Applies To:
Show Versions
BIG-IP APM
- 13.0.1, 13.0.0
About logon items
Logon items either display on a logon screen, or specify and present a logon screen to a user.
Logon screens display input fields, and in some cases messages. The items that present a logon screen accept user input and store it in session variables for use in another access policy item; typically, that is an authentication item and it usually follows a logon item in an access policy.
When you work with a logon item, you can usually change some aspect of the logon experience.
- Language on the screen
- Access Policy Manager® (APM®) provides the text displayed on the logon screen translated into a number of languages. (Languages are specified in the access profile.) Selecting a language in a logon item translates the text to that language. Translated text can be used as is or customized further.
- Text on the screen
- APM provides default labels for the user input fields and for any messages that can be displayed on the logon screen. The text can be edited.
- Fields on the screen
- The logon page item provides up to five fields that can be displayed or not. The type for each field is user-selectable: password, text, select (from a list).
Some logon items include authentication-specific settings. These logon items are appropriate in specific cases only:
- HTTP 401 error
- The HTTP 401 Response logon item is appropriate in response to an HTTP 401 error. It can precede HTTP Basic or Kerberos authentication, or both.
- HTTP 407 error
- The HTTP 407 Response logon item is appropriate in response to an HTTP 407 error. It can precede HTTP Basic or Kerberos authentication, or both. It is applicable for use with Secure Web Gateway (SWG) explicit forward proxy only.
- Standalone VMware View client
- The VMware View logon page is for use with a standalone VMware View client. It presents a logon screen that is customized for the selected authentication type (from a set of supported types).
About the External Logon page
An External Logon page action provides a link to a logon page on an external server. An external solution can then provide robust logon credentials to the access policy. A logon action typically precedes the authentication action that checks the credentials provided on the logon page.
When an access policy reaches the External Logon page action:
- Access Policy Manager® sends an HTML page containing JavaScript code that redirects users to the external server.
- The client submits a post_url variable. This post_url
variable is used by the external application to return a value to the access policy. When the
user completes authentication on the external server, the external server posts back to the URL
specified in this variable, to continue the session.
The value of post_URL is in the format: http(or https)://Access_Policy_Manager_URI/my.policy. The Access_Policy_Manager_URI is the URI visible to the user, taken from the HTTP Host header value sent by the browser.
An External Logon Page action provides these configuration elements and options:
- External Logon Server URI
- Specifies the URI of the external logon server.
- Split domain from full username
- Specifies Yes or No.
- Yes - specifies that when a username and domain combination is submitted (for example, marketing\jsmith or jsmith@marketing.example.com), only the username portion (in this example, jsmith) is stored in the session variable session.logon.last.username.
- No - specifies that the entire username string is stored in the session variable.
About HTTP 401 Response
The HTTP 401 Response action sends an HTTP 401 Authorization Required Response page to capture HTTP Basic or Negotiate authentication.
The HTTP 401 Response action provides up to three branches: Basic, Negotiate, and fallback. Typically, a basic type of authentication follows on the Basic branch and a Kerberos Auth action follows on the Negotiate branch.
An HTTP 401 Response action provides these configuration elements and options.
- Basic Auth Realm
- Specifies the authentication realm for use with Basic authentication.
- HTTP Auth Level
- Specifies the authentication required for the policy.
- none - specifies no authentication.
- basic - specifies Basic authentication only.
-
negotiate - specifies Kerberos authentication only.Note: This option is not available for a per-request policy subroutine.
-
basic+negotiate - specifies either Basic or Kerberos
authentication. Note: This option is not available for a per-request policy subroutine.
The action provides customization options that specify the text to display on the screen.
- Language
- Specifies the language to use to customize this HTTP 401 response page. Selecting a language
causes the content in the remaining fields display in the selected language.Note: Languages on the list reflect those that are configured in the access profile.
- Logon Page Input Field #1
- Specifies the text to display on the logon page to prompt for input for the first field. When Language is set to en, this defaults to Username.
- Logon Page Input Field #2
- Specifies the text to display on the logon page to prompt for input for the second field. When Language is set to en, this defaults to Password.
- HTTP response message
- Specifies the text that appears when the user receives the 401 response, requesting authentication.
About HTTP 407 Response
The HTTP 407 response action sends an HTTP 407 Proxy Authentication Required page to capture HTTP Basic or Negotiate authentication. The HTTP 407 Response action provides three branches: Basic, Negotiate, and fallback. Typically, a basic type of authentication follows on the Basic branch and a Kerberos Auth action follows on the Negotiate branch. An HTTP 407 response action provides these configuration elements and options:
The action provides 407 response settings.
- Basic Auth Realm
- Specifies the authentication realm for use with Basic authentication.
- HTTP Auth Level
- Specifies the authentication required for the access policy.
- none - specifies no authentication.
- basic - specifies Basic authentication only.
- negotiate - specifies Kerberos authentication only.
- basic+negotiate - specifies either Basic or Kerberos authentication.
The action provides customization options that specify the text to display on the screen.
- Language
- Specifies the language to use to customize this HTTP 407 response page. Selecting a language
causes the content in the remaining fields display in the selected language.Note: Languages on the list reflect those that are configured in the access profile.
- Logon Page Input Field #1
- Specifies the text to display on the logon page to prompt for input for the first field. When Language is set to en, this defaults to Username.
- Logon Page Input Field #2
- Specifies the text to display on the logon page to prompt for input for the second field. When Language is set to en, this defaults to Password.
- HTTP response message
- Specifies the text that appears when the user receives the 407 response, requesting authentication.
About Logon Page
A logon page action prompts for a user name and password, or other identifying information. The logon page action typically precedes the authentication action that checks the credentials provided on the logon page. The logon page action provides up to five customizable fields and enables localization.
The logon page action provides these configuration options and elements.
- Split domain from full username
- Specifies Yes or No.
- Yes - specifies that when a username and domain combination is submitted (for example, marketing\jsmith or jsmith@marketing.example.com), only the username portion (in this example, jsmith) is stored in the session variable session.logon.last.username.
- No - specifies that the entire username string is stored in the session variable.
- CAPTCHA configuration
- Specifies a CAPTCHA configuration to present for added CAPTCHA security on the logon page.
- Type
- Specifies the type of logon page input field: text,
password, select,
checkbox, or none.
- text Displays a text field, and shows the text that is typed in that field.
- password Displays an input field, but displays the typed text input as asterisks.
- select Displays a list. The list is populated with values that are configured for this field.
- checkbox Displays a check box.
- none Specifies that the field is not displayed on the logon page.
- Post Variable Name
- Specifies the variable name that is prepended to the data typed in the text field. For example, the POST variable username sends the user name input omaas as the POST string username=omaas.
