Applies To:
Show Versions
BIG-IP LTM
- 13.1.0, 13.0.1, 13.0.0, 12.1.3, 12.1.2, 12.1.1, 12.1.0
Overview: Using IPsec on the BIG-IP system to establish a secure network
This document guides you through the steps to configure a site-to-site (S2S) VPN tunnel connection from a corporate data center to an Microsoft Azure virtual network (VNet).
Before you can set up a S2S VPN tunnel, you need to create a virtual network, gateway subnet in Azure, and complete other Azure VPN configuration steps. These are all beyond the scope of this document. For details, see Create a VNet with a Site-to-Site connection using PowerShell at https://azure.microsoft.com/en-us/documentation/articles/vpn-gateway-create-site-to-site-rm-powershell/
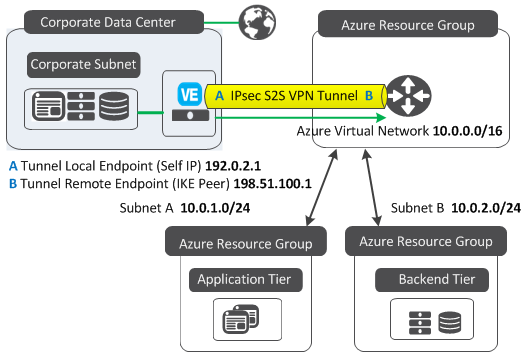
Sample configuration of a corporate data center and Azure resource groups connected by an IPsec site-to-site VPN tunnel
This illustration shows:
- A corporate data center, which includes a BIG-IP® VE and is where databases live.
- An Azure resource group, which contains a VNet. This VNet acts as a central hub for taking care of routing out to additional subnets.
- Additional Azure resource groups, which host applications and appliances.
In order for the databases in the corporate data center to contact the applications in Azure, you need to set up a VPN tunnel between the BIG-IP VE and Azure VNet.
How do I set up a secure tunnel to an Azure virtual network?
You should follow all of the tasks in this document, in the order shown.
Define an IKE Phase 2 security policy
Use these steps to configure the Internet Key Exchange (IKE) Phase 2 settings (authentication & encryption algorithms and perfect forward secrecy) for tunnel traffic.
In case you are not familiar with IKE, IKE Phase 2 is where security associations (a set of policy and key[s] used to protect information) are negotiated on behalf of services such as IPsec, or any other service that needs key material and/or parameter negotiation.
Define eligible web traffic for the secure tunnel
Use these steps to direct web traffic into the secure tunnel.
The traffic selector (a packet filter that defines which traffic should be handled by an IPsec policy) filters traffic based on the IP addresses and port numbers that you specify, as well as the custom IPsec policy you assign.
![]() Watch how to define eligible web traffic for the secure tunnel
Watch how to define eligible web traffic for the secure tunnel
Define IKE Phase 1 tunnel negotiation parameters
Use these steps to configure negotiation to authenticate Internet Key Exchange (IKE) peers and to encrypt IKE communication.
During IKE Phase 1, IKE peers, a configuration object of the IPsec protocol that represents a BIG-IP® system on each side of the IPsec tunnel, allow two systems to authenticate each other.
![]() Watch how to define IKE Phase 1 tunnel negotiation parameters
Watch how to define IKE Phase 1 tunnel negotiation parameters
Create a virtual interface for routing traffic through the tunnel
Use these steps to create an IPsec interface profile to filter traffic through the tunnel according to the traffic selector you specify.
The parent profile specifies the profile from which the newly created profile inherits settings.
![]() Watch how to create a virtual interface for routing traffic through the tunnel
Watch how to create a virtual interface for routing traffic through the tunnel
Create a tunnel by assigning endpoints and direction
Use these steps to create an IPsec tunnel on the BIG-IP® system and specify how the tunnel carries traffic.
When configuring a new tunnel, the default setting for Mode is Bidirectional, but this document only describes how to set up a tunnel for outbound traffic; that is, IPsec tunneling from a corporate data center network to a Microsoft Azure network.
![]() Watch how to create a tunnel by assigning endpoints and direction
Watch how to create a tunnel by assigning endpoints and direction
Create IP addresses for local and remote tunnel endpoints
![]() Watch how to create IP addresses for local and remote tunnel endpoints
Watch how to create IP addresses for local and remote tunnel endpoints
Add a static route for web traffic
Use these steps to route traffic from a BIG-IP system to an Azure virtual network and to specify the virtual interface as the gateway for the route.
A static route with the newly created tunnel allows any traffic hitting the BIG-IP system and destined for the specified subnet to be routed through the tunnel.
Disable load balancing and forward web traffic through the tunnel
Use these steps to create a forwarding virtual server to move traffic to the destination address.
Selecting Forwarding (IP) for Type specifies a virtual server like other virtual servers, except that the virtual server has no pool members to load balance. The virtual server forwards the packet directly to the destination IP address specified in the client request.
Other resources
For information about IKE or related industry-standard technologies, see the relevant IETF RFCs (Request for Comments).
For information about the F5 BIG-IP platform and Microsoft Azure, see The BIG-IP® Platform and Microsoft Azure: Application Services in the Cloud whitepaper at https://f5.com.
For information about the F5 BIG-IP Virtual Edition and Azure, see BIG-IP® Virtual Edition and Microsoft Azure: Setup on the AskF5™ Knowledge Base at http://support.f5.com.
For information about Azure VPN Gateway documentation, see Create a VNet with a Site-to-Site connection using PowerShell at https://azure.microsoft.com/en-us/documentation/articles/vpn-gateway-create-site-to-site-rm-powershell/.
For videos that walk you through common business tasks, see: https://www.youtube.com/playlist?list=PLyqga7AXMtPPi-MPCs8eC2b3EZDNqHuBO
Or, search for F5: Make It Work! on our DevCentral YouTube channel.





