Applies To:
Show Versions
BIG-IP APM
- 12.1.6, 12.1.5, 12.1.4, 12.1.3, 12.1.2, 12.1.1, 12.1.0
User Identification
About user identification
Access Policy Manager® (APM®) Secure Web Gateway (SWG) identifies users and maps them to IP addresses, or to sessions, without using cookies. The methods that are available for identifying users depend on access profile type.
About session management cookies and Secure Web Gateway
Secure Web Gateway (SWG) does not use Access Policy Manager® (APM®) session management cookies. If presented with an APM session management cookie, SWG ignores it.
About user identification with NTLM authentication
User identification by credentials is a method that is available for the SWG-Explicit access profile type. To support this option, an NTLM Auth Configuration object must be specified in the access profile and the result of NTLM authentication can be verified in the access policy.
For user identification by credentials, Secure Web Gateway (SWG) maintains an internal mapping of credentials to sessions.
About user identification with a logon page
User identification by IP address is a method that is available for these access profile types: SWG-Explicit, SWG-Transparent, and LTM-APM.
To support this option, a logon page must be added to the access policy to explicitly identify users. The logon page requests user credentials and validates them to identify the users. For explicit forward proxy, a 407 response page is the appropriate logon page action. For transparent forward proxy, a 401 response page is the appropriate logon page action. For LTM-APM, the Logon Page action is appropriate.
Secure Web Gateway (SWG) maintains an internal mapping of IP addresses to user names.
About user identification with an F5 agent
Transparent user identification makes a best effort to identify users without requesting credentials. It is not authentication. It should be used only when you are comfortable accepting a best effort at user identification.
Transparent user identification is supported in Secure Web Gateway (SWG) configurations for either explicit or transparent forward proxy. An agent obtains data and stores a mapping of IP addresses to user names in an IF-MAP server. An F5® DC Agent queries domain controllers. An F5 Logon Agent runs a script when a client logs in and can be configured to run a script when the client logs out.
In an access policy, a Transparent Identity Import item obtains the IP-address-to-username-mapping from the IF-MAP server. This item can be used alone for determining whether to grant access or be paired with another query to look up the user or validate user information.
To support this option, either the F5 DC Agent or the F5 Logon Agent must be downloaded, installed, and configured.
Overview: Configuring F5 DC Agent
The F5® DC Agent enables transparent user identification, a best effort to identify users without requesting credentials.
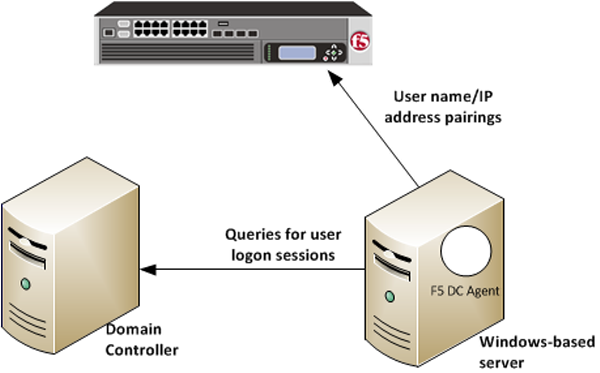
How F5 DC Agent transparently identifies users
You can install the F5® DC Agent on a Windows-based server in any domain in the network. The F5 DC Agent discovers domains and domain controllers, queries the domain controllers for logon sessions, and sends an IP-address-to-user-name mapping to the BIG-IP® system. F5 DC Agent sends only those new user name and IP address pairs recorded since the previous query. The BIG-IP system maintains user identity information in an IF-MAP server and stores only the most recently identified user name for a given IP address.
Considerations for installing multiple agents
You can install more than one F5 DC Agent in your network and configure F5 DC Agents to communicate with the same BIG-IP system.
- NetBIOS port 139
- F5 DC Agent uses NetBIOS port 139 for automatic domain detection. If NetBIOS port 139 is blocked in your network, you can deploy an F5 DC Agent instance for each virtually or physically remote domain.
- Multiple subnets
- As a best practice, install a separate F5 DC Agent in each subnet to avoid problems gathering logon information from domain controllers.
