Applies To:
Show Versions
BIG-IP AAM
- 11.5.10, 11.5.9, 11.5.8, 11.5.7, 11.5.6, 11.5.5, 11.5.4, 11.5.3, 11.5.2, 11.5.1
BIG-IP APM
- 11.5.10, 11.5.9, 11.5.8, 11.5.7, 11.5.6, 11.5.5, 11.5.4, 11.5.3, 11.5.2, 11.5.1
BIG-IP GTM
- 11.5.10, 11.5.9, 11.5.8, 11.5.7, 11.5.6, 11.5.5, 11.5.4, 11.5.3, 11.5.2, 11.5.1
BIG-IP Link Controller
- 11.5.10, 11.5.9, 11.5.8, 11.5.7, 11.5.6, 11.5.5, 11.5.4, 11.5.3, 11.5.2, 11.5.1
BIG-IP Analytics
- 11.5.10, 11.5.9, 11.5.8, 11.5.7, 11.5.6, 11.5.5, 11.5.4, 11.5.3, 11.5.2, 11.5.1
BIG-IP LTM
- 11.5.10, 11.5.9, 11.5.8, 11.5.7, 11.5.6, 11.5.5, 11.5.4, 11.5.3, 11.5.2, 11.5.1
BIG-IP AFM
- 11.5.10, 11.5.9, 11.5.8, 11.5.7, 11.5.6, 11.5.5, 11.5.4, 11.5.3, 11.5.2, 11.5.1
BIG-IP PEM
- 11.5.10, 11.5.9, 11.5.8, 11.5.7, 11.5.6, 11.5.5, 11.5.4, 11.5.3, 11.5.2, 11.5.1
BIG-IP ASM
- 11.5.10, 11.5.9, 11.5.8, 11.5.7, 11.5.6, 11.5.5, 11.5.4, 11.5.3, 11.5.2, 11.5.1
Configuring IPsec in Interface Mode between Two BIG-IP Systems
Overview: Configuring IPsec in Interface mode between two BIG-IP systems
You can configure an IPsec tunnel when you want to secure traffic that traverses a wide area network (WAN), from one BIG-IP ®system to another. By following this procedure, you can create an IPsec tunnel interface that can be used as any other BIG-IP VLAN. When you configure an IPsec tunnel interface, the IKE tunnel mode security associations occur automatically as part of the tunnel negotiation. For the IPsec tunnel interface, only the IPsec Encapsulating Security Protocol (ESP) is supported for the tunnel interface, and IPComp is not available.
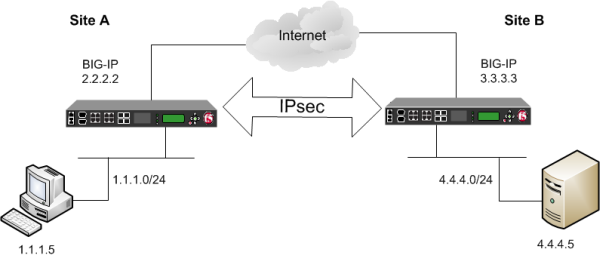
Example of an IPsec deployment
Task summary
Before you begin configuring IPsec, verify that these modules, system objects, and connectivity exist on the BIG-IP® systems in both the local and remote locations:
- BIG-IP Local Traffic Manager™
- This module directs traffic securely and efficiently to the appropriate destination on a network.
- Self IP address
- Each BIG-IP system must have at least one self IP address, to be used in specifying the ends of the IPsec tunnel.
- The default VLANs
- These VLANs are named external and internal.
- BIG-IP connectivity
- Verify the connectivity between the client or server and its BIG-IP device, and between each BIG-IP device and its gateway. For example, you can use ping to test this connectivity.
Task list
Creating a forwarding virtual server for IPsec
Creating a custom IPsec policy for Interface mode
You can create a custom IPsec policy to specify the Interface mode, which allows you to use the IPsec tunnel as a network interface object.





