Applies To:
Show Versions
BIG-IP AAM
- 12.1.4, 12.1.3, 12.1.2, 12.1.1, 12.1.0
BIG-IP APM
- 12.1.6, 12.1.5, 12.1.4, 12.1.3, 12.1.2, 12.1.1, 12.1.0
BIG-IP Analytics
- 12.1.6, 12.1.5, 12.1.4, 12.1.3, 12.1.2, 12.1.1, 12.1.0
BIG-IP Link Controller
- 12.1.6, 12.1.5, 12.1.4, 12.1.3, 12.1.2, 12.1.1, 12.1.0
BIG-IP LTM
- 12.1.6, 12.1.5, 12.1.4, 12.1.3, 12.1.2, 12.1.1, 12.1.0
BIG-IP AFM
- 12.1.6, 12.1.5, 12.1.4, 12.1.3, 12.1.2, 12.1.1, 12.1.0
BIG-IP PEM
- 12.1.6, 12.1.5, 12.1.4, 12.1.3, 12.1.2, 12.1.1, 12.1.0
BIG-IP DNS
- 12.1.6, 12.1.5, 12.1.4, 12.1.3, 12.1.2, 12.1.1, 12.1.0
BIG-IP ASM
- 12.1.6, 12.1.5, 12.1.4, 12.1.3, 12.1.2, 12.1.1, 12.1.0
User Roles
What is a user role?
A User role is a property of a BIG-IP® administrative user account. For each BIG-IP user account, you can assign a different user role to each administrative partition to which you the user has access. This allows you to assign multiple user roles to each user account on the system.
A user role controls the following:
- The types of resources that the user can manage
- User roles define the types of resources, or objects, that a user can manage. For example, a user with the role of Operator can enable or disable nodes and pool members only. By contrast, a user with the Guest role cannot manage any BIG-IP system resources.
- The tasks that a user can perform
- For example, a user with the role of Operator can enable or disable nodes and pool members, but cannot create, modify, or delete them. Conversely, a user with the Manager role can perform all tasks related to objects within a partition, except for tasks related to user accounts.
The BIG-IP system offers several different user roles that you can choose from when assigning roles to a user account. Each user role grants a different level and type of permissions to the user.
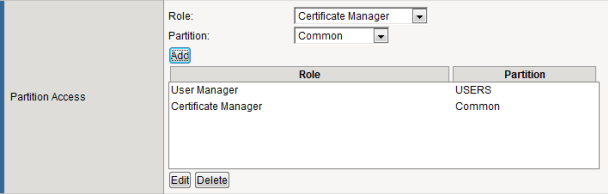
Assigning roles to a user account
You perform this task to change the user roles that are assigned to a user account. You can assign a different role for each partition to which the user has access. By default, the user role that the BIG-IP® system assigns to a user account on each partition is No Access.
User roles and administrative partitions
As a BIG-IP® user with an Administrator or User Manager user role, you can assign user roles to other BIG-IP user accounts. Specifically, for each BIG-IP user account, you can assign a specific user role to each administrative partition to which you grant the user access. In this way, you can control the BIG-IP configuration objects that the user can manage, as well as the types of actions the user can perform on those objects.
About universal access
When you create a BIG-IP administrative user account, you can grant the user access to all administrative partitions on the system, instead of to specific partitions only. This type of access is known as universal access. When you grant universal access to a user, you can assign only one user role, which applies to all partitions on the system for that user.
For example, if you create a user account and assign the role of Operator with the partition access set to All, the user has Operator permissions within all partitions on the system. You cannot assign any other user roles to that user account.
You can assign universal access to any user role except No Access. Moreover, certain user roles on the system automatically provide a user with universal access, and you cannot change this. The user roles that automatically and permanently provide universal access are:
- Administrator
- Resource Administrator
- Application Security Administrator
- Auditor
User roles on the BIG-IP system
This table lists and describes the various user roles that you can assign to a BIG-IP® user account.