- Session Variable Name (or Subsession Variable Name)
- Specifies the session variable name that the server uses to store the data typed in the
text field. For example, the session variable username stores the
username input omaas as the session variable string
session.logon.last.username=omaas. Note: A per-request policy subroutine uses subsession variables in place of session variables.
- Clean Variable
- Specifies whether to clear any value from the variable before presenting the logon page to the user; to clean the variable, select Yes. Defaults to No.
- Values
- Specifies values for use on the list when the input field type is select.
- Read Only
- Specifies whether the logon page agent is read-only, and always used in the logon process as specified. You can use Read Only to add logon POST variables or session variables that you want to submit from the logon page for every session that uses this access policy, or to populate a field with a value from a session variable. For example, you can use the On-Demand Certificate agent to extract the CN (typically the user name) field from a certificate, then you can assign that variable to session.logon.last.username. In the logon page action, you can specify session.logon.last.username as the session variable for a read only logon page field that you configure. When Access Policy Manager® displays the logon page, this field is populated with the information from the certificate CN field (typically the user name).
Additionally, customization options specify text and an image to display on the screen.
- Language
- Specifies the language to use to customize this logon page. Selecting a language causes
the content in the remaining fields to display in the selected language.Note: Languages on the list reflect those that are configured in the access profile.
- Form Header Text
- Specifies the text that appears at the top of the logon box.
- Logon Page Input Field # number
- Specifies the text to display for each input field (number 1 through 5) that is defined in the Logon Page Agent area with Type set to other than none.
- Logon Button
- Specifies the text that appears on the logon button, which a user clicks to post the defined logon agents.
- Front Image
- Specifies an image file to display on the logon page. The Replace Image link enables customization and the Revert to Default Image discards any customization and use the default logon page image.
- Save Password Check Box
- Specifies the text that appears adjacent to the check box that allows users to save their passwords in the logon form. This field is used only in the secure access client, and not in the web client.
- New Password Prompt
- Specifies the prompt displayed when a new Active Directory password is requested.
- Verify Password Prompt
- Specifies the prompt displayed to confirm the new password when a new Active Directory password is requested.
- Password and Password Verification do not Match
- Specifies the prompt displayed when a new Active Directory password and verification password do not match.
- Don't Change Password
- Specifies the prompt displayed when a user should not change password.
About the virtual keyboard
A virtual keyboard displayed on the logon screen prevents password characters from being typed on the physical keyboard. The virtual keyboard appears on the logon screen when a user clicks in the password field. A user then types the password by clicking the characters on the virtual keyboard, instead of typing them on the physical keyboard.
A virtual keyboard action applies to all logon page actions that follow it in the access policy.
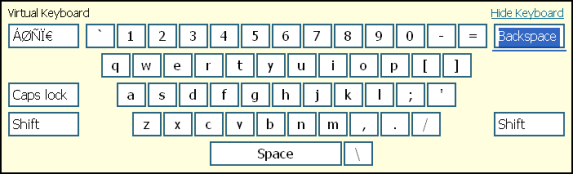
The virtual keyboard action provides these configuration elements and options:
- Virtual Keyboard
- Specifies whether the onscreen virtual keyboard is enabled or disabled.
- Move Keyboard After Every Keystroke
- Specifies whether the onscreen keyboard moves after the user enters a keystroke with a mouse click.
- Allow Manual Input
- Specifies whether a user can type the password with the physical keyboard, in addition to clicking keys on the virtual keyboard.
About the VMware View logon page action
A VMware View logon page action can display a message or can request Windows, RSA SecurID, or RADIUS logon credentials. A logon action typically precedes the authentication action that checks the credentials provided on the logon page.
The VMware View logon page provides these configuration elements and options:
- VMware View logon screen
- Specifies the type of logon screen to display:
- Windows Password - requests Windows logon credentials.
- RSA SecurID - requests RSA SecurID logon credentials.
- RADIUS - requests RADIUS credentials.
- Disclaimer - displays a message dialog box; for example, to display acceptable use terms.
- VMware View Windows Domains
- Specifies domain names separated by commas; for use with the Windows Password screen.
- VMware View RADIUS Auth Label
- Specifies the name of the RADIUS authentication provider to display on the RADIUS logon screen in a message similar to this one: Please provide your Auth Label credentials
The VMware View logon page action also provides customization options to specify the text to display on the screen:
- Language
- Specifies the language to use to customize this logon page. Selecting a language causes the
content in the remaining fields display in the selected language.Note: Languages on the list reflect those that are configured in the access profile.
- Logon Page Input Field #1
- Specifies the text to display on the logon page to prompt for input for the first field. When Language is set to en, this defaults to Username.
- Logon Page Input Field #2
- Specifies the text to display on the logon page to prompt for input for the second field. When Language is set to en, this defaults to Password.
- Disclaimer message
- Specifies a message to display in the disclaimer logon screen.
About assignment items
Most assignment items support assigning resources to a session. In contrast, the Variable Assign item supports assigning values to existing variables, to existing configuration elements, and to variables that you define yourself.
- Resource assignment
- A resource assignment item is usually placed immediately prior to an
Allow ending on a branch in an access policy. At that point, any
branching (based on client type or geolocation, and so on), client software checks, SSL client
certificate checks, and authentication items are complete. Resource assignment supports:
- Selection of the resources that are needed to establish a network access, portal access, or application access session, including a webtop and any ACLs.
- Mapping resources to an Active Directory or LDAP group.
- Overriding the pool assignment made in a virtual server.
- Variable assignment
- A variable assignment item is placed where needed in an access policy. Variable assignment
items can support:
- Replacing the value of one configuration object, such as a subnet, with another configuration object of the same type.
- Replacing the value of a session variable.
- Taking a value from an AAA attribute (which must be already available in the session, retrieved by another item), and assigning the attribute value to a variable.
- Creating a variable for any reason (for example, storing a value for later retrieval or using the value in arithmetic operations).
- Using Tcl expressions to derive values and assign them to variables.
About ACL Assign
An ACL Assign action dynamically assigns static access control lists (ACLs). ACLs then apply only to clients that reach such an assignment action in the access policy. An ACL Assign action provides these configuration elements and options: selection of static ACLs from those configured in Access Policy Manager®.
When no ACLs are assigned in an access policy, the default behavior allows access. When an ACL is assigned in an access policy, it can restrict resources to only those specified in the ACL provided that the last ACE in the list is configured to reject any connection not matched by a previous entry.
About AD Group Resource Assign
The AD Group Resource Assign action enables users to create entries that specify Active Directory groups and assign resources to them.
An AD Group Resource Assign action provides these configuration elements and options:
- Groups
- Specifies the AD groups to which resources are assigned. A list of groups can be imported through the AD AAA server and created manually by typing group names.
- Resources
- Specifies Static ACLS, Network Access resources, App Tunnels, and so on to assign to the selected groups. Any resource on the system can be assigned to a group. The system limits apply; for example, only one webtop should be assigned to a group.
