Applies To:
Show Versions
BIG-IP APM
- 13.0.1, 13.0.0
What is step-up authentication?
With step-up authentication, you can authenticate a user at any time during a session.
Use cases for step-up authentication
Step-up authentication can be used to protect layers or parts of a web application that manage more sensitive data. It can be used to increase protection by requiring stronger authentication within an already authenticated access to the web application. Step-up authentication can be a part of using the portal access or web application management (reverse proxy) features of Access Policy Manager® (APM®).
Concepts to know for building step-up authentication policies
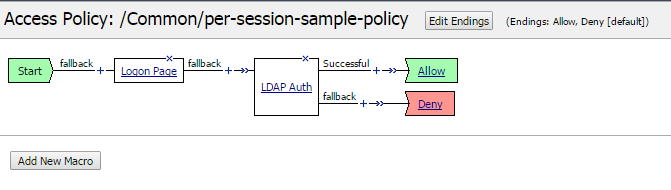
- Per-session policy
- Runs once. Associated with an access profile, which specifies a session lifetime. Can be
used to validate that a client satisfies corporate policy, establish user identity,
establish policy behavior, and allow or deny access to a virtual server and the resources
it protects. Establishes a session. Required.
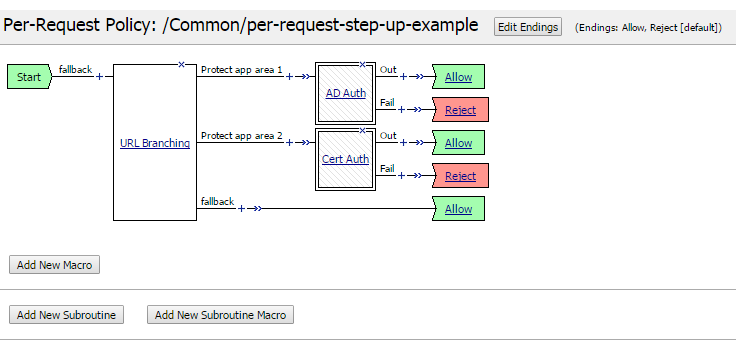
- Per-request policy
- Runs each time the client makes an HTTP or HTTPS request during a session. Can be used
to determine whether to request step-up authentication, and to allow or reject a request.
The purpose of this policy is to control access to the requested resource.
Required.
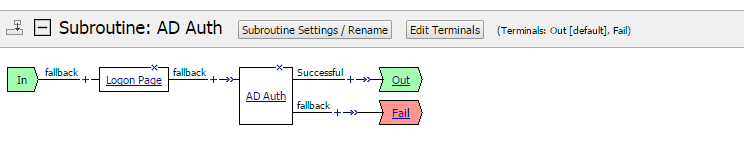
- Per-request policy subroutine
- A special macro that can handle client interactions. Represents the step-up
authentication policy. Establishes a subsession. Runs when no active subsession matches
the expected identifying characteristics (subroutine name and any gating criteria). While
a matching subsession exists, the subroutine does not run again; the user retains access
to the resource and need not authenticate again. Required.
- Subroutine settings
- Specifies subsession lifetime; a loop count, which can be used if authentication retry
is needed; gating criteria; and other timeout values. Default values for these settings
are provided when you configure a per-request policy subroutine; you can retain those
values or change them.
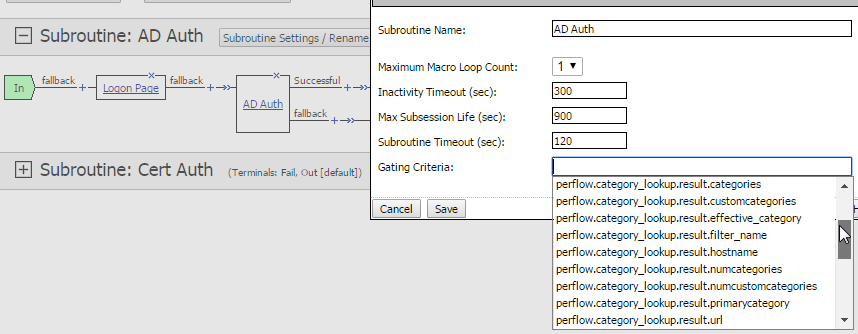
- Gating criteria
- A subroutine setting. Specifies a criteria to distinguish subsessions. A distinct subsession is created for each distinct gating criteria value. Gating criteria can be blank (one value) or can be set to a perflow variable (more than one possible value). The default value is blank.