- Network size, disk space, and RAM
- If your network is very large (10,000+ users or 30+ domain controllers), you might benefit from installing F5 DC Agent on multiple machines to evenly distribute resource usage. F5 DC Agent uses TCP to transmit data, and transmits roughly 80 bytes per user name and IP address pair.
| Number of users | Average amount of data transferred per day |
|---|---|
| 250 users | 30 KB |
| 2,000 users | 240 KB |
| 10,000 users | 1200 KB |
Task summary
Configuring the BIG-IP system for the F5 DC Agent
Verifying network communication
Downloading and installing F5 DC Agent
Updating privileges for the F5 DC Agent service
-
On the Windows-based server, create a user account for F5 DC Agent:
-
Configure the F5 DC Agent service to log on as the user account you just
configured:
Configuring the initialization file
Configuring domain controller polling in the dc_agent.txt file
Recovering from an unsuccessful installation
- Log on to the Windows-based server from a user account with local and domain administrator privilege.
- From the Windows Programs and Features dialog box, uninstall the F5 Installer application.
- From Windows Explorer, click the SWGUserIdentificationAgents.exe file and follow the instructions to install F5 DC Agent again.
Enabling debug logging for the F5 DC Agent
Troubleshooting when a user is identified incorrectly
- Log on to the client system that belongs to the user.
- Open a browser and navigate to four or more distinctive web sites.
- Log on to the Windows-based server where the F5® DC Agent is installed.
- Look for error messages in the Windows Event Viewer.
- Proceed based on any error messages that you discover.
F5 DC Agent error messages
Error messages from the F5® DC Agent display in the Event Viewer on the Windows-based server where DC Agent is installed.
| Error code | Error message | Possible causes |
|---|---|---|
| 3 | Could not configure DC Agent (Code 3) | An attempt was made to install F5 DC Agent using an account that does not have domain and local administrator privileges. As a result, some required files are not installed properly, and F5 DC Agent service cannot run. |
| 5 | ERROR_ACCESS_DENIED | F5 DC Agent service does not have sufficient permissions to perform required
tasks. This error can occur when:
|
| 53 | ERROR_BAD_NETPATH | A network problem prevents F5 DC Agent from contacting a domain controller. This
error can occur when:
|
| 71 |
System error while enumerating the domain controllers. domain: (****)ecode: 71 : message: No more connections can be made to this remote computer at this time because there are already as many connections as the computer can accept. |
The error results from F5 DC Agent automatic domain discovery process, used to identify new domains and domain controllers. It can also occur when F5 DC Agent tries to connect to a Windows XP-based computer that is broadcasting itself as the master browser for a non-company domain or workgroup. Although the issue might indicate a problem with connectivity to the domain controller, it is more likely that the domain is a workgroup with no domain controllers. This error can be ignored. |
| 997 | Error Code 997 | An attempt was made to install F5 DC Agent using an account that does not have domain and local administrator privileges. As a result, some required files are not installed properly, and F5 DC Agent service cannot run. |
| 1058 | Error Code 1058 | This error is seen on startup. A Local Security Policy on the Windows-based server might have disabled the F5 DC Agent service. |
Overview: Configuring F5 Logon Agent
The F5® Logon Agent enables transparent user identification, a best effort to identify users without requesting credentials.
You can install the F5 Logon Agent on a Windows-based server in any domain in the network. The F5 Logon Agent identifies users in real time when the users log on to domains, which prevents missing a user logon because of a query timing issue. F5 Logon Agent sends up-to-date session information to the BIG-IP® system.
F5 Logon Agent identification process
- When users log on to the network, a network logon script invokes the logon application (LogonApp.exe).
- The logon application contacts F5 Logon Agent using HTTP.
- F5 Logon Agent sends an NTLM authentication challenge, and the logon application provides a user name, hashed password, and IP address to F5 Logon Agent.
- F5 Logon Agent verifies the username and password combination from the logon application by establishing a session with the domain controller. (F5 Logon Agent contacts User Service to determine which domain controller is the logon source.)
- After verifying the user name and IP address pair, F5 Logon Agent sends the information to the BIG-IP system and adds an entry to its user map in local memory. The user map is periodically saved to a backup file, AuthServer.bak.
- The BIG-IP system records user name and IP address pairs to the BIG-IP system copy of the user map in local memory. Confidential information (such as user passwords) is not sent to the BIG-IP system.
