Applies To:
Show Versions
BIG-IQ Centralized Management
- 5.3.0
About Access and SWG reports
Access reports focus on session and logging data from Access devices (managed devices with APM licensed and provisioned). F5® Secure Web Gateway Services reports focus on user requests (for URLs or applications, for example) from Access devices with Secure Web Gateway Services provisioned. BIG-IQ® Centralized Management Access also supports high availability. Thus, users can view both Access and SWG reports on a secondary BIG-IQ system.
Access reports and SWG reports provide the following features.
- Reports on any combination of discovered devices, Access groups, and clusters
- Graphs for typical areas of concern and interest, such as cross-geographical comparisons or top 10 issues
- Tabular data to support the graphs
- Ability in some screens to drill down from summarized data to details
- Ability to save data to CSV files
Setup requirements for Access and SWG reports
Before you can produce Access reports and SWG reports, you must ensure that these tasks are already complete.
- Set up the BIG-IQ® Centralized Management data collection devices.
- Add the BIG-IP® devices to BIG-IQ inventory.
- Discover the devices. (Devices with the Access service configuration are what you need.)
- Run the data collection device configuration setup on the devices from the Access Reporting screen.
What data goes into Access reports for the All Devices option?
The All Devices option for Access reports includes data from the devices that are currently managed (discovered) in the BIG-IQ® system. This is in addition to data from devices that were managed at some point during the report timeframe, but that are not currently managed. With All Devices selected, if data from unmanaged devices exists, it displays in reports.
An unmanaged device might be unmanaged temporarily or permanently. Any time a configuration management change causes APM® to be undiscovered, the device and its data are moved to All Devices until APM is re-discovered on the device.
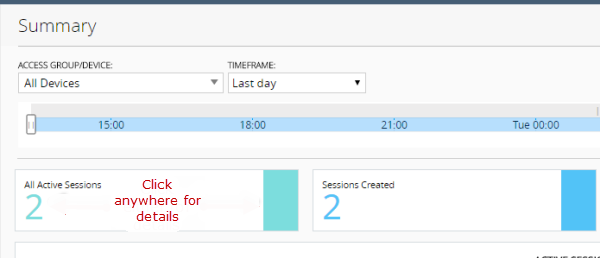
You cannot generate a report for an unmanaged device. However, you can generate a report for the timeframe when the device was managed, and then search the report for the unmanaged device name. In the Summary report, All Active Sessions includes the number of sessions that were active on the device when it became unmanaged. Those sessions stay in the Summary and in the Active sessions reports until the next session status update, which occurs every 15 minutes.
About upgrades affecting reports
When you upgrade a BIG-IQ® Centralized Management system without taking a snapshot, it deletes all reporting data, including both Access and SWG reports. After upgrading, users cannot obtain these reports from the BIG-IP® devices. To prevent the lost of reports, users should take an Elasticsearch snapshot before upgrading, and restore the snapshot after upgrading. For more information on elasticsnapshots, refer to F5 BIG-IQ Centralized Management: Upgrading Logging Nodes to Version x.x.
About the application dashboard
The Application Summary dashboard is your starting point to view and download general reports for BIG-IQ Access.
View the Application Summary dashboard
- Log in to the BIG-IQ system with your user name and password.
- At the top of the screen, click Monitoring.
- On the left, select .
About user visibility
You can monitor your user base by viewing the BIG-IQ® Centralized Management Access user dashboard for data on specific users. The system displays which users created the most sessions, were denied the most sessions, and had the longest total session duration. The administrator can enter a specific user name to get the following details for the user:
- The user login locations on a world map
- The total sessions, denied sessions, and session duration
- The Access denied sessions.
