Applies To:
Show Versions
BIG-IP AFM
- 14.1.2, 14.1.0
Deploying AFM in ADC Mode
Deploying AFM in ADC mode
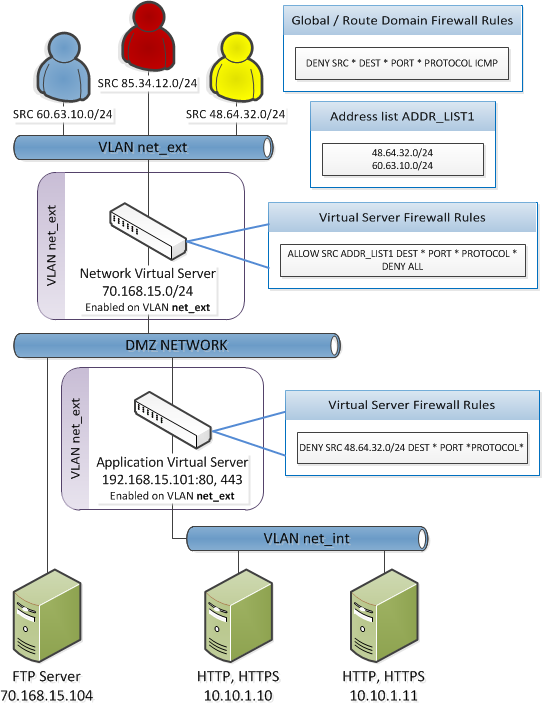
By default, AFM firewall is configured in ADC mode, which is a default allow configuration. In ADC mode, all traffic is allowed through the firewall, and any traffic you want to block must be explicitly specified.
To understand this firewall scenario, imagine that your prerequisite system load-balances all traffic from the Internet to several internal servers. The internal servers are:
| Virtual servers | IP address |
|---|---|
| Network virtual server | 70.168.15.0/24 |
| Application virtual server | 192.168.15.101 |
In order for traffic from the internal application virtual server to reach the external network virtual server, you must create a VLAN and enable both internal and external virtual servers on it. In this scenario, these VLANs are specified:
| VLAN | Configuration |
|---|---|
| net_ext | Enabled on 70.168.15.0/24, 192.168.15.101 |
| net_int | Includes pool members 10.10.1.10, 10.10.1.11 |
In this firewall configuration, there are three external networks that require firewall policies:
| Network | Policy |
|---|---|
| 60.63.10.0/24 | Allow all access |
| 48.64.32.0/24 | Allow all access |
| 85.34.12.0/24 | Deny all access |
ADC mode configuration scenario
Configuration settings for IPv6 pools and ADC mode
- State: Enabled
- Protocol: ICMPv6 (58)
- Type: Neighbor Advertisement (136)
- Source Address: any affected pool members
- Destination Address: the BIG-IP address, or Any
- Action: Accept
- All other values can be left at their defaults, except the rule name.
Such a rule allows ICMPv6 pools to function, when a rule that denies all traffic is added at the end of the rule list in an ADC mode configuration.
Configure AFM to use ADC mode
- On the Main tab, click .
- From the Virtual Server & Self IP Contexts list, select the default action Accept for the self IP and virtual server contexts.
-
From the Global Context list, select the default action for the global rule context.
- Select Drop to silently drop all traffic. Dropping causes the connection to be retried until the retry threshold is reached.
- Select Reject to reject all traffic. Rejecting sends a destination unreachable message to the sender.
- Click Update.
Creating a VLAN for the network firewall
Configuring an LTM virtual server with a VLAN for Network Firewall
Adding a firewall rule to deny ICMP
Creating address lists
- On the Main tab, click .
- Click Create.
- In the name field, type addr_list1.
- In the Addresses area, add the following addresses: 48.63.32.0/24 and 60.63.10.0/24. Click Add after you type each address.
- Click Repeat.
- In the name field, type addr_list2.
- In the Addresses area, add the following address: 85.34.12.0/24.
- Click Add.
- Click Finished.
Creating firewall rule lists
Adding the firewall rules to the rule list
Creating firewall policies
Activating the rule list in the policy
Associating the firewall policies with the virtual servers
- On the Main tab, click .
- Click the name of the virtual server with Destination IP address 70.186.15.0/24.
- Click at the top of the page.
- Change Network Firewall Enforcement to Enabled.
- From the Policy list, select network_virtual_policy.
- Click Update.
- Click Virtual Servers : Virtual Server List at the top of the page.
- Click the name of the virtual server with Destination IP address 192.168.15.101.
- Click at the top of the page.
- Change Network Firewall Enforcement to Enabled.
- From the Policy list, select app_virtual_policy.
- Click Update.





