Applies To:
Show Versions
BIG-IP APM
- 13.0.1, 13.0.0
APM OAuth 2.0 support
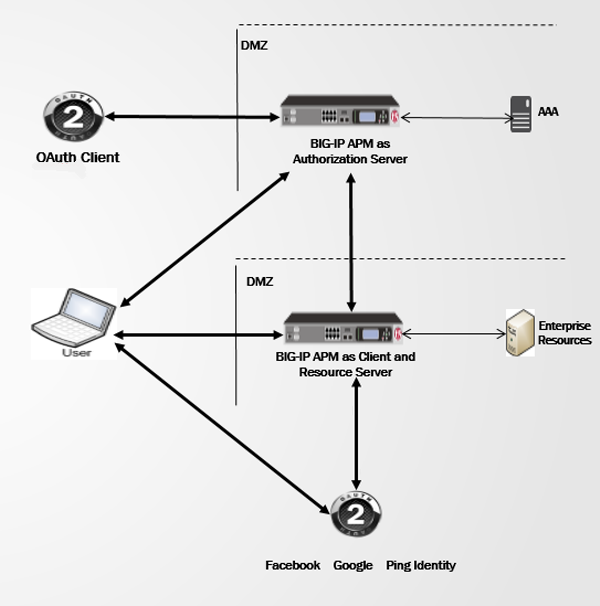
APM in OAuth roles in the network
OAuth roles that APM supports
On a single BIG-IP® system, Access Policy Manager® (APM®) can be configured to act as an OAuth 2.0 client and resource server, or to act as an OAuth 2.0 authorization server.
OAuth 2.0 roles
OAuth 2.0 specification RFC 6749 defines the roles in this table.
| OAuth role | Description |
|---|---|
| resource owner | Can grant access to a protected resource. A resource owner can be an end-user (person) or another entity. |
| resource server | Hosts protected resources, and can accept and respond to requests for protected resources using access tokens. |
| client | Makes requests for protected resources on behalf of, and with authorization from, the resource owner. The client is an application. |
| authorization server | Issues access tokens to the client after successfully authenticating the resource owner and obtaining authorization. |
APM in OAuth resource server and client roles
When Access Policy Manager® (APM®) acts as an OAuth resource server, users can log on using external OAuth accounts to gain access to the resources that APM protects. External OAuth accounts can be social accounts, such as Facebook and Google, or enterprise accounts, such as F5 (APM) and Ping Identity (PingFederate).
In this configuration, APM becomes a client application to an external OAuth authorization server, such as F5, on another BIG-IP® system, or Google.
APM in the OAuth authorization server role
When Access Policy Manager® (APM®) acts as an OAuth authorization server, APM can grant authorization codes, access tokens, and refresh tokens, and APM can perform token introspection.