- The top authentication failures, including AD Auth and LDAP only
- The device type users used to log into the system
- The reason the system terminated the session
- The login history showing the success and failures over time
- The most accessed applications
- The most accessed URLs
- The login failure attempts over time, sorted by the reason
- The client session duration over time
- The Access denied reason over time
About application visibility
You can monitor your applications by viewing the BIG-IQ® Centralized Management Access user dashboard for data on which applications are linked to the BIG-IQ Access component. The system displays the top applications used and the application usage time. Administrators can expand the GUI for a specific application and view the following information:
- The application access history
- The users who use the application the most
- The access history
- The world map, showing where the user is access the application
About denied sessions
You can monitor the sessions that BIG-IQ® Centralized Management denies. By using the Access Monitoring option, you can view the following information:
- The history of denied sessions
- The reasons why sessions were denied
- The top denied users, sorted by session count
- The top authentication failures
- The top denied policies
- The top denied sessions by country of origin
- The top denied session by the virtual server
- The denied sessions, sorted by the client platform
Viewing denied sessions
Overview: About the BIG-IP configuration for BIG-IQ application visibility
The F5® BIG-IQ® Centralized Management Application Summary dashboard displays statistics for applications and users that are managed by the BIG-IP® system. This includes the most requested applications, and how often individual users access the applications. For example, as an administrator, you can see the application summary report for the SharePoint application managed by the BIG-IQ system. You can use the report to track usage statistics, such as the request count for SharePoint and the most frequent users by request count. You can also adjust the time slider to see statistics for a certain time period.
- Basic
- A Basic configuration is your starting point to configure the BIG-IP system for application visibility. In some cases, you only need this option to generate the application logs and send them to the BIG-IQ system.
- Advanced
- In an Advanced configuration, after you configure a basic configuration and validate the reports, you might need to configure more BIG-IP resources such as classification presets and profiles. This situation typically occurs if there is not a predefined classification profile in the application that you want to display statistics and reports in.
Before you begin configuring application visibility, refer to Access Reporting and Statistics, in the F5® BIG-IQ® Centralized Management: Monitoring and Reports guide.
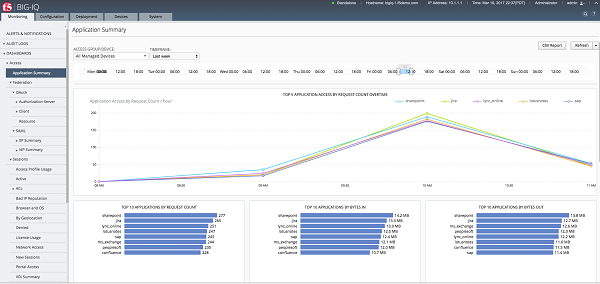
Sample Application Summary dashboard
Notice the length of time displayed by the line graph, dictated by the time slider above. Also notice the top ten applications, with SharePoint at number one. You can select an application and view the usage over time and the top users for that application.
View the Application Summary dashboard
- Log in to the BIG-IQ system with your user name and password.
- At the top of the screen, click Monitoring.
- On the left, select .
What is a basic configuration?
The basic BIG-IP® system configuration for BIG-IQ® application visibility is when a classification profile is already available to the administrator. This situation occurs when you want to track predefined access applications in BIG-IQ, such as SharePoint, OWA, PeopleSoft, or Lotus Notes. When you configure the virtual server for one or more of these applications, the BIG-IP system has already configured a classification profile. For most other applications, this basic configuration does not apply, and you must create the classification profile as well as other necessary resources.
In some cases, you might want to define your own signatures. If so, even in a basic configuration, you must upload the signatures in Traffic Intelligence.
- Enable remote logging in the Access area of BIG-IQ. Refer to the "BIG-IQ Centralized Management: Access" manual to learn how to configure remote logging.
- Update classification signatures in BIG-IP Traffic Intelligence.
- Configure a virtual server in BIG-IP Local Traffic.
- Attach an existing classification profile to the virtual server.
About traffic signatures for application visibility
Classification signatures define different types of traffic that the BIG-IP® system can recognize through Traffic Intelligence. The system recognizes a predefined set of signatures for common applications and application categories that are updated periodically. You can download signature updates from F5 Networks, and schedule the system to automatically update the signatures (pull the updated signatures automatically). You can also manually install the classification signatures and updates, for example, if the BIG-IP system does not have Internet access.