- perflow.scratchpad and perflow.custom
- Pre-defined custom variables. These are the only custom variables that can be used in a per-request policy or its components (macro, subroutine, subroutine macro). Use of these variables is optional.
- Subsession
-
Starts when a subroutine runs and continues until reaching its maximum lifetime (a subroutine setting), or until the session terminates. Does not count against license limits. Populates subsession variables that persist throughout the subsession. Supports logging. Multiple subsessions can exist at the same time, up to a limit of 128 per access session. (When the 129th session is created, the first subsession is removed.)
- Per-request policy subroutine macro
- Groups agents. Keeps policy display clean and simple. Optional.
How step-up authentication works
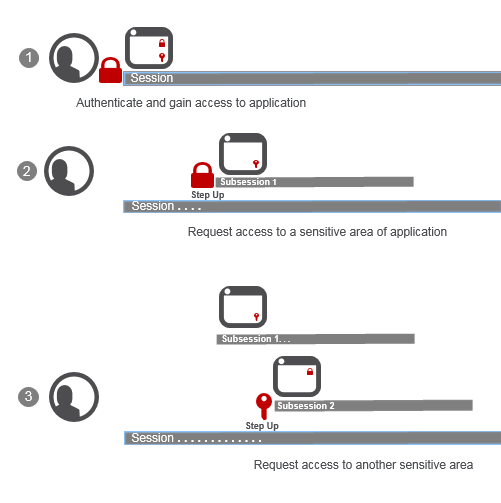
| 1 | User logs in and authenticates through an access policy (per-session policy); Access Policy Manager® (APM®) creates a session. User
starts to use an application that's available in the enterprise. User can access all but two
parts of the application that APM protects with step-up authentication, which requires:
|
| 2 | User requests access to part of the application protected with step-up authentication (username and password). APM challenges the user and then starts a subsession; for simplicity, we call it Subsession 1. For the duration of Subsession 1: If the user passed step-up authentication, the user does not need to authenticate again to access that part of the application; If the user failed step-up authentication, the user does not have access and step-up authentication does not run again. |
| 3 | User requests access to part of the application protected with step-up authentication
certificate authentication. APM challenges the user and then starts another subsession,
Subsession 2. If the user passes certificate authentication, for the duration of Subsession
2: If the user passed step-up authentication, the user does not need to authenticate again to
access that part of the application; If the user failed step-up authentication, the user does
not have access and step-up authentication does not run again.
Tip: A subsession ends when its
lifetime expires or when the session ends, whichever is sooner.
|
Authentication types APM supports for step-up authentication
Access Policy Manager® (APM®) supports these authentication types for step-up authentication:
- Multi-factor authentication through RADIUS authentication
- APM supports multi-factor authentication providers, such as DUO Security and RSA SecurID, when they are integrated with RADIUS.
- Certificate-based authentication
-
- On-Demand certificate authentication - APM re-negotiates the SSL connection, requesting and validating the certificate.
- CRLDP - When coupled with on-demand certificate authentication, Certificate Revocation List Distribution Point (CRLDP) authentication verifies that the certificate is still valid.
- OCSP - When coupled with on-demand certificate authentication, Online Certificate Status Protocol (OCSP) authentication verifies the certificate is still valid.
Example: Step-up authentication at the application layer
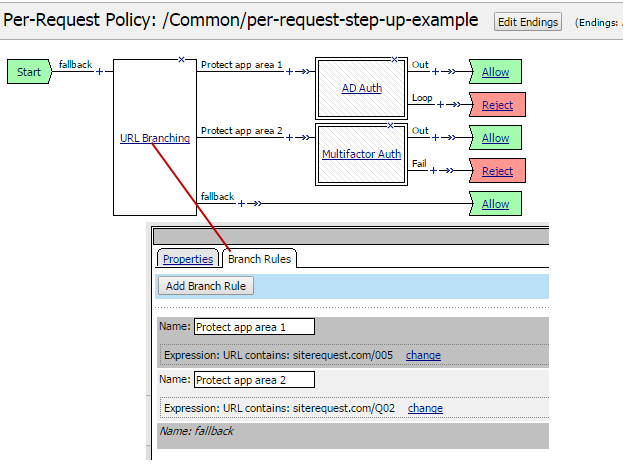
One way to identify an application or some part of an application that you want to protect is by using the URL Branching agent in a per-request policy to specify a URI and branch on it.
