Applies To:
Show Versions
BIG-IP APM
- 13.1.5, 13.1.4, 13.1.3, 13.1.1, 13.1.0
Overview: Configuring remote high-speed APM and SWG event logging
You can configure the BIG-IP® system to log information about Access Policy Manager® (APM® ) and Secure Web Gateway events and send the log messages to remote high-speed log servers.
When configuring remote high-speed logging of events, it is helpful to understand the objects you need to create and why, as described here:
| Object | Reason |
|---|---|
| Pool of remote log servers | Create a pool of remote log servers to which the BIG-IP system can send log messages. |
| Destination (unformatted) | Create a log destination of Remote High-Speed Log type that specifies a pool of remote log servers. |
| Destination (formatted) | If your remote log servers are the ArcSight, Splunk, or Remote Syslog type, create an additional log destination to format the logs in the required format and forward the logs to a remote high-speed log destination. |
| Publisher | Create a log publisher to send logs to a set of specified log destinations. |
| Log Setting | Add event logging for the APM system and configure log levels for it or add logging for URL filter events, or both. Settings include the specification of up to two log publishers: one for access system logging and one for URL request logging. |
| Access profile | Add log settings to the access profile. The log settings for the access profile control logging for the traffic that comes through the virtual server to which the access profile is assigned. |
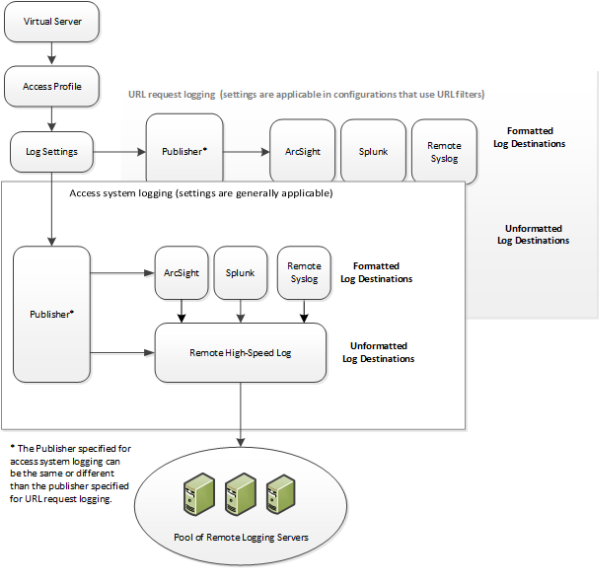
Association of remote high-speed logging configuration objects
Task summary
Perform these tasks to configure remote high-speed APM and SWG event logging on the BIG-IP system.Task list
About the default-log-setting
Access Policy Manager® (APM®) provides a default-log-setting. When you create an access profile, the default-log-setting is automatically assigned to it. The default-log-setting can be retained, removed, or replaced for the access profile. The default-log-setting is applied to user sessions only when it is assigned to an access profile.
Regardless of whether it is assigned to an access profile, the default-log-setting applies to APM processes that run outside of a user session. Specifically, on a BIG-IP® system with an SWG subscription, the default-log-setting applies to URL database updates.
Creating a pool of remote logging servers
Creating a remote high-speed log destination
Create a log destination of the Remote High-Speed Log type to specify that log messages are sent to a pool of remote log servers.
Creating a formatted remote high-speed log destination
Create a formatted logging destination to specify that log messages are sent to a pool of remote log servers, such as Remote Syslog, Splunk, or ArcSight servers.
Creating a publisher
Configuring log settings for access system and URL request events
Disabling logging
About event log levels
Event log levels are incremental, ranging from most severe (Emergency) to least severe (Debug). Setting an event log level to Warning for example, causes logging to occur for warning events, in addition to events for more severe log levels. The possible log levels, in order from highest to lowest severity are:
- Emergency
- Alert
- Critical
- Error
- Warning
- Notice (the default log level)
- Informational
- Debug