About Advanced Resource Assign
The Advanced Resource Assign action enables assignment of resources.
An Advanced Resource Assign action provides these configuration elements and options:
- Resource type
- Specifies a type of resource (one per tab), and on each tab provides a check list or radio button list of such resources for selection. Resource types include: Network Access, Portal Access, App Tunnels, Remote Desktops, Static ACLs, SAML, Webtops, Webtop Links, Webtop Sections, and Static Pools.
About BWC Policy
The BWC Policy action enables users to assign bandwidth control (BWC) policies to the traffic that passes through the virtual server.
A BWC Policy action provides these configuration elements and options:
- Static BWC policies
- Specifies one or more static BWC policies from those configured on the BIG-IP® system.
- Dynamic BWC Policy
- Specifies the name of one dynamic BWC policy that was configured to shape traffic for Citrix clients that support MultiStream ICA.
- Very High Citrix BWC Category
- Specifies the name of the category in the BWC policy that assigns a percentage of the maximum bandwidth to a very high level of Citrix traffic.
- High Citrix BWC Category
- Specifies the name of the category in the BWC policy that assigns a percentage of the maximum bandwidth to a high level of Citrix traffic.
- Very High Citrix BWC Category
- Specifies the name of the category in the BWC policy that assigns a percentage of the maximum bandwidth to a medium level of Citrix traffic.
- Very High Citrix BWC Category
- Specifies the name of the category in the BWC policy that assigns a percentage of the
maximum bandwidth to a low level of Citrix traffic.Note: For more information, refer to BIG-IP® Access Policy Manager®: Third-Party Integration Implementations on the AskF5™ web site (http://support.f5.com/kb/en-us.html).
About Citrix Smart Access
The Citrix Smart Access action enables users to assign Citrix SmartAccess filters to the session. A filter is a name; it is defined in a Citrix software product.
A Citrix Smart Access action provides these configuration elements and options:
- Assignment
- One or more entries each of which specifies the name of a filter. The name must match the name that is specified in the Citrix software product.
For more information, refer to BIG-IP® Access Policy Manager®: Third-Party Integration Implementations on the AskF5™ web site (http://support.f5.com/kb/en-us.html).
About Dynamic ACL
A dynamic ACL is an ACL that is created on and stored in an LDAP, RADIUS, or Active Directory server. A Dynamic ACL action dynamically creates ACLs based on attributes from the AAA server. Because a dynamic ACL is associated with a user directory, this action can assign ACLs specifically per the user session.
A Dynamic ACL action provides these configuration elements and options:
- Source
- Specifies an option and the attribute from which the Dynamic ACL action extracts ACLs: Custom indicates an F5 ACL from an Active Directory, RADIUS, or LDAP directory; Cisco AV-Pair VSA indicates a Cisco AV-Pair ACL from a RADIUS directory; the field is prepopulated with: session.radius.last.attr.vendor-specific.1.9.1.
- ACL
- Specifies the dynamic ACL container configured on the BIG-IP® system.
- Format
- Specifies the format (F5 or Cisco) in which the ACL is specified.
About LDAP Group Resource Assign
The LDAP Group Resource Assign action enables users to create entries that specify LDAP groups and assign resources to them.
An LDAP Group Resource Assign action provides these configuration elements and options:
- Groups
- Specifies the LDAP groups to which resources are assigned. A list of groups can be imported through the LDAP AAA server and created manually by typing group names.
- Resources
- Specifies Static ACLS, Network Access resources, App Tunnels, and so on to assign to the selected groups. Any resource on the system can be assigned to a group. The system limits apply; for example, only one webtop should be assigned to a group.
About Pool Assign
The Pool Assign agent can dynamically assign a local traffic pool; it provides this configuration element only: selection of a static pool.
In a per-session policy, the Pool Assign agent enables session-based pool selection from among valid pools in this priority order: a pool selected by an iRule that is defined for the virtual server takes precedence over any other; a static pool defined in the Pool Assign agent takes precedence over a static pool defined for the virtual server.
In a per-request policy, the Pool Assign agent enables request-based pool selection for reverse proxy (LTM+APM) only. In a per-request policy, the pool specified in Pool Assign agent is assigned.
About Resource Assign
The Resource Assign action assigns connection resources to a session.
A Resource Assign action provides these configuration elements and options:
- Network Access
- Specifies the names of one or more network access resources.
- Portal Access
- Specifies the names of one or more portal access resources.
- App Tunnel
- Specifies the names of one or more application tunnels.
- Remote Desktop
- Specifies the names of one or more remote desktops.
- SAML
- Specifies the names of one or more SAML resources.
About Route Domain and SNAT Selection
The Route Domain and SNAT Selection action enables dynamic assignment of a route domain and of SNAT.
A Route Domain and SNAT Selection action provides these configuration elements and options:
- Route Domain
- Specifies a route domain. Enables route domain-based policy routing, sending a user to another route domain based on the outcomes of previous branches in the access policy.
- SNAT
- Specifies a SNAT to provide secure network address translation (SNAT) to the self IP address
of the BIG-IP® device, or to choose from a pool of configured internal
addresses for SNAT. SNAT precedence is determined according to the following rules:
- First, if a SNAT is defined in a Network Access resource configuration, APM uses that SNAT.
- If there is no SNAT defined in the Network Access resource, or the resource is another type, the APM takes the SNAT from this assignment in the access policy.
- If there is no SNAT assigned in the access policy, the APM uses the SNAT from the virtual server definition.
About SSO Credential Mapping
The SSO Credential Mapping action caches the user name and password for use with single sign-on (SSO) applications in the enterprise. This action enables users to forward stored user names and passwords to applications and servers automatically, without having to input credentials repeatedly.
The SSO Credential Mapping action provides these configuration elements and options.
- SSO Token Username
- One of these:
- Username from Logon Page - when selected, the Tcl expression that APM® uses to obtain the username from session variables displays; it is read-only.
- sAMAccountName from Active Directory - when selected, the Tcl expression that APM uses displays; it is read-only.
- sAMAccountName from LDAP Directory - when selected, the Tcl expression that APM uses displays; it is read-only.
- Custom - when selected, the last-displayed Tcl expression remains in the entry field. This field can be edited; another Tcl expression can be entered.
- SSO Token Password
- One of these:
- Password from Logon Page - when selected, the Tcl expression that APM uses to obtain the username from session variables displays; it is read-only.
- Custom - when selected, the last-displayed Tcl expression remains in the entry field. This field can be edited.
About Variable Assign
The Variable Assign action can includes one or more entries. An entry specifies a variable and assigns a value to it.