Example: Determining to step up for an application layer
In this example, the URL Branching agent matches substrings that indicate requests to sensitive areas of a web application named siterequest. Matching requests are protected with Active Directory or multi-factor step-up authentication.
Example: Stepping up with Active Directory and authentication retries
This example subroutine authenticates a user with Active Directory.
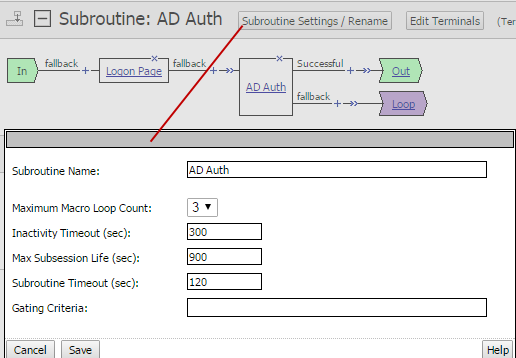
The user gets three authentication retries because the Maximum Macro Loop Count is set to 3. Because the Gating Criteria is blank, the subroutine can create only one distinct subsession. While the subsession exists, if the user makes another request that matches the application area, the user is not challenged again for authentication.
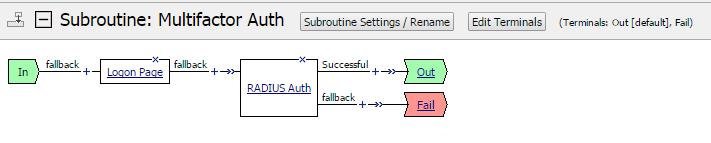
Example: Stepping up with multi-factor authentication
This example subroutine uses RADIUS to authenticate a user. This configuration supports multi-factor authentication when it is implemented using third-party products that integrate through RADIUS.
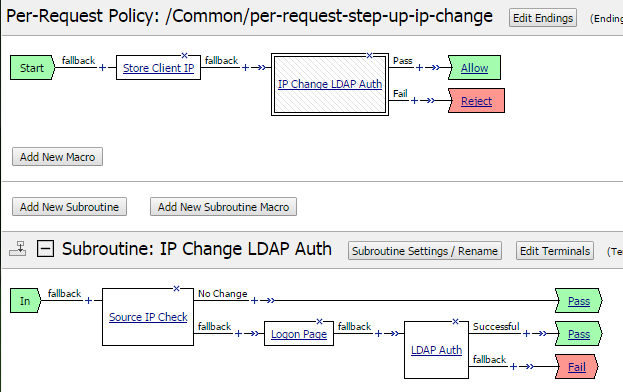
Example: Step-up authentication for an IP address change
Using the Variable Assign agent (renamed as Store Client IP in this example), it's possible to save the client IP address, then compare it to the original client IP address from the start of the session and, if it changes, run LDAP authentication.
Example: Basing step-up authentication on a custom value
In this example, the Variable Assign agent stores a value in a pre-defined custom variable.
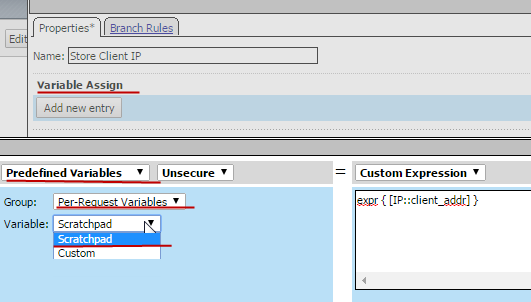
In the illustration, Predefined Variables is selected, Group is set to Per-Request Variables, and Variable is set to Scratchpad. An iRule in the Custom Expression field gets the value, which is the client IP address.