Considerations for installing multiple agents
You can install more than one F5 Logon Agent in your network, and configure F5 Logon Agents to communicate with the same BIG-IP system. If you have multiple BIG-IP systems, each BIG-IP system must be able to communicate with every F5 Logon Agent in your network.
- NetBIOS port 139
- F5 Logon Agent uses NetBIOS port 139 for automatic domain detection. If NetBIOS port 139 is blocked in your network, you can deploy an F5 Logon Agent instance for each virtually or physically remote domain.
- Multiple subnets
- As a best practice, install a separate F5 Logon Agent in each subnet to avoid problems gathering logon information from domain controllers.
- Network size, disk space, and RAM
- If your network is very large (10,000+ users or 30+ domain controllers), you might benefit from installing F5 Logon Agent on multiple machines to evenly distribute resource usage.
Task summary
Configuring the BIG-IP system for the F5 Logon Agent
Verifying network communication
Downloading and installing F5 Logon Agent
Updating privileges for the F5 Logon Agent service
-
On the Windows-based server, create a user account for F5 Logon Agent:
-
Configure the F5 Logon Agent service to log on as the user account you just
configured:
Configuring the initialization file
Recovering from an unsuccessful installation
- Log on to the Windows-based server from a user account with local and domain administrator privilege.
- From the Windows Programs and Features dialog box, uninstall the F5 Installer application.
- From Windows Explorer, click the SWGUserIdentificationAgents.exe file and follow the instructions to install F5 Logon Agent again.
Enabling debug logging for the F5 Logon Agent
Troubleshooting when a user is identified incorrectly
- Log on to the client system that belongs to the user.
- Open a browser and navigate to four or more distinctive web sites.
- Log on to the Windows-based server where the F5® Logon Agent is installed.
- Look for error messages in the Windows Event Viewer.
- Proceed based on any error messages that you discover.
Files used by Logon Agent
This table explains the relevant files used by F5® Logon Agent after you install the installation file from the BIG-IP® system Configuration utility Welcome screen.
| Filename | File location | Additional information |
|---|---|---|
| LogonApp.exe | Stored in User Identity Agents > LogonApp > Windows folder. | Sends user information to F5 Logon Agent. Captures user logon sessions as they occur. Runs on Windows client machines. |
| logon.bat | Stored in User Identity Agents > LogonApp > Windows folder. | Invokes LogonApp.exe, which runs on client machines and captures logon sessions. |
| AuthServer.ini | Stored in User Identity Agents > config folder. | Contains one initialization parameter for Logon Agent. |
Overview: Creating a script on a Windows system for F5 Logon Agent
When you install the F5® Logon Agent, you must create a logon script for clients that identify the clients to the BIG-IP® system when they log on to a Windows domain. The application, LogonApp.exe, provides a username and IP address to F5 Logon Agent each time a Windows client connects to a Windows Active Directory or a Windows NT directory service.
When installing F5 Logon Agent, the following files are placed in the F5 Networks folder (by default, C:\Program Files\F5 Networks\User Identity Agents\LogonApp):
- LogonApp.exe
- logon.bat
Task summary
Creating a logon or logout script
Running a logon or logout script on Active Directory
Logon and logout script parameters
This table explains the relevant parameters used by a logon or logout script for F5® Logon Agent.
| Parameter | Description |
|---|---|
| <server> | The IP address of the BIG-IP® system F5 Logon Agent. |
| <port> | The port number used by F5 Logon Agent. The default value is 15880. |
| /NOPERSIST |
|
| /COPY | Copies the logon application to the %USERPROFILE%\Local Settings\Temp directory on the user machine, where the logon script runs it from the local memory. This optional parameter helps prevent your logon script from hanging. COPY can be used only in persistent mode. |
| /VERBOSE | A debugging parameter that can be used only with help from technical support. |
| /LOGOUT | Used only in an optional logout script, this parameter removes the user's logon information from the F5 Logon Agent user map when the user logs off. If you use Active Directory, this parameter can clear the logon information from the user map before the interval that is defined for F5 Logon Agent has elapsed. Use this optional parameter in a logout script in a batch file that is different than the one containing the logon script. The following example logout script clears the logon information for each user as soon as the user logs out. LogonApp.exe http://10.2.2.95:15880 /NOPERSIST /LOGOUT |





