Applies To:
Show Versions
BIG-IQ Centralized Management
- 5.0.0
How do I evaluate changes made to managed objects?
To change the object settings on a managed device, there are four tasks to perform.
This figure illustrates the workflow you perform to manage the objects on BIG-IP® devices. Evaluating the changes you have made is the third step in this process.

Overview of evaluating changes made to managed objects
Evaluating configuration changes
To apply the object changes to the managed device, you must deploy them.
How do I deploy changes made to managed objects?
Deploying changes applies the revisions that you have made on the BIG-IQ® to the managed BIG-IP® devices.
- To accept the default, proceed with the deployment. The settings from the managing BIG-IQ overwrite the settings on the managed BIG-IP device.
- To override the default, rediscover the device and reimport the service. Any changes that have been made using the BIG-IQ are overwritten with the settings from the managed BIG-IP device.
This figure illustrates the workflow you perform to manage the objects on BIG-IP devices. Deploying the settings is the last step in this process.
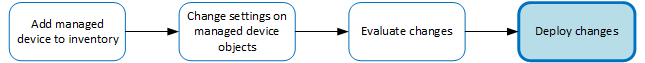
Change managed object workflow
Deploying configuration changes
To apply the changes you made on the BIG-IQ to your managed device, you must deploy those changes to the managed device.
- If you chose to deploy immediately, the changes begin to deploy and the Status column updates as it proceeds.
- If you choose to delay deployment, the Status column displays the scheduled date and time.
Making an urgent deployment
You can skip the evaluation task and deploy changes right now if you need to make urgent changes.
Verifying firewall rules have compiled on all BIG-IP devices
Reviewing deployment process states to diagnose problems
When a firewall security policy or a web application security policy is deployed, that policy goes through several deployment states. Reviewing these states may be useful in understanding what occurred during deployment in order to diagnose a problem. Note that not all states may appear in the log, since what states are displayed depends on how the deployment was processed.
Review the restjavad.n.log file to view deployment states for either a firewall security policy or a web application security policy.
Device deployment states
This table displays states that can occur during the deployment process, and a brief description of each state.
| State | Description |
|---|---|
| CHECK_LICENSE | Licenses for BIG-IQ systems are checked to be valid. |
| CHECK_OTHER_RUNNING_TASKS | Verifies that no tasks are running that could cause errors during deployment. Tasks
that could cause errors include:
|
| GET_DEVICES | Finds all devices managed by the BIG-IQ Security system. |
| CHECK_DEVICE_AVAILABILITY | Determines whether the devices to be deployed are available. |
| LOOKUP_CLUSTERS | Determines if any devices included in the deployment are part of a cluster, and if so, verifies that both devices in the cluster are configured with the same sync mode and sync failover group on the BIG-IP device. |
| REFRESH_CURRENT_CONFIG_SOAP | Using the SOAP API, refreshes the current configuration for all devices included in the deployment. This process adds any new configuration items from the BIG-IP device to the current configuration. |
| REFRESH_CURRENT_CONFIG_REST | Using the REST API, refreshes the current configuration for all devices included in deployment. This process adds any new configuration items from the BIG-IP device to the current configuration. |
| CREATE_SNAPSHOT | Creates a snapshot of the working configuration. |
| CREATE_DIFFERENCE | Generates the differences between the snapshot taken and the current configuration. |
| VERIFY_CONFIG | Verifies that devices to be deployed do not have configuration problems that could lead to deployment errors. |
| GET_CHILD_DEPLOY_DEVICES | Finds all devices managed by Shared Security objects. These devices are considered to be child deployments of a parent firewall security or web application security deployment. |
| START_CHILD_DEPLOY | Starts the deployment of devices managed by Shared Security objects. |
| WAIT_FOR_CHILD_DEPLOY | Waits for deployment of devices managed by Shared Security objects to complete. |
| CLEANUP_PREVIOUS_EVALUATE | Cleans up processing artifacts from the previous evaluation. |
| DISTRIBUTE_DSC_CLUSTERS | Distributes changes to devices identified as being in a cluster by the LOOKUP_CLUSTERS process and that are configured to use the BIG-IP Device Service Clustering (DSC) to keep the BIG-IP devices synchronized. |
| DISTRIBUTE_CONFIG | Distributes configuration changes to the specified devices. |
| DISTRIBUTE_CONFIG_SOAP | Using the SOAP API, distributes configuration changes to the specified devices. |
| DISTRIBUTE_CONFIG_REST | Using the REST API, distributes configuration changes to the specified devices. |
| FOLDBACK_DEPLOYED_ADDITIONS | Inserts any newly-added objects directly into the current configuration to that the BIG-IQ system will already know about those objects on the next refresh of the current configuration. |
| DONE | Indicates the deployment process has completed. |





