Applies To:
Show Versions
BIG-IP APM
- 11.5.10, 11.5.9, 11.5.8, 11.5.7, 11.5.6, 11.5.5, 11.5.4, 11.5.3, 11.5.2
About RSA SecurID configuration requirements for APM AAA
Before you can use a SecurID AAA server in Access Policy Manager (APM), you need to meet specific requirements for configuration elements and settings on RSA SecurID, as described here.
Authentication agent
To provide RSA SecurID authentication for APM, the RSA Authentication Manager requires an authentication agent for APM in its database.
To create an authentication agent from the RSA Security Console, you need:
- Hostname
- IP addresses for all network interfaces
- Agent Type (set to Standard Agent)
RADIUS client
To provide RSA SecurID authentication for APM, RSA Authentication Manager requires a RADIUS client that corresponds to the authentication agent for APM.
To create a RADIUS client from the RSA Security Console, you need:
- Hostname
- IP addresses for all network interface
- RADIUS secret (this RADIUS secret must match the corresponding RADIUS secret on the APM system).
Character requirements setting in a SecurID token policy
To avoid a problem in the RSA SDK with alphabetic-only PIN policies, do not use them. When you set up a SecurID token policy, set the character requirements to one of these values:
- Require numeric PINs
- Allow alpha-numeric PINs
About RSA SecurID authentication
RSA SecurID is a two-factor authentication mechanism based on a user PIN or password and code that an authenticator generates and provides to the user.
A token is an authentication code generated every 60 seconds by an authenticator (hardware or software) assigned to the user.
 How Access Policy Manager works with RSA SecurID
How Access Policy Manager works with RSA SecurID
- The client submits the user name and PIN code to Access Policy Manager.
- Access Policy Manager sends the user-specified inputs to the RSA authentication server.
- Based on the authentication results, Access Policy Manager grants or denies access to the client.
Task summary for configuring for RSA SecurID authentication
This task list includes all steps required to set up this configuration and provides an example access policy that uses both RSA SecurID and Active Directory authentication. It is only an example. If you are adding RSA SecurID authentication to an existing access policy, you do not need to create another access profile.
Task list
Configuring a SecurID AAA server in APM
Creating an access profile
Configuring RSA SecurID authentication in an access policy
Access policy example for RSA and AD authentication
Typically, when you configure an authentication action, you precede it with a Logon Page action to collect credentials. This example describes how to include more than one authentication item (RSA and AD authentication) in an access policy and present a Logon Page only once.
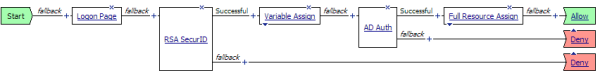
Access policy with RSA SecurID and AD Auth actions
In this example, if the Logon Page action is not customized, the access policy passes the same credentials to both the RSA SecurID and AD Auth authentication agents. But RSA SecurID accepts a user name and a token at logon, while Active Directory accepts a user name and password. To accommodate these differences, customize the Logon Page item.
Logon Page customization: how to collect a token and a password
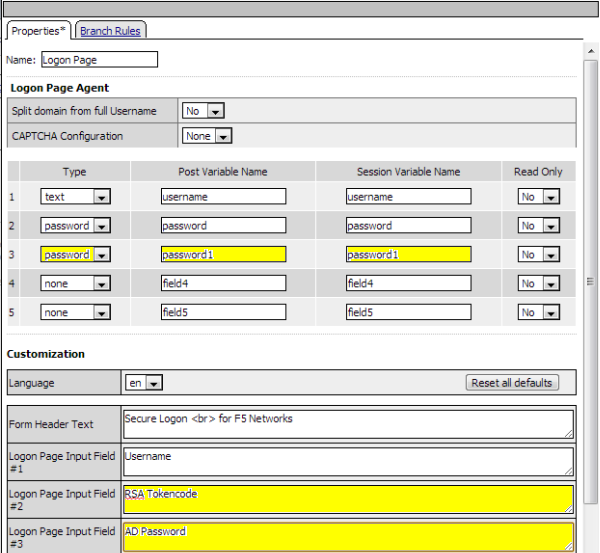
The first highlighted entry defines a second password field. The second password is stored in the session.variable.last.password1 variable.
The highlighted entries in the Customization area change the labels that the Logon Page displays, from Password to RSA Token Code for the first password and to AD Password for the second password.