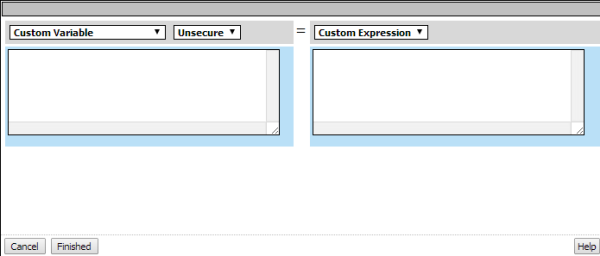
A variable assign entry screen as it displays initially
In the entry screen, the variable is specified in the left pane and the value is specified in the right pane.
A Variable Assign action provides these configuration elements and options for the variable:
- Custom Variable
- Specifies a variable name. It can be any name including the name of a session variable or
the name of a perflow variable. Note: For a per-session policy, when the policy runs it recognizes only existing perflow variables.
- Predefined Variables
- Specifies a predefined session variable or perflow variable name, which must be selected
from the Variable list. The type of variable (session or perflow) that
is available for selection depends on the selected Group:
Per-Session Variables or Per-Request Variables.
For Per-Request Variables, the Scratchpad, Custom, and Primary Category perflow variables are available for use in the per-request policy and in per-request policy subroutines. You can, for example, pass the value of a session variable into the per-request policy in one of these variables.
- Unsecure or Secure
- Specifies whether the variable is secure. A secure variable is stored in encrypted form in the session database. The value of a secure variable is not displayed in the session report, or logged by the logging agent.
A Variable Assign action provides these configuration elements and options for the value:
- Custom Expression
- Specifies a Tcl expression. The result of the expression is used as the value.
- AAA attribute
- Specifies the name of the attribute that contains the value:
- Agent Type - specifies the type of AAA server: AD, LDAP, or RADIUS.
-
Attribute Type - specifies the attribute type to use depending on
the agent type:
- Use user's attribute - for AD agent.
- Use user's primary group attribute - for AD agent.
- Use LDAP attribute - for LDAP agent.
- Use RADIUS attribute - for RADIUS agent.
- Agent type attribute name - specifies the name of the attribute that contains the value.
- Text
- Specifies a text string to use as the value. The text entered in this field is used as is.
- Session Variable
- Specifies the name of a session variable from which to get the value.
About VMware View Policy
A VMware View Policy action provides the ability to enable USB redirection for View desktop resources, and to pass Start Session Script Variables for VMware View connections for supported View clients.
A VMware View Policy action provides these configuration elements and options:
- USB redirection
-
- Disabled - Disables USB redirection. This is the default setting.
- Enabled - Enables USB redirection.
- VMware View Start Session Script Variables
- Specify variables and values to pass to the VMware View Connection Server (VCS) for use in a Start Session Script that you have configured on the VCS.
About Webtop, Links and Sections Assign
The Webtop, Links and Sections Assign action can assign a webtop, preconfigured webtop links, and webtop sections to a session.
A Webtop, Links and Sections Assign action provides these configuration elements and options:
- Webtop Links
- Specifies one or more webtop links. Note: Webtop links apply only to a full webtop.
- Webtop
- Specifies one webtop. This can be a full webtop, portal access webtop, or a network access webtop.
- Webtop Sections
- Specifies one or more webtop sections for grouping links on the webtop. Note: Webtop sections apply only to a full webtop.
About endpoint security client-side items
Endpoint security is a strategy for ensuring that a client device does not present a security risk before it is granted a remote access connection to the network.
Endpoint security verifies that desktop antivirus and firewall software is in place, systems are patched, keyloggers or other dangerous processes are not running, and sensitive data is not left behind in web caches and other vulnerable locations.
Configuring endpoint security (client-side) access policy items enables verification actions and other security-enhancing actions:
- On a Linux, Mac, or Windows client, client-side items can confirm that software meets requirements and can confirm the presence or absence of files and processes.
- On a Windows client, client-side items can confirm the registry, open a protected workspace, or perform cache and session control.
About client-side action requirements and alternatives
Endpoint security (client-side) access policy items require installation of client components. Access Policy Manager® uses ActiveX controls or browser plug-ins to collect information about client systems.
Not all clients support browser add-ons or allow browser software installation. For these clients, the server-side security process can inspect HTTP headers to gather information about the client operating system and browser type. The server-side Client Capability action determines whether a client is capable of running client-side actions.
About the Anti-spyware action
The Anti-spyware action checks for anti-spyware software on a client computer. When checking for multiple anti-spyware types, if one anti-spyware type matches the software on the client system, the action passes, regardless of other anti-spyware conditions that are specified in the item.
An Anti-spyware action provides these settings and options:
- Continuously check the result and end the session if it changes
- Specifies Enabled or Disabled. Note: When Enabled, if the client does not respond for five minutes, the server ends the session.
- Platform
- Specifies a platform. The default is Any. When a platform is
selected, the Vendor ID and Product ID lists update to include the products and vendors that
are supported for that platform according to the EPSEC package that is installed on the BIG-IP® system. Note: A link to a report that includes the anti-spyware software that Access Policy Manager® currently supports is available on the BIG-IP system Welcome page.
- Vendor ID
- Specifies a vendor ID (from the list of supported vendors) or Any.
- Product ID
- Specifies a product ID (from the list of supported products) or Any.
- State
- Specifies one of these states:
- Enabled When selected, the action verifies that the anti-spyware software is enabled
- Disabled When selected, the action verifies that the anti-spyware software is disabled.
- Unspecified When selected, the action does not verify the state of the software.
- Engine Version
- Specifies the engine version number; when specified the Anti-spyware action verifies this information.
- DB Version
- Specifies the database version number; when specified the Anti-spyware action verifies this information.
- DB Age Not Older Than (days)
- Specifies the database age in days; when specified the Anti-spyware action verifies this information.
- Last Scan Time Not Older Than (days)
- Specifies a number of days; when specified the Anti-spyware action verifies that the last scan did not occur more than the specified number of days ago.
About the Antivirus action
The Antivirus action checks for antivirus software on the client computer. When checking for multiple antivirus types, if one antivirus type matches the software on the client system, the action passes, regardless of other antivirus conditions that are specified in the action.
An Antivirus action provides these settings and options:
- Continuously check the result and end the session if it changes
- Specifies Enabled or Disabled. Note: When Enabled, if the client does not respond for five minutes, the server ends the session.
- Platform
- Specifies a platform. The default is Any. When a platform is
selected, the Vendor ID and Product ID lists update to include the products and vendors that
are supported for that platform according to the EPSEC package that is installed on the BIG-IP® system. Note: A link to a report that includes the antivirus software that Access Policy Manager® currently supports is available on the BIG-IP system Welcome page.
- Vendor ID
- Specifies a vendor ID (from the list of supported vendors) or Any.
- Product ID
- Specifies a product ID (from the list of supported products) or Any.