| User role | Description | Partition scope |
|---|---|---|
| Administrator | This is the most powerful user role on the system and grants users complete access to all objects on the system. Users with this role cannot have other user roles on the system. | All partitions (mandatory) |
| Resource Administrator | This role grants a user access to all objects on the system except BIG-IP user accounts. With respect to user accounts, a user with this role can view a list of all user accounts on the system but cannot view or change user account properties except for their own user account. Users with this role cannot have other user roles on the system. | All partitions (mandatory) |
| User Manager | This role grants a user permission to manage BIG-IP user accounts. When granted terminal access, a user with this role has access to TMSH only. | Specific partitions or all partitions (optional) |
| Manager | This role grants a user permission to manage a subset of local traffic objects. When granted terminal access, a user with this role has access to TMSH only. | Specific partitions or all partitions (optional) |
| Certificate Manager | This role grants a user permission to manage digital certificates and keys, as well as perform Federal Information Processing Standard (FIPS) operations. When granted terminal access, a user with this role has access to TMSH only. | Specific partitions or all partitions (optional) |
| iRule Manager | This role grants a user permission to create, modify, view, and delete iRules. Users with this role cannot affect the way that an iRule is deployed. For example, a user with this role can create an iRule but cannot assign the iRule to a virtual server or move the iRule from one virtual server to another. When granted terminal access, a user with this role has access to TMSH only. | Specific partitions or all partitions (optional) |
| Application Editor | This role grants a user permission to modify a subset of local traffic objects. When granted terminal access, a user with this role has access to TMSH only. | Specific partitions or all partitions (optional) |
| Acceleration Policy Editor | This role grants a user permission to manage BIG-IP Application Acceleration Manager™ policies. Users with this role cannot have other user roles on the system. | All partitions (mandatory) |
| Firewall Manager | This role grants a user permission to manage all firewall rules and supporting objects. Notably, the Firewall Manager role has no permission to create, update, or delete non-network firewall configurations, including Application Security or Protocol Security policies. | All partitions or a single partition |
| Application Security Administrator | This role grants a user permission to manage BIG-IP Application Security Manager™ (ASM®) configuration objects. This role is similar to the Administrator role but for ASM only. You can assign this role only when the BIG-IP system includes the ASM module. Users with this role cannot have other user roles on the system. When granted terminal access, a user with this role has access to TMSH only. | All partitions (mandatory) |
| Application Security Editor | This role grants a user permission to manage most parts of ASM. You can assign this role only when the BIG-IP system includes the ASM module. When granted terminal access, a user with this role has access to TMSH only. | Specific partitions or all partitions (optional) |
| Fraud Protection Manager | This role grants a user permission to configure the BIG-IP Fraud Protection Service (FPS) module. When granted terminal access, a user with this role has access to TMSH only. | Specific partitions or all partitions (optional) |
| Operator | This role grants a user permission to enable or disable nodes and pool members. When granted terminal access, a user with this role has access to TMSH only. | Specific partitions or all partitions (optional) |
| Auditor | This is a powerful role that grants read-only access to all configuration data on the system, except for ARP data, archives, and support tools. Users with this role cannot have other user roles on the system but can change their own user account password. When granted terminal access, a user with this role has access to TMSH only. | All partitions (mandatory) |
| Guest | This is the least powerful role on the system other than No Access. This role grants read-only access to all objects in the user's assigned partitions plus Common, except for: ARP data, archives, logs, support tools, SNMP configurations displayed in the BIG-IP Configuration utility, and other users' user accounts. A user with this role has write access to their own user account password. When granted terminal access, a user with this role has access to TMSH only. | Specific partitions or all partitions (optional) |
| No Access | This role blocks read and write access to any configuration objects and data on the BIG-IP system. | None |
User role permissions
This table describes the permissions associated with each BIG-IP user role.
| User role | Write access | Read-only access | No access |
|---|---|---|---|
| Administrator | All objects on the system | All objects on the system | Not applicable |
| Resource Administrator | All objects on the system except user accounts | All objects on the system | Not applicable |
| User Manager | User accounts in assigned partitions | Objects in assigned partitions plus Common | ARP entries, archives, SNMP configurations, logs, and support tools |
| Manager | Virtual servers, pool members, nodes, profiles, monitors, and iRules® in assigned partitions. | Objects in assigned partitions plus Common | ARP entries, archives, SNMP configurations, logs, and support tools |
| Certificate Manager | All digital certificates and FIPS operations in assigned partitions | Objects in assigned partitions plus Common | ARP entries, archives, SNMP configurations, logs, and support tools |
| iRule Manager | iRules in assigned partitions | Objects in assigned partitions plus Common | ARP entries, archives, SNMP configurations, logs, and support tools |
| Application Editor | Nodes, pools, pool members, and monitors in assigned partitions | Objects in assigned partitions plus Common | ARP entries, archives, SNMP configurations, logs, and support tools |
| Acceleration Policy Editor | All Application Acceleration Manager™ policy objects and profiles on the system | Most objects on the system | ARP entries, archives, SNMP configurations, logs, and support tools |
| Firewall Manager | All firewall rules and supporting objects in assigned partitions. To modify global and management port rules, Firewall Managers must have partition Common assigned to their accounts. | Objects in assigned partitions plus Common | ARP entries, archives, SNMP configurations, logs, and support tools |
| Application Security Administrator | All Application Security Manager™ security policy objects on the system | Objects in assigned partitions plus Common | ARP entries, archives, SNMP configurations, logs, and support tools |
| Application Security Editor | Application Security Manager™ objects in assigned partitions | Objects in assigned partitions plus Common | ARP entries, archives, SNMP configurations, logs, and support tools |
| Fraud Protection Manager | Fraud Protection Service objects in assigned partitions | Objects in assigned partitions plus Common | ARP entries, archives, SNMP configurations, logs, and support tools |
| Operator | Nodes and pool members in assigned partitions (enable and disable only) | Objects in assigned partitions plus Common | ARP entries, archives, SNMP configurations, logs, and support tools |
| Auditor | None | Most objects on the system | ARP entries, SSL keys, archives, and user passwords |
| Guest | None | Objects in assigned partitions plus Common | ARP entries, archives, SNMP configurations, logs, and support tools |
| No Access | None | None | None |
About the User Manager user role
If a user with this role has permission to manage user accounts in partition A, then this user can view most BIG-IP objects in Common and partition. The objects that the User Manager cannot view are: ARP entries, system archives, SNMP configurations, logs (by default), and support information (through QKView and TCP Dump).
