Applies To:
Show Versions
BIG-IP LTM
- 13.0.1, 13.0.0
Overview: Creating an MQTT configuration
You can use a Message Queuing Telemetry Transport (MQTT) configuration to optimize the performance and bandwidth of mobile environments. Because the MQTT protocol is designed for lightweight publish-and-subscribe messaging, it reduces or eliminates the disadvantages of the commonly used HTTP request-response protocol, especially in mobile environments. For example, you will want to use an MQTT configuration when devices use intermittent connectivity, when bandwidth is at a premium, when an enterprise application interacts with multiple mobile device applications, or when mobile device applications send data reliably without requiring retries.
In an MQTT configuration, clients publish messages, and the BIG-IP® system validates and manages those messages through a pool of message brokers, which then transport and route the messages to subscribing servers. You can examine statistics specific to MQTT parameters through the Profiles Summary.
A typical BIG-IP MQTT configuration includes:
- MQTT pool of message brokers
- iRules for MQTT
- Client SSL profile
- MQTT profile (configured in TMSH)
- Virtual server configured to use MQTT functionality
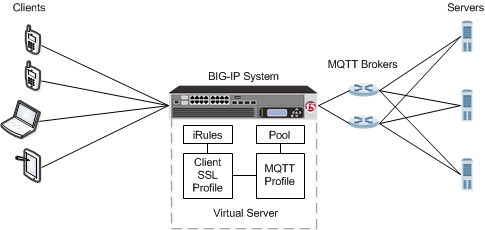
An MQTT configuration
About the MQTT profile
The Message Queuing Telemetry Transport (MQTT) profile supports MQTT protocol functionality, enabling you to configure a publish-and-subscribe environment to manage devices in an Internet of Things (IoT) context. The BIG-IP® system includes a default MQTT profile, configured in TMSH, that you assign to a virtual server.
Example iRule to log MQTT messages
This example iRule shows how to log MQTT messages.
ltm rule mqtt_rule {
when MQTT_CLIENT_INGRESS {
log local0. "Client message type [MQTT::type]"
switch [MQTT::type] {
CONNECT {
log local0. " protocol-name [MQTT::protocol_name]"
log local0. " protocol-version [MQTT::protocol_version]"
log local0. " client-id [MQTT::client_id]"
log local0. " keep-alive [MQTT::keep_alive]"
log local0. " username [MQTT::username]"
log local0. " password [MQTT::password]"
}
PUBLISH {
log local0. " qos [MQTT::qos]"
log local0. " message-id [MQTT::message_id]"
log local0. " topic [MQTT::topic]"
}
PUBREL {
log local0. " message-id [MQTT::message_id]"
}
SUBSCRIBE {
log local0. " message-id [MQTT::message_id]"
set count [MQTT::topic count]
for {set i 0} {$i < $count} {incr i} {
set topic [MQTT::topic index $i]
log local0. " topics index $i $topic"
log local0. " topics index $i qos [MQTT::message topics qos $topic]"
}
}
UNSUBSCRIBE {
log local0. " message-id [MQTT::message_id]"
set count [MQTT::topic count]
for {set i 0} {$i < $count} {incr i} {
log local0. " topics index $i [MQTT::topic index $i]"
}
}
}
}
when MQTT_SERVER_INGRESS {
log local0. "Server message type [MQTT::type]"
switch [MQTT::type] {
CONNACK {
log local0. " return-code [MQTT::return_code]"
}
PUBLISH {
log local0. " message-id [MQTT::message_id]"
log local0. " topic [MQTT::topic]"
}
PUBACK {
log local0. " message-id [MQTT::message_id]"
}
PUBREC {
log local0. " message-id [MQTT::message_id]"
}
PUBCOMP {
log local0. " message-id [MQTT::message_id]"
}
SUBACK {
log local0. " message-id [MQTT::message_id]"
}
UNSUBACK {
log local0. " message-id [MQTT::message_id]"
}
}
}
}
Example iRule to pass client certificate common name
This example iRule shows how to pass the common name for a client certificate to an MQTT server through the username field in the CONNECT message.
when CLIENT_ACCEPTED {
set cn ""
}
when CLIENTSSL_CLIENTCERT {
set cn [ lindex [ split [lindex [ split [X509::subject [SSL::cert 0]] "," ] 0 ] "=" ] 1 ]
log local0. "Client Cert Common Name : $cn"
}
when MQTT_CLIENT_INGRESS {
if {[MQTT::type] == "CONNECT"} {
if {$cn == ""} {
# if we didn't see a client cert, return an authentication error
MQTT::drop # drop current message
MQTT::respond type CONNACK return-code 5 # send a CONNACK
MQTT::disconnect # and disconnect
} else {
MQTT::username $cn # fill-in username field
}
}
}
Task Summary
Task list
Creating a pool
You can create a pool of servers that you can group together to receive and process traffic. After the pool is created, you can associate the pool with a virtual server.
Creating an iRule for MQTT publishing
Creating a Client SSL profile
You create a Client SSL profile when you want the BIG-IP® system to authenticate and decrypt/encrypt client-side application traffic.