- State
- Specifies one of these states:
- Enabled - when selected, the action verifies that the antivirus software is enabled
- Disabled - when selected, the action verifies that the antivirus software is disabled.
- Unspecified - when selected, the action does not verify the state of the software.
- Version
- Specifies a version; when specified, the antivirus action verifies the version of the software.
- Engine Version
- Specifies the engine version number; when specified, the antivirus action verifies this information.
- DB Version
- Specifies the database version number; when specified, the antivirus action verifies this information.
- DB Age Not Older Than (days)
- Specifies the database age in days; when specified, the antivirus action verifies this information.
- Last Scan Time Not Older Than (days)
- Specifies a number of days; when specified, the antivirus action verifies that the last scan did not occur more than the specified number of days ago.
About the Firewall action
The Firewall action checks for firewall software on the client computer. When this action includes checks for multiple firewall types, if one firewall type matches the software on the client computer, the action passes, regardless of other firewall conditions that are specified in the action.
A firewall action provides these settings and options:
- Continuously check the result and end the session if it changes
- Specifies Enabled or Disabled. Note: When Enabled, if the client does not respond for five minutes, the server ends the session.
- Platform
- Specifies a platform. The default is Any. When a platform is
selected, the Vendor ID and Product ID lists update to include the products and vendors that
are supported for that platform according to the EPSEC package that is installed on the BIG-IP® system. Note: A link to a report that includes the firewall software that Access Policy Manager® currently supports is available on the BIG-IP system Welcome page.
- Vendor ID
- Specifies a vendor ID (from the list of supported vendors) or Any.
- Product ID
- Specifies a product ID (from the list of supported products) or Any.
- State
- Specifies one of these states:
- Enabled When selected, the action verifies that the firewall software is enabled
- Disabled When selected, the action verifies that the firewall software is disabled.
- Unspecified When selected, the action does not verify the state of the software.
- Version
- Specifies a version; when specified, the firewall action verifies the version of the software.
About Hard Disk Encryption
The Hard Disk Encryption action checks for hard disk encryption software on a client computer. When this action includes checks for multiple hard disk encryption types, if one of the specified hard disk encryption types matches the software on the client system, the action passes, regardless of other hard disk encryption conditions that are specified in the item.
A Hard Disk Encryption action provides these settings and options:
- Continuously check the result and end the session if it changes
- Specifies Enabled or Disabled. Note: When Enabled, if the client does not respond for five minutes, the server ends the session.
- Platform
- Specifies a platform. The default is Any. When a platform is
selected, the Vendor ID and Product ID lists update to include the products and vendors that
are supported for that platform according to the EPSEC package that is installed on the BIG-IP® system. Note: A link to a report that includes the hard disk encryption software that Access Policy Manager® currently supports is available on the BIG-IP system Welcome page.
- Vendor ID
- Specifies a vendor ID (from the list of supported vendors) or Any.
- Product ID
- Specifies a product ID (from the list of supported products) or Any.
- Encryption State
- Specifies one of these states:
- Enabled When selected, the action verifies that all disk volumes are encrypted on the client.
- Disabled When selected, the action verifies all disk volumes are not encrypted on the client.
- Unspecified When selected, the action verifies that hard disk encryption software is installed on the client.
- Version
- Specifies a version; when specified, the Hard Disk Encryption action verifies the version of the software.
About Linux File
The Linux File action can verify the presence of specific files and can verify one or more file properties in situations where doing so increases confidence in the security of the client system. If a file with the described properties exists, the access policy passes the client to the successful branch. If the file does not exist, or a file exists but one or more properties are not correct, the access policy passes the client to the fallback branch.
The Linux File action provides the following configuration elements and options:
- Continuously check the result and end the session if it changes
- Specifies Enabled or Disabled. Note: When Enabled, if the client does not respond for five minutes, the server ends the session.
- FileName
- Specifies the file name for which to check; for example csound.
- MD5
- Specifies the MD5 checksum. An MD5 checksum provides easily computable verification of the identity of a file using a cryptographic hash algorithm. The MD5 checksum is a 32-digit hexadecimal value. For example, the checksum for a zero-byte file is always d41d8cd98f00b204e9800998ecf8427e.
- Size
- Specifies the size of the file in bytes. The default value is 0 which
is the same as not specifying a size; a size of zero (0) is not verified. Note: A zero-byte file is specified with the MD5 checksum for a zero-byte file in the MD5 field.
- Date
- Specifies the file last modified date. Note: The date must be translated first to GMT, and then to a 24-hour clock.
About Linux Process
The Linux Process action can verify that one or more particular processes are or are not running on a client system.
The Linux Process action provides these configuration elements and options:
- Continuously check the result and end the session if it changes
- Specifies Enabled or Disabled. Note: When Enabled, if the client does not respond for five minutes, the server ends the session.
- Expression
- Specifies a Boolean expression to use to check for a process. The expression can include
these wildcards: * and ?, and parentheses ( ) to combine values, and the logical operators
AND, OR, and NOT. This is the syntax for a process check expression:
"process name" | (EXPRESSION) | NOT EXPRESSION | EXPRESSION AND
EXPRESSION | EXPRESSION OR EXPRESSION
Note: Double quotes (" ") are required around each process name.
Here is an example expression: "httpd" AND NOT "smtpd". Using this expression, the Linux Process action verifies that the HTTP daemon (httpd) is running on the system, and that the SMTP daemon (smtpd) is not running. Using another example expression, ("process1" OR "process2") AND "process3*", the action verifies the presence of either process1 or process2, and a process with a name that is process3 or starts with process3.
About Mac File
The Mac File action can verify the presence of specific files and can verify one or more file properties in situations where doing so increases confidence in the security of the client system. If a file with the described properties exists, the access policy passes the client to the successful branch. If the file does not exist, or a file exists but one or more properties are not correct, the access policy passes the client to the fallback branch.
The Mac File action provides the following configuration elements and options:
- Continuously check the result and end the session if it changes
- Specifies Enabled or Disabled. Note: When Enabled, if the client does not respond for five minutes, the server ends the session.
- FileName
- Specifies the file name for which to check; for example check.txt.
- MD5
- Specifies the MD5 checksum. An MD5 checksum provides easily computable verification of the identity of a file using a cryptographic hash algorithm. The MD5 checksum is a 32-digit hexadecimal value. For example, the checksum for a zero-byte file is always d41d8cd98f00b204e9800998ecf8427e.
- Size
- Specifies the size of the file in bytes. The default value is 0 which
is the same as not specifying a size; a size of zero (0) is not verified. Note: A zero-byte file is specified with the MD5 checksum for a zero-byte file in the MD5 field.
- Date
- Specifies the file last modified date. Note: The date must be translated first to GMT, and then to a 24-hour clock.
About Mac Process
The Mac Process action can verify that one or more particular processes are or are not running on a client system.