Variable Assign action: How to pass the AD Password to the AD Auth
Use the Variable Assign action to provide the appropriate password before the AD Auth action occurs.
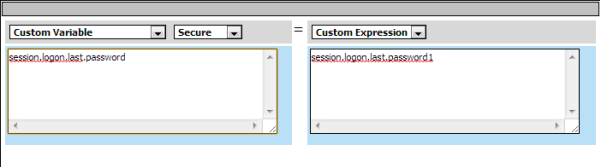
The Variable Assign action moves the AD Auth password, stored in session.variable.last.password1, to the session.variable.last.password variable.
About BIG-IP Edge Client RSA SecurID authentication
RSA SecurID is a two-factor authentication mechanism based on a one-time passcode (OTP) that is generated by using a token code provided by a software or hardware authenticator. Both BIG-IP Edge Client for Windows and OS X systems support the RSA SecurID feature.
A token is a one-time authentication code generated every 60 seconds by an authenticator (hardware or software) assigned to the user.
 How Access Policy Manager works with RSA SecurID
How Access Policy Manager works with RSA SecurID
- Access Policy Manager displays the logon page to the user. The logon page accepts the username and PIN code provided by the user, requests the passcode from RSA Secure-ID Software Token software, and sends the username and passcode to Access Policy Manager.
- Access Policy Manager sends the user-specified inputs to the RSA authentication server.
- Based on the authentication results, Access Policy Manager grants or denies access to the client.
About RSA SecurID (with soft token) automation requirements
For BIG-IP Edge Client for Windows or BIG-IP Edge Client for Mac to support RSA SecurID (with soft token) automation, RSA SecurID must be configured for pin plus tokencode.
Task summary for configuring for RSA SecurID integration with APM
This task list includes all steps required to set up this configuration, and provides an example access policy that uses RSA SecurID authentication for F5 BIG-IP Edge Client. It is only an example. If you are adding RSA SecurID authentication to an existing access policy, you do not need to create another access profile.
Task list
Configuring a SecurID AAA server in APM
Creating an access profile
Configuring RSA SecurID authentication in an access policy
Access policy example for RSA SecurID software token integration
These examples are for RSA SecurID software token integration with BIG-IP Edge Client for Windows and for OS X.
Access policy with RSA SecurID action
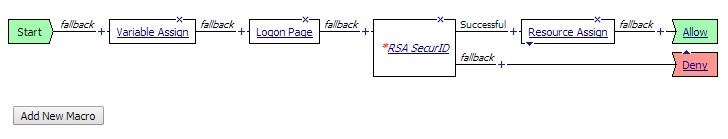
Variable Assign action
Use the Variable Assign action to provide the appropriate password before the Logon Page action occurs.
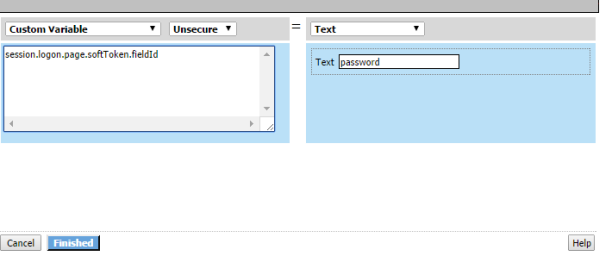
The Variable Assign action stores the text password in the custom variable, session.logon.page.softToken.fieldId; password is the name of the field that is used for RSA token authentication.
RSA SecurID session variables for access policy rules
When the RSA SecurID access policy item runs, it populates session variables which are then available for use in access policy rules. The tables list the session variables for the RSA SecurID access policy item and a logon access policy item.
Session variables for RSA SecurID
| Session Variable | Description |
|---|---|
| session.securid.last.result | Provides the result of the RSA SecurID authentication. The available values are:
|
Common session variables
| Session Variable | Description |
|---|---|
| session.logon.last.username | Provides user credentials. The username string is stored after encrypting, using the system's client key. |
| session.logon.last.password | Provides user credentials. The password string is stored after encrypting, using the system's client key. |
RSA SecurID on Windows using RADIUS configuration troubleshooting tips
You might run into problems with RSA SecurID on Windows using RADIUS configuration. Follow these tips to try to resolve any issues that you encounter.





