Applies To:
Show Versions
BIG-IP AFM
- 14.0.1, 14.0.0
Configuring High-Speed Remote Logging of Protocol Security Events
Overview: Logging remote protocol security events
You can configure the BIG-IP® system to log information about Protocol Security events and send the log messages to remote high-speed log servers.
This illustration shows the association of the configuration objects for remote high-speed logging.
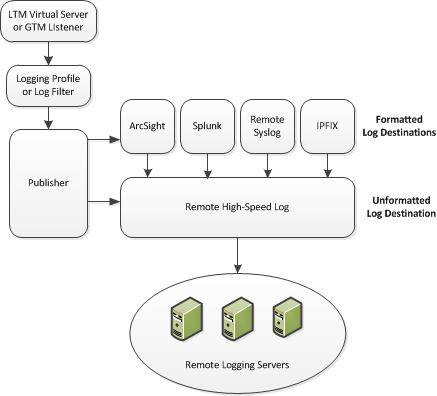
Association of remote high-speed logging configuration objects
Task summary
Perform these tasks to configure Protocol Security event logging on the BIG-IP® system.About the configuration objects of remote protocol security event logging
When configuring remote high-speed logging of Protocol Security events, it is helpful to understand the objects you need to create and why, as described here:
| Object | Reason | Applies to |
|---|---|---|
| Pool of remote log servers | Create a pool of remote log servers to which the BIG-IP system can send log messages. | Creating a pool of remote logging servers. |
| Destination (unformatted) | Create a log destination of Remote High-Speed Log type that specifies a pool of remote log servers. | Creating a remote high-speed log destination. |
| Destination (formatted) | If your remote log servers are the ArcSight, Splunk, IPFIX, or Remote Syslog type, create an additional log destination to format the logs in the required format and forward the logs to a remote high-speed log destination. | Creating a formatted remote high-speed log destination. |
| Publisher | Create a log publisher to send logs to a set of specified log destinations. | Creating a publisher. |
| DNS Logging profile | Create a custom DNS Logging profile to define the data you want the BIG-IP system to include in the DNS logs and associate a log publisher with the profile. | Creating a custom Protocol Security logging profile. |
| Protected object (virtual server) | Associate a custom DNS profile with a protected object to define how the BIG-IP system logs the DNS traffic that the protected object processes. | Configuring a protected object for Protocol Security event logging. |
Creating a pool of remote logging servers
Creating a remote high-speed log destination
Create a log destination of the Remote High-Speed Log type to specify that log messages are sent to a pool of remote log servers.
Creating a formatted remote high-speed log destination
Create a formatted logging destination to specify that log messages are sent to a pool of remote log servers, such as Remote Syslog, Splunk, or IPFIX servers.





