Applies To:
Show Versions
BIG-IP APM
- 12.0.0
Using APM as a Gateway for RDP Clients
Overview: Configuring APM as a gateway for Microsoft RDP clients
Access Policy Manager® (APM®) can act as a gateway for Microsoft RDP clients, authorizing them on initial access and authorizing access to resources that they request after that. The APM configuration includes these elements.
- APM as gateway
- From a configuration point of view, this is a virtual server that accepts SSL traffic from Microsoft RDP clients and is associated with an access policy that authorizes the client.
- Client authorization access policy
- This access policy runs when the RDP client initiates a session with the gateway (APM). Only NTLM authentication is supported. This access policy should verify that NTLM authentication is successful and must assign an additional access policy to use for resource authorization throughout the session.
- Resource authorization access policy
- This access policy runs when the authorized RDP client requests access to a resource. The access policy must contain logic to determine whether to allow or deny access to the target server and port.
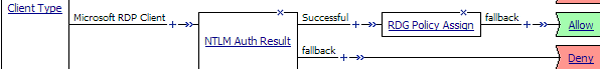
Sample client authorization policy
Notice the RDG Policy Assign item; it is used to specify the resource authorization policy.
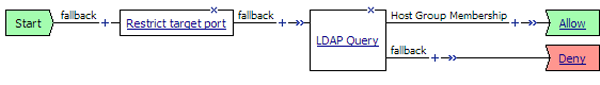
Sample resource authorization policy
Task summary
If you already have configured them, you can use existing configuration objects: a machine account, an NTLM authentication configuration, a VDI profile, a connectivity profile, and a client SSL profile.
Task list
About supported Microsoft RDP clients
Supported Microsoft RDP clients can use APM® as a gateway. The configuration supports Microsoft RDP clients on Windows, Mac, iOS, and Android.
Refer to BIG-IP® APM® Client Compatibility Matrix on the AskF5™ web site at http://support.f5.com/kb/en-us.html for the supported platforms and operating system versions for Microsoft RDP clients.
About Microsoft RDP client configuration
Before a supported Microsoft RDP client connects to Access Policy Manager® (APM®) as a gateway for RDP clients, installation of the BIG-IP®client SSL certificate (specified in the virtual server) is required.
About Microsoft RDP client login to APM
On a Microsoft RDP client, a user types in settings for a gateway and a connection. The names for the settings vary depending on the Microsoft RDP client.
- RDP client gateway settings
-
- Hostname setting: The hostname or IP address of the virtual server must be specified.
- Port setting: If requested, 443 must be specified.
- Credentials: Selection of specific logon method and entry of a user name and password should be avoided. In this implementation, APM® supports only NTLM authentication.
- RDP client connection settings
- Gateway setting: On some clients, you must configure a name and address for the gateway and
at login type the gateway name. If requested, the gateway name must be specified as configured
on the client.
- Hostname setting: Hostname of the target server.
- Port setting: Port on the target server.
Configuring an access profile for resource authorization
Verifying log settings for the access profile
Configuring an access policy for resource authorization
Creating an access profile for RDP client authorization
Verifying log settings for the access profile
Configuring an access policy for an RDP client
Configuring a machine account
Creating an NTLM Auth configuration
Maintaining a machine account
Configuring a VDI profile
Creating a connectivity profile
Creating a custom Client SSL profile
- Authenticating and decrypting ingress client-side SSL traffic
- Re-encrypting egress client-side traffic
Creating a virtual server for SSL traffic
Implementation result
Supported Microsoft RDP clients can specify a virtual server on the BIG-IP® system to use as a remote desktop gateway. Access Policy Manager® (APM®) can authorize the clients and authorize access to target servers as the clients request them.
Overview: Processing RDP traffic on a device with SWG
If you configure Access Policy Manager® APM® as a gateway for RDP clients and configure Secure Web Gateway (SWG) explicit forward proxy on the same BIG-IP® system, you need to complete an additional configuration step to ensure that APM can process the RDP client traffic. The recommended SWG configuration for explicit forward proxy includes a catch-all virtual server, which listens on all IP addresses and all ports, on an HTTP tunnel interface.
When a programmatic API queries listeners for a specific IP and port, the query covers all interfaces and tunnels. As a result, the catch-all virtual server will always match. Sending traffic using this tunnel results in all packets being dropped because this virtual server is configured as a reject type of virtual server.
To prevent RDP client traffic from being dropped, add an additional wildcard port-specific virtual server on the HTTP tunnel interface.
About wildcard virtual servers on the HTTP tunnel interface
In the recommended Secure Web Gateway explicit forward proxy configuration, client browsers point to a forward proxy server that establishes a tunnel for SSL traffic. Additional wildcard virtual servers listen on the HTTP tunnel interface. The listener that best matches the web traffic directed to the forward proxy server handles the traffic.
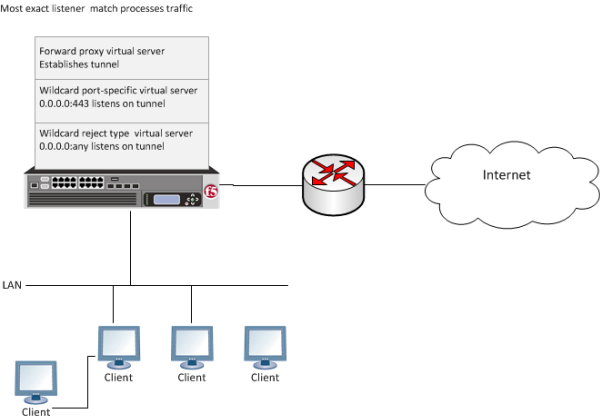
Explicit forward proxy configuration





