Applies To:
Show Versions
BIG-IP LTM
- 12.1.6, 12.1.5, 12.1.4, 12.1.3, 12.1.2, 12.1.1, 12.1.0
BIG-IP DNS
- 12.1.6, 12.1.5, 12.1.3, 12.1.2, 12.1.1, 12.1.0
Overview: DNS response policy zones and the BIG-IP system
The BIG-IP® system can utilize a domain name service (DNS) response policy zone (RPZ) as a firewall mechanism. An RPZ is a zone that contains a list of known malicious Internet domains. The list includes a resource record set (RRset) for each malicious domain. Each RRset includes the names of the malicious domain and any subdomains of the domain.
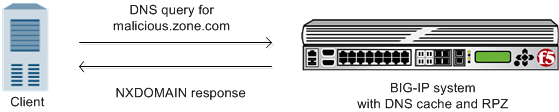
BIG-IP returns NXDOMAIN response to DNS query for malicious domain
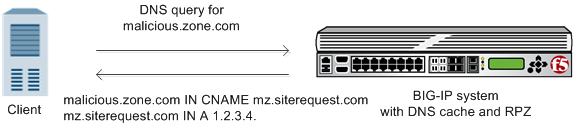
BIG-IP forwards DNS query for malicious domain to walled garden
About creating an RPZ using ZoneRunner
Task summary
Creating a custom RPZ using ZoneRunner
Adding resource records to a custom RPZ
For each malicious domain that you want to add your custom RPZ, create a resource record for the domain. Additionally, you can add a wildcard resource record to represent all subdomains of the malicious domain.
About configuring the BIG-IP system to use an RPZ as a DNS firewall
With an RPZ configuration, the BIG-IP® system filters DNS queries for domains that are known to be malicious and returns custom responses that direct those queries away from the malicious domain.
Task summary
Optional: Adding a TSIG key for the server that hosts the RPZ
Before adding a TSIG key for a DNS server that hosts an RPZ:
- Ensure that the DNS server is configured to allow the BIG-IP® system to perform zone transfers.
- Ensure that the time on the systems that use TSIG keys are synchronized.
- Obtain the TSIG key for each DNS server.
Add a TSIG key to the BIG-IP system configuration, when you want to validate zone transfer communications between DNS Express® and a DNS server hosting an RPZ.
Adding a nameserver object for the server that hosts the RPZ
Creating an RPZ DNS Express zone
- Ensure that the authoritative DNS server that currently hosts the DNS response policy zone (RPZ) is configured to allow zone transfers to the BIG-IP system.
- Ensure a nameserver object that represents that authoritative DNS server exists in the BIG-IP system configuration.
- Determine the name you want to use for the DNS Express zone. The zone name must match the
zone name on the authoritative DNS server exactly. Note: Zone names are case insensitive.
Creating a DNS cache
Adding a local zone to represent a walled garden
Obtain the resource records for the walled garden zone on your network.
Adding an RPZ to a DNS cache
If you want the BIG-IP® system to redirect DNS queries for known malicious domains to a specific location, ensure that you have associated a local zone that represents the RPZ with the DNS cache.
Staging the RPZ on your network
Creating a custom DNS profile for DNS caching
Viewing DNS zone statistics
You can view information about DNS zones.





