Applies To:
Show Versions
BIG-IP ASM
- 11.5.10, 11.5.9, 11.5.8, 11.5.7, 11.5.6, 11.5.5, 11.5.4, 11.5.3, 11.5.2, 11.5.1
Overview: Integrating ASM and APM with database security products
You can deploy Application Security Manager (ASM) and Access Policy Manager(APM) with database security products, such as IBM InfoSphere Guardium to increase security visibility, receive alerts about suspicious activity, and prevent attacks. When integrated with database security, ASM can provide information about each HTTP request and database query. This allows the database security system to correlate the web transaction with the database query to make a security assessment of the transaction. ASM also provides application level details to improve the database security system's logging and reporting.
For you to integrate ASM with a database security product, the database security server itself must have been configured and accessible on the network. On the BIG-IP system, you specify the host name or IP address of the database security server. Then, you enable database security integration for one or more security policies that are set up to protect web application resources.
When using database security, Application Security Manager monitors web application traffic and sends information about the users, the requests, and reporting events to the database security server. The following figure shows an example of how ASM can integrate with the IBM InfoSphere Guardium Database Activity Monitoring Appliance.
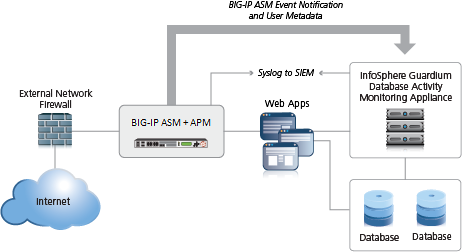 Integrating ASM and APM with external database security example
Integrating ASM and APM with external database security example
The security policy can get user names from requests using login pages configured from within ASM, or the policy can retrieve the user names from Access Policy Manager(APM). This implementation describes how to integrate ASM and APM with an external database security server. APM handles user authentication in this case and provides the information that is sent to the database security server.
Prerequisites for integrating ASM and APM with database security
In order to integrate a database security server from within Application Security Manager (ASM) so that the security policy retrieves the user names from Access Policy Manager (APM), you need to perform basic these system configuration tasks according to the needs of your networking configuration:
- Run the setup utility and create a management IP address.
- License and provision ASM, APM, and Local Traffic Manager (LTM).
- Configure a DNS address ().
- Configure an NTP server ().
- Restart ASM (at the command line, type tmsh restart /sys service asm).
Task Summary
Creating a VLAN
Creating a self IP address for a VLAN
Creating a local traffic pool for application security
Creating a virtual server to manage HTTPS traffic
Creating a security policy automatically
Creating an access profile
Configuring an access policy
Adding the access profile to the virtual server
You associate the access profile with the virtual server created for the web application that Application Security Manager is protecting.
You associate the access profile with the virtual server so that Access Policy Managercan apply the profile to incoming traffic.
Configuring a database security server
Enabling database security integration with ASM and APM
Implementation result
You have set up a BIG-IP system to use Application Security Manager (ASM) to secure application traffic, and Access Policy Manager (APM) to check user credentials.
Client traffic is routed to the virtual server for the web application. At first, traffic is handled by the APM module. APM verifies user credentials and allows those with valid credentials to use web application. APM also sends user names and session IDs of valid users to ASM. After that, ASM checks for security violations and forwards traffic that meets the security policy requirements to the backend server.
The database security server includes the application and user information provided by ASM and APM, so it can be viewed in logs and reports on that system. The database security server can perform a more in depth security assessment of the web request.
If you want to review reports and event logs that associate the user name with the session information on the BIG-IP system, you can set up session tracking (by enabling session awareness). When session awareness is enabled, you can see the user names on the Event Logs: Application: Requests screen in the General Details section of specific requests. IN addition, the Reporting: Application: Charts screen displays the users who sent the illegal requests.