- Set up the DNS server on the BIG-IP system in order for the automatic updates to work.
- The management network should be on the Internet.
Scheduling automatic signature updates
Modify the virtual server for a basic configuration
What is an advanced configuration?
If you want to display statistics and reports using the Access feature of BIG-IQ® in an application that does not have a predefined classification profile, you must create the classification profile and attach it to the virtual server. This is considered an advanced configuration, and applies to most applications.
- Enable remote logging in BIG-IQ Access. Refer to the BIG-IQ Centralized Management: Access manual to learn how to configure remote logging.
- Create a classification policy in BIG-IP system Traffic Intelligence screens.
- Create a new application from the Traffic Intelligence application list by customizing a category.
- Update the existing classification preset or create a new preset.
- Create a classification profile in the BIG-IP system's Local Traffic settings if you created a new classification preset. Otherwise, update the existing classification profile to include the existing preset.
- Configure a virtual server in the BIG-IP system's Local Traffic settings.
Creating a custom local traffic policy
Creating a category
Create a classification application
About presets and profiles
In BIG-IQ® application visibility, as part of the advanced configuration, there are two ways to configure the BIG-IP® classification preset and classification profile.
- You can use the existing classification preset, and make sure it is associated with the current classification profile.
- You can create a new classification preset, but you must also associate it with a new classification profile.
Updating classification presets
Updating a classification profile
Creating classification presets
Creating a classification profile
Modify the virtual server for an advanced configuration
How much memory does application visibility need?
In the BIG-IP® system configuration for BIG-IQ® application tracking reporting, you do not need to allocate separate memory resources to enable the application visibility functionality. The runtime memory consumption depends on the amount of traffic processed, such as concurrent TCP flows.
Application visibility troubleshooting commands
Type these commands in the BIG-IP® UNIX shell to start and stop debugging and logging.
| Command | Description |
|---|---|
| tmctl gpa_classification_stats | Displays classification results in a table that lists all applications that were classified, the number of flows, the bytes in, and the bytes out. |
|
tmsh modify sys db tmm.cec.log.level value Debug tmsh modify sys db tmm.gpa.log.level value Debug |
Generates debug logs. The log messages are stored in /var/log/tmm. |
|
tmsh modify sys db tmm.cec.log.level reset-to-default tmsh modify sys db tmm.gpa.log.level reset-to-default |
Stops debug log messages. |
Managing a specific user in Access reporting
Running Access reports
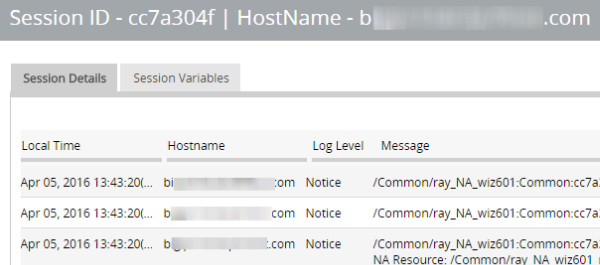
Getting the details that underlie an Access report
About the maximum number records for Access and SWG reports
When you run an Access report or an SWG report, Access can get up to 10,000 records to display to you. After you scroll to the end of those 10,000 records, Access displays a message. At that point, all you can do is select fewer devices or select a shorter timeframe.
Setting the timeframe for your Access or SWG report
- Log in to BIG-IQ Centralized Management with your admin user name and password.
- At the top of the screen, click Monitoring.
- To set a predefined timeframe, select one of these from the TIMEFRAME list: Last hour, Last day, Last week, Last 30 days, Last 3 months.
-
To set a custom timeframe, select one of these from
theTIMEFRAME list:
- Between: Click each of the additional fields that display to select dates and times. The report displays the records between those dates and times.
- Before: Click the additional fields that display to select a date and a time. The report displays the records before that date and time.