The Mac Process action provides these configuration elements and options:
- Continuously check the result and end the session if it changes
- Specifies Enabled or Disabled. Note: When Enabled, if the client does not respond for five minutes, the server ends the session.
- Expression
-
Specifies a Boolean expression to use to check for a process. The expression can include
these wildcards: * and ?, and parentheses ( ) to combine values, and the logical operators
AND, OR, and NOT. This is the syntax for a process check expression:
"process name" | (EXPRESSION) | NOT EXPRESSION | EXPRESSION AND
EXPRESSION | EXPRESSION OR EXPRESSION
Note: Double quotes (" ") are required around each process name.
Here is an example expression: "httpd" AND NOT "smtpd". Using this expression, the Mac Process action verifies that the HTTP daemon (httpd) is running on the system, and that the SMTP daemon (smtpd) is not running. Using another example expression, ("process1" OR "process2") AND "process3*", the action verifies the presence of either process1 or process2, and a process with a name that is process3 or starts with process3.
About Machine Cert Auth
A Machine Certificate Auth action can check for the existence of fields in a machine certificate to ensure that Windows and Mac client systems comply with your security policy.
| Client | Description |
|---|---|
| Windows | The Machine Cert Auth action accesses the machine certificate private key; admin privilege is required to do this. A user that runs without admin privilege cannot successfully run this check unless the machine certificate checker service is installed on the machine. (The Machine Certificate Checker Service is available for inclusion in the Windows client package from the Secure Connectivity area of Access Policy Manager®.) |
| Mac | The Machine Cert Auth action accesses the machine certificate private key. If the certificate is stored in a keychain other than user’s own keychain, such as the system keychain, then an ACL is required for non-admin users to be able to access this private key. |
The Machine Certificate Auth action provides the following configuration elements and options:
- Certificate Store Name
- Specifies the certificate store name that the action attempts to match. The certificate store can be a system store with a predefined name, such as MY, or a user-defined name. The store name can contain alphanumeric characters. The Machine Cert Auth action treats MY as the default store name for both Mac and Windows clients.
- Certificate Store Location
- Specifies the type and location of the store that contains the certificate, either the local
machine or the current user. For a Windows client, the store locations are in the following
registry locations:
- LocalMachine When specified, the action searches in HKEY_LOCAL_MACHINE for the machine certificate.
- CurrentUser When specified, the action searches in HKEY_CURRENT_USER for the machine certificate.
- LocalMachine When specified, the action searches in the keychain specified in Certificate Store Name in the system preference domain.
- CurrentUser When specified, the action searches in the keychain specified in Certificate Store Name in the user preference domain.
- If Certificate Store Name is set to System.keychain and Certificate Store Location is set to LocalMachine, the action searches for the machine certificate in /Library/Keychains/System.keychain.
- If Certificate Store Name is set to login.keychain and Certificate Store Location is set to CurrentUser, the action searches for the machine certificate in /Library/Keychains/login.keychain and then searches for the machine certificate in /Users/username/Library/Keychains/login.keychain
- If Certificate Store Name is set to MY then the action searches for the machine certificate in the default keychain of Certificate Store Location.
- CA Profile
- Specifies the certificate authority profile for the particular machine certificate.
- Save Certificate in a session variable
- Specifies Enabled or Disabled. When Enabled, specifies that the complete encrypted text of the machine certificate be saved in a session variable, session.check_machinecert.<name>.cert.cert.
- Allow User Account Control right elevation prompts
- Specifies Yes or No. When set to
Yes, a UAC prompt for users with admin-level privileges is allowed.
When set to No the UAC prompt for non-admin users is suppressed, which
can cause a failure to verify the machine certificate. This setting does not affect users
without admin-level privileges. If the Machine Certificate Checker Service is installed and
Allow User Account Control right elevation prompts is set to
Yes, the following scenarios occur:
- Users with administrator privilege are prompted for UAC.
- Standard users who use Machine Certificate Checker service will not be prompted for UAC.
- Guest users who use Machine Certificate Checker service will not be prompted for UAC.
- Users with administrator privilege are not prompted for UAC.
- Standard users who use Machine Certificate Checker service will not be prompted for UAC.
- Guest users who use Machine Certificate Checker service will not be prompted for UAC.
- Users with administrator privilege are prompted for UAC.
- Standard users will fail to verify machine certificate.
- Guest users will fail to verify machine certificate.
- Users with administrator privilege will fail to verify machine certificate.
- Standard users will fail to verify machine certificate.
- Guest users will fail to verify machine certificate.
- Match Subject CN with FQDN
- Specifies Yes or No. When set to Yes, specifies that the common name in the machine certificate matches the computer's fully qualified domain name (FQDN) such as, CHR-L-SMITH2.MARKETING.SITEREQUEST.COM.
- Match subject Alt Name with FQDN
- Specifies a regular expression used to extract content from the first subgroup matched in
the Subject Alternative Name, and then to compare the extracted content with the machine's
FQDN. Note: The order of RDNs is the same as is displayed; the required separator is a comma , .Here are some examples of regex extraction.
- Partial extraction. For example, .*DNS Name=([^,]+).*" or .*Other Name:Principal Name=([^,]+).*. For a regular expression .*DNS Name=([^,]+).*, the value of the DNS Name field is extracted for matching.
- Whole extraction. Using (.*) specifies that the entire SubjectAltName content be extracted for matching.
- Match Issuer
- Specifies a regular expression that is used to match the Issuer content against the
specified pattern. Note: The order of RDNs is the same as is displayed; the required separator is a comma , .Here are some examples of regex extraction.
- Partial match. CN=.*, OU=FP, O=F5, L=San Jose, S=CA, C=US
- Exact match. E=test@f5.com, CN=f5clientrootcert, OU=es, O=f5, L=london, S=chertsey, C=uk
- Match Serial Number
- Specifies a serial number that must be an exact match for the certificate serial. The hex string must be specified in the same order as it is displayed by OpenSSL and Windows certificate tools. For example, 33:AA:7B:82:00:01:00:00:00:33.
About Machine Info
The Machine Info action retrieves MAC addresses for network adapters on Mac, Linux, and Windows clients. It retrieves additional information on Windows clients
After retrieving the information, the Machine Info action creates session variables and stores the values in them. Session variables can be used in Tcl expressions and are also available for configuring an expression using the expression builder pull-down menu item Machine Info.