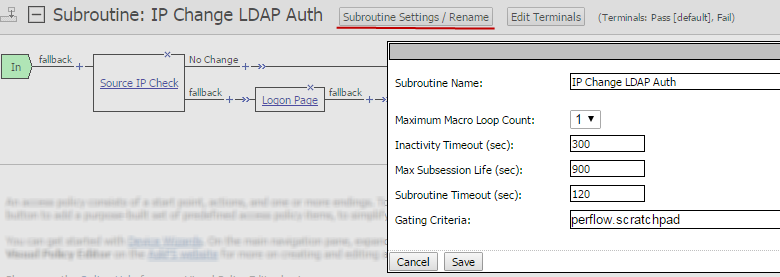
Example: Specifying the Scratchpad variable as the gating criteria
In this example, perflow.scratchpad is specified as the Gating Criteria in the subroutine settings. In another example, you can see the per-request policy store the client IP address in the predefined Scratchpad variable. The Scratchpad variable (available through the Variable Assign agent), equates to the perflow.scratchpad variable that is available in subroutine settings.
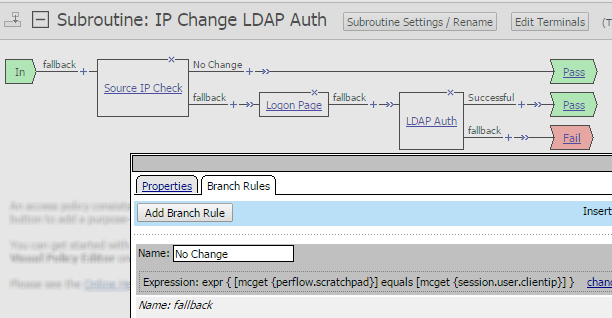
Example: Using additional criteria to determine when to step up
In this example, a change in the client IP address (stored in the gating criteria, perflow.scratchpad) triggers the step-up authentication subroutine to run. However, we want the user to authenticate using LDAP only if the client IP address is not the same one that started the session. An agent in the subroutine, Source IP Check (configured from the Empty agent), makes this comparison.
Step-up authentication configuration basics
These are the configuration objects and settings you need to create when you implement step-up authentication.
- Access profile
- The primary use for step-up authentication is to protect resources in a portal access or web
access management (reverse proxy) configuration. Access Policy Manager®
(APM®) supports it with any of these access profile types:
- LTM+APM
- SSL-VPN
- All
- SWG-Explicit
- SWG-Transparent
- Per-session policy
- A per-session policy, also known as an access policy, can include authentication or not. The policy can be as simple as Start-Allow, or it can be very complex.
- Per-request policy subroutine
- Part of a per-request policy in which you configure a type of authentication to use for step-up authentication.
- Per-request policy subroutine gating criteria setting
- A setting that is blank or contains a perflow variable which specifies a distinct value that represents a reason to run step-up authentication.
- Per-request policy
- A policy that runs for each request throughout a session. It must include a call to the step-up authentication subroutine, and can include logic that determines when to call the step-up authentication subroutine. Unless the gating criteria for the step-up authentication subroutine is set to blank, or to a variable that gets populated automatically, the per-request policy must contain an agent to populate the gating criteria.
Overview: Configuring step-up authentication
These steps guide you through configuring a per-request policy for step-up authentication.
Task summary
Configuring a subroutine for step-up authentication
Specifying how often a user must step up
Setting gating criteria to run step-up authentication more than once per session
Adding a subroutine to a per-request policy
Populating gating criteria for step-up authentication
Using Variable Assign to populate gating criteria
Configuring URL branching for step-up authentication
Session variables for more granular access control in step-up authentication
Session variables might not change throughout a session. However, in conjunction with other data, they can be used to create distinctive subsessions that control which resources a user can reach. A Variable Assign agent or an iRule agent could put a string into the perflow.custom or perflow.scratchpad variable like this example:
Senior_Executive_After_Hours_04_06_2017
An administrator can derive the example string from a session variable and date-time information.
- Senior_Executive - Added to the string based on a group name in the session.ldap.last.attr.memberOf session variable.
- After_Hours - Appended to the string if the current time is after 5 PM today and before 7 AM tomorrow; otherwise, Office_Hours could be appended to the string.
- 04_06_2017 - The most recent 24-hour period that started at 7 AM is appended to the string.
The F5 DevCentral online community is the source for information about iRules®. BIG-IP® Access Policy Manager®: Visual Policy Editor on the AskF5™ web site located at support.f5.com provides information about session variables, perflow variables, and Tcl usage, all of which can be helpful when working with Variable Assign.





