Applies To:
Show Versions
BIG-IP APM
- 11.6.5, 11.6.4, 11.6.3, 11.6.2, 11.6.1
BIG-IP LTM
- 11.6.5, 11.6.4, 11.6.3, 11.6.2, 11.6.1
BIG-IP AFM
- 11.6.5, 11.6.4, 11.6.3, 11.6.2, 11.6.1
Overview: Configuring IPsec using manually keyed security associations
You can configure an IPsec tunnel when you want to use a protocol other than SSL to secure traffic that traverses a wide area network (WAN), from one BIG-IP system to another. Typically, you would use the Internet Key Exchange (IKE) protocol to negotiate the secure channel between the two systems. If you choose not to use IKE, you must create manual security associations for IPsec security. A manual security association statically defines the specific attribute values that IPsec should use for the authentication and encryption of data flowing through the tunnel.
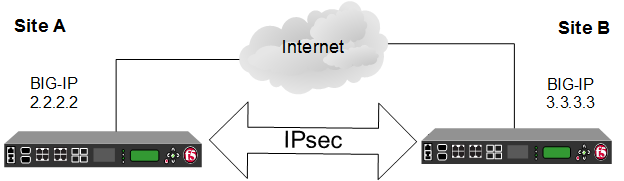 Illustration of an IPsec deployment
Illustration of an IPsec deployment
The implementation of the IPsec protocol suite with a manual security association consists of these components:
- IPsec policy
- An IPsec policy is a set of information that defines the specific IPsec protocol to use (ESP or AH), and the mode (Transport, Tunnel, or iSession). For Tunnel mode, the policy also specifies the endpoints for the tunnel. The way that you configure the IPsec policy determines the way that the BIG-IP system manipulates the IP headers in the packets.
- Manual security association
- A manual security association is set of information that the IPsec protocol
uses to authenticate and encrypt application traffic.Note: When you manually create a security association instead of using IKE, the peer systems do not negotiate these attributes. Peers can communicate only when they share the same configured attributes.
- Traffic selector
- A traffic selector is a packet filter that defines what traffic should be handled by a IPsec policy. You define the traffic by source and destination IP addresses and port numbers.
About IPsec Tunnel mode
Tunnel mode causes the IPsec protocol to encrypt the entire packet (the payload plus the IP header). This encrypted packet is then included as the payload in another outer packet with a new header. Traffic sent in this mode is more secure than traffic sent in Transport mode, because the original IP header is encrypted along with the original payload.
Task summary
You can configure an IPsec tunnel to secure traffic that traverses a wide area network (WAN), such as from one data center to another.
Before you begin configuring IPsec, verify that these modules, system objects, and connectivity exist on the BIG-IP systems in both the local and remote locations:
- BIG-IP Local Traffic Manager
- This module directs traffic securely and efficiently to the appropriate destination on a network.
- Self IP address
- Each BIG-IP system must have at least one self IP address, to be used in specifying the ends of the IPsec tunnel.
- The default VLANs
- These VLANs are named external and internal.
- BIG-IP system connectivity
- Verify the connectivity between the client or server and its BIG-IP device, and between each BIG-IP device and its gateway. For example, you can use ping to test this connectivity.
Task list
Creating a forwarding virtual server for IPsec
Creating custom IPsec policies for manual security associations
Manually creating IPsec security associations for inbound and outbound traffic
Creating IPsec traffic selectors for manually keyed security associations
Verifying IPsec connectivity for Tunnel mode
After you have manually configured security associations for an IPsec tunnel and before you configure additional functionality, you can verify that the tunnel is passing traffic.