- After: Click the additional fields that display to select a date and a time. The report displays the records after that date and time.
Access report problems: causes and resolutions
| Problem | Resolution |
|---|---|
| A session is over, but it continues to display in the Active sessions report. | If a session starts when logging nodes are up and working, but terminates during a period when logging modes are unavailable, the session remains in the Active sessions report for 15 minutes. After 15 minutes, the session status is updated and the session is dropped from the report. |
| Active sessions are included in the Summary and Active sessions reports for a device that is no longer managed. | Sessions were active on a device when it was removed from an Access group and became unmanaged. Sessions that were active when the device became unmanaged remain counted in All Active Sessions on the Summary screen and stay in the Active sessions report until the next session status update, which occurs every 15 minutes. |
| A session is over, but Session Termination and Session Duration are blank in a session report. | If a session starts when logging nodes are up and working but terminates during a period when logging nodes are unavailable, the session termination is not recorded and the session duration cannot be calculated. |
What can cause logging nodes to become unavailable?
Logging nodes are highly available, but it is still possible for them to become unavailable. This could occur, for example, if all logging nodes are on devices in the same rack in a lab, and the power to the lab shuts down.
Sessions
Running Session reports
Stopping sessions on BIG-IP devices from Access
Running Secure Web Gateway reports
Getting the details that underlie an SWG report
About VDI reports
- The top 10 VDI applications
- The top users for the VDI applications
- The application usage history
Federation
Running OAuth reports
Running SAML reports
About Application Summary and traffic signatures
In BIG-IQ Access, to view the Sharepoint and OWA application names in the Application dashboard correctly, update the classification signatures on the BIG-IP device. You can also customize your traffic signature by creating a custom signature.
Overview: Updating classification signatures
Classification signatures define different types of traffic that Policy Enforcement Manager™ (PEM) can recognize, through Traffic Intelligence™. PEM™ recognizes a predefined set of signatures for common applications and application categories that are updated periodically. You can download signature updates from F5 Networks, and schedule the system to automatically update the signatures. You can also manually install the classification signatures and updates, for example, if the BIG-IP® system does not have Internet access.
Task Summary
Scheduling automatic signature updates
Overview: Creating custom classifications
Traffic Intelligence analyzes and identifies higher level protocols and applications. It has the ability to detect applications and protocols in Service Provider networks, for example, HTTP, popular P2P, and top categories (Audio/Video, File Transfer, Instant Messaging, Mail, P2P, Web). It provides an application update mechanism, which in turn, provides the ability to keep up with new, modified, or obsolete applications without going through software release upgrades. IP traffic classifications are based on the IP protocol field of the IP header (IANA protocol).
Task summary
Determining and adjusting traffic classifications
Creating a category
Creating classification presets
Creating a custom URL database
Using iRules with classification categories and applications
Modifying iRule event for URL categories
Classification iRule commands
When the BIG-IP® system identifies a specific type of traffic with iRules® enabled, it triggers a CLASSIFICATION_DETECTED event. You can use the commands within iRules for additional system flexibility to classify the flow as one or more of the application or category classifications. The CLASSIFY commands are available from the HTTP_REQUEST or HTTP_RESPONSE iRule events.
| iRule Command | Description |
|---|---|
| CLASSIFICATION::app | Gets the name of the classified application (the most explicit classified application). |
| CLASSIFICATION::category | Gets the category of the application. |
| CLASSIFICATION::disable | Disables the classification for a flow. |
| CLASSIFICATION::enable | Enables the classification for a flow. |
| CLASSIFICATION::protocol | Gets the name of the classified protocol (the least explicit classified application). |
| CLASSIFY::application set appname | Classifies the flow as appname and associates the category that appname belongs to. |
| CLASSIFY::category set catname | Classifies the flow as catname and also associates the flow with the unknown category. |
| CLASSIFY::application add appname | Adds the application appname to the classification statistics. |
| CLASSIFY::category add catname | Adds the category catname to the classification statistics. |