Applies To:
Show Versions
BIG-IP AAM
- 11.6.5, 11.6.4, 11.6.3, 11.6.2, 11.6.1
BIG-IP APM
- 11.6.5, 11.6.4, 11.6.3, 11.6.2, 11.6.1
BIG-IP GTM
- 11.6.5, 11.6.4, 11.6.3, 11.6.2, 11.6.1
BIG-IP Analytics
- 11.6.5, 11.6.4, 11.6.3, 11.6.2, 11.6.1
BIG-IP Link Controller
- 11.6.5, 11.6.4, 11.6.3, 11.6.2, 11.6.1
BIG-IP LTM
- 11.6.5, 11.6.4, 11.6.3, 11.6.2, 11.6.1
BIG-IP PEM
- 11.6.5, 11.6.4, 11.6.3, 11.6.2, 11.6.1
BIG-IP AFM
- 11.6.5, 11.6.4, 11.6.3, 11.6.2, 11.6.1
BIG-IP ASM
- 11.6.5, 11.6.4, 11.6.3, 11.6.2, 11.6.1
Overview: Managing client and server HTTP traffic using a self-signed certificate
One of the ways to configure the BIG-IP system to manage SSL traffic is to enable both client-side and server-side SSL processing:
- Client-side SSL termination makes it possible for the system to decrypt client requests before sending them on to a server, and encrypt server responses before sending them back to the client. This ensures that client-side HTTP traffic is encrypted. In this case, you need to install only one SSL key/certificate pair on the BIG-IP system.
- Server-side SSL termination makes it possible for the system to decrypt and then re-encrypt client requests before sending them on to a server. Server-side SSL termination also decrypts server responses and then re-encrypts them before sending them back to the client. This ensures security for both client- and server-side HTTP traffic. In this case, you need to install two SSL key/certificate pairs on the BIG-IP system. The system uses the first certificate/key pair to authenticate the client, and uses the second pair to request authentication from the server.
This implementation uses a self-signed certificate to authenticate HTTP traffic.
Task summary
To implement client-side and server-side authentication using HTTP and SSL with a self-signed certificate, you perform a few basic configuration tasks.
Task list
Creating a self-signed digital certificate
Creating a custom HTTP profile
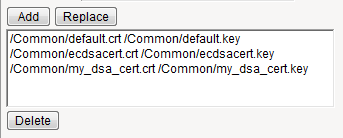
Creating a custom Client SSL profile
- Ciphers
- Client Certificate
- Frequency
- Certificate Chain Traversal Depth
- Certificate Revocation List (CRL)
- Trusted Certificate Authorities
- Advertised Certificate Authorities
Creating a custom Server SSL profile
Implementation results
After you complete the tasks in this implementation, the BIG-IP system ensures that SSL authentication and encryption occurs for both client-side and server-side HTTP traffic. The system performs this authentication and encryption according to the values you specify in the Client SSL and Server SSL profiles.