Applies To:
Show Versions
BIG-IP AFM
- 14.1.2, 14.1.0
HTTP Protocol Security
Overview: Securing HTTP traffic
You can secure HTTP traffic by using a default configuration or by customizing the configuration. You can adjust the following security checks in an HTTP security profile:
- HTTP protocol compliance validation
- Evasion technique detection
- Length checking to help avoid buffer overflow attacks
- HTTP method validation
- Inclusion or exclusion of certain files by type
- Mandatory header enforcement
You can also specify how you want the system to respond when it encounters a violation. If the system detects a violation and you enabled the Block flag, instead of forwarding the request, the system can either send a blocking response page or redirect the client to a different location.
Creating an HTTP virtual server to use with HTTP protocol security
Attaching an HTTP protocol security profile to a virtual server
The easiest method for adding HTTP protocol security to your HTTP virtual server is to use the system default profile. You do this by configuring a virtual server with the HTTP profile http, and then associating the default HTTP protocol security profile http_security with the virtual server.
Reviewing violation statistics for security profiles
Overview: Creating a custom HTTP security profile
This implementation describes how to set up the BIG-IP® system to perform security checks on your HTTP virtual server traffic customized to the needs of your environment. Custom configuration of HTTP security and traffic management requires creating an HTTP security profile, and fine tuning this profile so it protects HTTP traffic the way you want. Once you have all HTTP settings specified, you create a virtual server, attach the custom HTTP security profile, and add a default pool to handle the HTTP traffic.
Task summary
Creating a custom HTTP profile
Creating a security profile for HTTP traffic
Configuring an HTTP virtual server with an HTTP security profile
Reviewing violation statistics for security profiles
Overview: Increasing HTTP traffic security
The HTTP security profile consists of many different security checks for the various components of HTTP traffic. This implementation shows you how to fine-tune your HTTP security profile as required by your environment. The custom checks are described under the assumption that you have already created a custom HTTP security profile but have no other prerequisite or special order. You need configure only the custom checks that you are interested in.
You can achieve a greater level of security when you configure the system to perform the following checks:
- HTTP Protocol Checks that are related to RFC compliance and actions to take resulting from a violation
- Request Checks, such as length, allowable HTTP request methods, inclusion or exclusion of file types, and custom headers that must occur in every request
- Blocking Page configuration which describes the page to display in the event of a blocked request when a violation is encountered
About RFC compliance and validation checks
When the BIG-IP® system receives an HTTP request from a client, the first validation check that the system performs is to ensure that it is RFC protocol compliant. If the request passes the compliance checks, the system applies the security profile to the request. So that your system fully validates RFC compliance, keep the following HTTP Protocol Checks enabled (they are enabled by default):
- Several Content-Length headers: This security check fails when the incoming request contains more than one content-length header.
- Null in request: This security check fails when the incoming request contains a null character.
- Unparsable request content: This security check fails when the Advanced Firewall Manager™ is unable to parse the incoming request.
Modifying HTTP protocol compliance checks
About evasion techniques checks
Advanced Firewall Manager can examine HTTP requests for methods of application attack that are designed to avoid detection. When found, these coding methods, called evasion techniques, trigger the Evasion technique detected violation. By creating HTTP security profiles, you can detect evasion techniques, such as:
- Directory traversal, for example, a/b/../c turns into a/c
- Multiple decoding passes
- Multiple backslash characters in a URI, for example, \\servername
- Bare byte decoding (higher than ASCII-127) in a URI
- Apache whitespace characters (0x09, 0x0b, or 0x0c)
- Bad unescape
By default, the system logs requests that contain evasion techniques. You can also block requests that include evasion techniques.
Configuring HTTP protocol evasion techniques blocking policy
About the types of HTTP request checks
By creating HTTP security profiles, you can perform several types of checks on HTTP requests to ensure that the requests are well-formed and protocol-compliant.
- Length checks
- Specify valid maximum lengths for request components to help prevent buffer overflow attacks.
- Method checks
- Specify which HTTP methods the system allows in requests.
- File type checks
- Specify which file types users can or cannot access.
- Mandatory headers
- Specify custom headers that must occur in every request.
- Null in request
- This security check fails when the incoming request contains a null character.
- Unparsable request content
- This security check fails when the system is unable to parse the incoming request.
Configuring length checks for HTTP traffic
Specifying which HTTP methods to allow
Including or excluding files by type in HTTP security profiles
Configuring a mandatory header for an HTTP security profile
Configuring the blocking response page for HTTP security profiles
Overview: Configuring Local Protocol Security Event Logging
You can configure the BIG-IP® system to log detailed information about protocol security events and store those logs locally.
Creating a local Protocol Security Logging profile
Configuring a virtual server for Protocol Security event logging
Viewing Protocol Security event logs locally on the BIG-IP system
Disabling logging
Implementation result
You now have an implementation in which the BIG-IP® system logs specific Protocol Security events locally.
Overview: Logging remote protocol security events
You can configure the BIG-IP® system to log information about Protocol Security events and send the log messages to remote high-speed log servers.
This illustration shows the association of the configuration objects for remote high-speed logging.
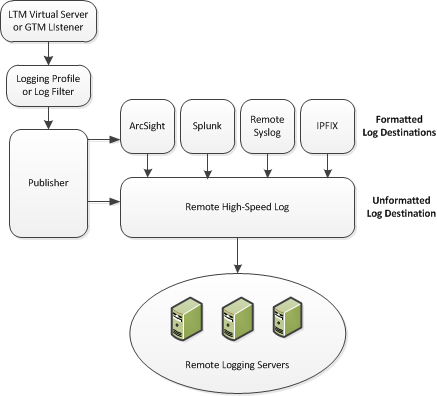
Association of remote high-speed logging configuration objects
Task summary
Perform these tasks to configure Protocol Security event logging on the BIG-IP® system.About the configuration objects of remote protocol security event logging
When configuring remote high-speed logging of Protocol Security events, it is helpful to understand the objects you need to create and why, as described here:
| Object | Reason | Applies to |
|---|---|---|
| Pool of remote log servers | Create a pool of remote log servers to which the BIG-IP system can send log messages. | Creating a pool of remote logging servers. |
| Destination (unformatted) | Create a log destination of Remote High-Speed Log type that specifies a pool of remote log servers. | Creating a remote high-speed log destination. |
| Destination (formatted) | If your remote log servers are the ArcSight, Splunk, IPFIX, or Remote Syslog type, create an additional log destination to format the logs in the required format and forward the logs to a remote high-speed log destination. | Creating a formatted remote high-speed log destination. |
| Publisher | Create a log publisher to send logs to a set of specified log destinations. | Creating a publisher. |
| DNS Logging profile | Create a custom DNS Logging profile to define the data you want the BIG-IP system to include in the DNS logs and associate a log publisher with the profile. | Creating a custom Protocol Security logging profile. |
| Protected object (virtual server) | Associate a custom DNS profile with a protected object to define how the BIG-IP system logs the DNS traffic that the protected object processes. | Configuring a protected object for Protocol Security event logging. |
Creating a pool of remote logging servers
Creating a remote high-speed log destination
Create a log destination of the Remote High-Speed Log type to specify that log messages are sent to a pool of remote log servers.
Creating a formatted remote high-speed log destination
Create a formatted logging destination to specify that log messages are sent to a pool of remote log servers, such as Remote Syslog, Splunk, or IPFIX servers.