A user with a User Manager role on all partitions (that is, with universal access) can manage user accounts in these ways:
- Create a user account in any partition and assign roles for that user on any partition.
- Modify a user account in any partition and change the existing roles for that user on any partitions.
- View all user accounts.
- Modify the password on any user account.
- Enable or disable terminal access for any user account.
- Change his or her own password.
A user with a User Manager role on a specific partition can manage user accounts in the same way as above except that all actions are restricted to the specific partition to which the user manager has access. Therefore the user manager cannot change any user's role that is associated with another partition. For example, suppose that:
- User mjones has the User Manager role for partition A only.
- User account rsmith resides in Partition A.
- User rsmith has the role of Certificate Manager on Partition A.
- User rsmith has the role of Operator on Partition B.
In this case, user mjones can view, change, or delete rsmith's Certificate Manager role for partition A. User mjones can view rsmith's Operator role for partition B but cannot change or delete that role.
With respect to deleting user accounts in partition A, user mjones cannot delete the rsmith account because user rsmith has access to a partition other than A.
About the Firewall Manager user role
A user with the role of Firewall Manager can manage firewall rules and other supporting objects, including:
- Firewall rules in all contexts
- Address lists
- Port lists
- Schedules
- Security logging profiles and supporting objects, including log publishers and destinations
- IP intelligence and DoS profiles association rights for all of the above security profiles to virtual servers
- DoS Device Configuration (the L2 through L4 DoS protection configuration)
Summary of user role considerations
When managing user roles for BIG-IP® user accounts, it is helpful to understand these system behaviors and restrictions. Some apply to all user accounts, while others apply to remote accounts only.
All user accounts
This section summarizes some high-level concepts about configuring access control for all BIG-IP user accounts, whether stored locally on the BIG-IP system or on a remote authentication server:
- A user account can have only one user role for each administrative partition on the BIG-IP system.
- If a user has multiple roles on the system, the user's most powerful role is applied on first login.
- If you have an Administrator role, you can grant universal access to any user, except those that have a role of No Access.
- A user with the role of Administrator, Resource Administrator, Application Security Administrator, or Auditor always has universal partition access (that is, access to all partitions). For these users, you cannot change this universal access.
- A user with universal access can have only one role on the system, and the role applies to all partitions. On initial login, the user's current partition is set to Common.
- During a user's login session, the role for the current partition is continually displayed in the upper left area of each screen of the BIG-IP Configuration utility.
- If you change a role on a user account while the user is logged into the system through tmsh, the BIG-IP system terminates the user's tmsh session when the user subsequently issues another tmsh command.
Remote user accounts
This section summarizes some high-level concepts about configuring access control for remotely-stored BIG-IP user accounts. Specific BIG-IP system behavior with respect to granting permissions depends on the type of remote authentication server. For more detailed information, see the section titled Remote User Account Management.
- When assigning user role-partition combinations to a single remote user group, you can specify multiple combinations to the group (that is, for the same attribute string). However, for a single user group, you cannot specify multiple roles for the same partition. Within one remote group, the BIG-IP system disallows any attempt to assign multiple roles to the same partition.
- For a user with multi-group membership, if you assign more than one role to the same partition, the BIG-IP system chooses a role and partition for the user at login time, based primarily on the line order that you specified in the remote role configuration on the BIG-IP system.
- If you attempt to assign multiple role-partition combinations to a user, and one of those combinations grants universal access (that is, access to all partitions), then the BIG-IP system will either disallow the universal access assignment (if configuring one user group only), or, depending on configured line order, grant universal access to the user and ignore all other role assignments for individual partitions.
- If you are logged in to the BIG-IP system as a member of the account Other External Users ,and you modify the role of that account to a lesser role, the system modifies the user role of your own account to the lesser role also. The change occurs when you log out and log in again to the BIG-IP system.