The Machine Info action collects the following information and creates the following session variables.
| Information | Session variable name |
|---|---|
| CPU Name | session.machine_info.cpu.name |
| CPU Vendor ID | session.machine_info.cpu.vendor |
| CPU Description | session.machine_info.cpu.description |
| CPU maximum clock | session.machine_info.cpu.max_clock |
| Motherboard manufacturer | session.machine_info.motherboard.manufacturer |
| Motherboard serial number | session.machine_info.motherboard.sn |
| Motherboard product | session.machine_info.motherboard.product |
| BIOS manufacturer | session.machine_info.bios.manufacturer |
| BIOS serial number | session.machine_info.bios.sn |
| BIOS version | session.machine_info.bios.version |
| Number of network adapters | session.machine_info.net_adapter.count |
| First network adapter name | session.machine_info.net_adapter.list.0.name |
| Second network adapter name | session.machine_info.net_adapter.list.1.name |
| First network adapter MAC address (Collected from Linux, Mac, and Windows clients) | session.machine_info.net_adapter.list.0.mac_address |
| Second network adapter MAC address (Collected from Linux, Mac, and Windows clients) | session.machine_info.net_adapter.list.1.mac_address |
| Number of hard drives | session.machine_info.hdd.count |
| First hard drive model number | session.machine_info.hdd.list.0.model |
| Second hard drive model number | session.machine_info.hdd.list.1.model |
| First hard drive serial number | session.machine_info.hdd.list.0.sn |
| Second hard drive serial number | session.machine_info.hdd.list.1.sn |
About Patch Management
The Patch Management action can check for patch management software on the client system. When this action includes checks for multiple patch management types, if one specified type matches, the action passes, regardless of other conditions that are specified in the action.
The Patch Management action provides the following configuration elements and options:
- Continuously check the result and end the session if it changes
- Specifies Enabled or Disabled. Note: When Enabled, if the client does not respond for five minutes, the server ends the session.
- Platform
- Specifies a platform. The default is Any. When a platform is
selected, the Vendor ID and Product ID lists update to include the products and vendors that
are supported for that platform according to the EPSEC package that is installed on the BIG-IP® system. Note: A link to a report that includes the antivirus software that Access Policy Manager® currently supports is available on the BIG-IP system Welcome page.
- Vendor ID
- Specifies a vendor ID (from the list of supported vendors) or Any.
- Product ID
- Specifies a product ID (from the list of supported products) or Any.
- Automatic Updates
- Specifies one of these values:
- Enabled When selected, the action verifies that patch management software is running on the client system.
- Disabled When selected, the action verifies that patch management software is not running on the client system.
- Unspecified When selected, the action does not perform either verification.
- Version
- Specifies a version; when specified, the Patch Management action verifies the version of the software.
- Max Allowed No. of Missing Critical Updates
- Specifies a number; when specified, the action verifies that the number of missing critical updates for the software is less than this number.
About Peer-to-Peer
The Peer-to-Peer action checks for peer-to-peer software on the client system.
The Peer-to-Peer action provides these configuration elements and options:
- Continuously check the result and end the session if it changes
- Specifies Enabled or Disabled. Note: When Enabled, if the client does not respond for five minutes, the server ends the session.
- Check for software in the list, and
- Specifies one of these options:
- pass if at least one listed software matches When selected, the action sends traffic to the successful branch if at least one software item in the list matches the software that is present on the client system.
- fail if unlisted software found -When selected, the action sends traffic to the fallback branch when any software that is not included in the list is found on the system. In this case, the list functions as a whitelist; if any endpoint software is found on the client system that is not included in the list, the check fails and traffic goes to the fallback branch.
- fail if any listed software matchesWhen selected, the action sends traffic to the fallback branch when any software item in the list is found on the client system. In this case, the list functions as a blacklist.
- Platform
- Specifies a platform. The default is Any. When a platform is
selected, the Vendor ID and Product ID lists update to include the products and vendors that
are supported for that platform according to the EPSEC package that is installed on the BIG-IP® system. Note: A link to a report that includes the peer-to-peer software that Access Policy Manager® currently supports is available on the BIG-IP system Welcome page.
- Vendor ID
- Specifies a vendor ID (from the list of supported vendors) or Any.
- Product ID
- Specifies a product ID (from the list of supported products) or Any.
- State
- Specifies one of these values:
- Enabled When selected, the action verifies that peer-to-peer software is running on the client system.
- Disabled When selected, the action verifies that peer-to-peer software is not running on the client system.
- Unspecified When selected, the action does not verify the state.
- Version
- Specifies a version; when specified, the Peer-to-Peer action verifies the version of the software.
About Windows Cache and Session Control
The Windows Cache and Session Control action can clean up after and control a session in a number of ways.
The Windows Cache and Session Control action provides these configuration elements and options:
- Clean temporary Internet files and cookies
- Specifies Disabled or Enabled. When set to Enabled, the action deletes temporary files and cookies after logout.
- Clean forms and passwords autocomplete data
- Specifies Disabled or Enabled. When set to Enabled, the action clears autocomplete entries in forms and fields after logout.
- Empty Recycle Bin
- Specifies Disabled or Enabled. When set to Enabled, the action empties the system Recycle Bin after logout.
- Force session termination if the browser or Webtop is closed
- Specifies Disabled or Enabled. When set to Enabled, the action forces the session to terminate after the browser or Webtop is closed.
- Remove dial-up entries used by Network Access client
- Specifies Disabled or Enabled. When set to Enabled, the action removes dial-up networking entries after logout.
- Terminate session on User Inactivity
- Specifies Disabled or n minutes, or n hours or Custom and a number of minutes. When not set to Disabled, the action terminates the session after the specified amount of time elapses.
- Lock workstation on User Inactivity
- Specifies Disabled or n minutes, or n hours or Custom and a number of minutes. When not set to Disabled, the action locks the workstation after the specified amount of time elapses.
About the Windows File action
A Windows File action can verify the presence of specific files and can verify one or more file properties in situations where doing so increases confidence in the security of the client system. If a file with the described properties exists, the access policy passes the client to the successful branch. If the file does not exist, or a file exists but one or more properties are not correct, the access policy passes the client to the fallback branch.
The Windows File action provides the following configuration elements and options:
- Continuously check the result and end the session if it changes
- Specifies Enabled or Disabled. Note: When Enabled, if the client does not respond for five minutes, the server ends the session.
- FileName
- Specifies the file name for which to check; for example, notepad.exe can be used to check for Windows Notepad.
- MD5
- Specifies the MD5 checksum. An MD5 checksum provides easily computable verification of the identity of a file using a cryptographic hash algorithm. The MD5 checksum is a 32-digit hexadecimal value. For example, the checksum for a zero-byte file is always d41d8cd98f00b204e9800998ecf8427e.
- Size
- Specifies the size of the file in bytes. The default value is 0 which
is the same as not specifying a size; a size of zero (0) is not verified. Note: A zero-byte file is specified with the MD5 checksum for a zero-byte file in the MD5 field.
- Signer
- Specifies the signer for the file. This can be left blank to omit checking for a signer.
- Date
- Specifies the file last modified date. Note: The date must be translated first to GMT, and then to a 24-hour clock.
- Version
- Specifies the version of the file. This can be left blank to omit checking for a version.
- Version Comparison
- Specifies the version comparison operator:
- = Specifies that the version to check for is the exact version specified in the Version field.
- < Specifies that the version to check for is a higher number than the version number specified in the Version field.
- > Specifies that the version to check for is a lower number than the version number specified in the Version field.
About Windows Health Agent
The Windows Health Agent action checks for health agent software on Windows-based client systems. When this action includes checks for multiple health agent types, if one specified type matches the software on the client system, the action passes, regardless of other health agent conditions that are specified in the action.
A Windows Health Agent action provides these settings and options:
- Continuously check the result and end the session if it changes
- Specifies Enabled or Disabled. Note: When Enabled, if the client does not respond for five minutes, the server ends the session.
- Vendor ID
- Specifies a vendor ID (from the list of supported vendors) or Any.
- Product ID
- Specifies a product ID (from the list of supported products) or Any.
- Version
- Specifies a version; when specified, the Windows Health Agent action verifies the version of the software.
- Policy Compliance
- Specifies one of these values:
- Enabled - when selected, the action verifies that the client is compliant with the health policy specified by the site administrator.
- Disabled - when selected, the agent verifies that the client is out of compliance with the health policy specified by the site administrator.
- Unspecified - when selected, that action does not check for policy compliance.
About Windows Info
The Windows Info action determines whether the client uses particular versions of the Windows operating system and has applied specific patches or updates to Windows. The Windows Info action supplies several default branch rules for various Windows operating system versions or Windows operating system version and service pack combinations.
The Windows Info action supplies these conditions for defining branch rules.
About Windows Process
The Windows Process action can verify that one or more particular processes are or are not running on a client system.
The Windows Process action provides these configuration elements and options:
- Continuously check the result and end the session if it changes
- Specifies Enabled or Disabled. Note: When Enabled, if the client does not respond for five minutes, the server ends the session.
- Expression
- Specifies a Boolean expression to use to check for a process. The expression can include
these wildcards: * and ?, and parentheses ( ) to combine values, and the logical operators
AND, OR, and NOT. This is the syntax for a process check expression:
"process name" | (EXPRESSION) | NOT EXPRESSION | EXPRESSION AND
EXPRESSION | EXPRESSION OR EXPRESSION
Note: Double quotes (" ") are required around each process name.
Here is an example expression: ("winlogon.exe" AND "GoogleDesktop.exe") AND NOT "gator*". The expression checks running Windows processes for the presence of the winlogon.exe and GoogleDesktop.exe processes and the absence of any process with gator in the name.
About Windows Protected Workspace
The Windows Protected Workspace action configures a temporary Windows user workspace for a session. This workspace contains temporary Desktop and My Documents folders. The protected workspace control deletes the temporary workspace and all of the folder contents at the end of the session.
- Close Google Desktop Search
- Specifies whether to close Google Desktop Search before starting protected workspace.
- Allow user to temporarily switch from Protected Workspace
- Specifies whether a user can switch from the protected workspace. When set to Enabled, the action provides a link so that the user can temporarily switch from the protected workspace.
- Allow user to use printers
- Specifies whether a user can use printers.
- Allow write access to USB flash drives
- Specifies whether a user can write from the protected workspace to USB flash drives:
- Disabled does not allow users to write to any USB flash drives from the protected workspace.
- All USB flash drives allows a user to write to any USB flash drive from the protected workspace.
- Only IronKey Secure Flash Drives allows a user to write only to specialized, highly secured flash drives created by IronKey, Inc., from the protected workspace.
- Allow user to burn CDs
- Specifies whether a user can burn CDs from within the protected workspace.
- Allow user to choose storage location
- Specifies whether a user can choose the storage location for protected workspace files:
- Enabled allows users to select a storage location.
- Disabled stores files in the user's Document and Settings directory.
- Enable persistent storage
- Specifies whether data is saved on the system after the Protected Workspace session is closed:
- Enabled allows users to save encrypted data from the Protected Workspace session on the local system after the session exits. The files are automatically decrypted and available in the next Protected Workspace session.
- Disabled prevents users from storing Protected Workspace data in persistent storage.
- Password protect new storage
- Specifies whether the protected workspace requires a password to access data in persistent
storage.
- Enabled requires the user to set a password to access persistent storage data.
- Disabled uses the default encryption and decryption, which is based on the server group name and storage device volume serial number.
- Server group name
- Specifies a group name for the server. This name is arbitrary, but limits persistent storage to that group name. For example, if a user connects to a protected workspace on a server with group name GroupA, and persistent storage is enabled, the user data is available when reconnecting to a server with the group nameGroupA. However, if the user then connects to a server with persistent storage enabled, and the server group name GroupB, persistent data from the GroupAProtected Workspace session is not available in the new session, and a new persistent storage is defined
About Windows Registry
The Windows Registry action verifies the existence or absence of certain keys and values in the Windows system registry database based on user-entered key values or Boolean expressions. Windows Registry can also fetch the value of a key and store it in a session variable, provided that the client is configured to allow the value to be fetched.
The Windows Registry action provides these configuration elements:
- Continuously check the result and end the session if it changes
- Specifies Enabled or Disabled. Note: When Enabled, if the client does not respond for five minutes, the server ends the session.
- Expression
- Specifies a Boolean expression.
This is the syntax for registry checker expressions:
"key" comparison_operator data
"key"."value" >> "variable_name"
"key" ISPR
"key"."value" comparison_operator data
"key"."value" ISPR
- “key”
- Represents a path in the Windows registry. Quotation marks are required around the path. If quotation marks exist as part of the registry path, they should be doubled (requires two sets of quotation marks).
- “value”
- Represents the name of the value. Quotation marks are required. If quotation marks exist as part of the value name, they should be doubled (requires two sets of quotation marks).
- comparison_operator
- Represents a comparison operator (< <= > >= =) or ISPR. ISPR verifies that a
key or value is present. The equal sign (=) and the double equal sign (==) specify
equality. Note: Windows Registry does not support comparison of binary data.
- data
- Represents the content to compare against. Any spaces, commas, slashes, tabs, or other delimiters in the data must be enclosed in quotation marks. Data is interpreted as a version number when formatted like this: d.d[.d][.d]”, d,d[,d][,d] (where d is a number). Data is interpreted as a date when formatted like this: mm/dd/yyyy .
- >>
- This is the GET operator; it fetches the value of a key provided that the client is
configured to allow the value to be fetched.Note: The GET operator supports these Windows Registry data types only: REG_DWORD, REG_SZ, and REG_MULTI_SZ. The maximum recommended amount of data that a GET operator returns should be kept within 1 KB.All sub-expressions of a compound expression are evaluated even if they are joined by OR operators. Windows Registry values are sent to the server for successful fetch operations even if the overall expression is evaluated to false.
- "variable_name"
- Represents the variable into which the GET operator stores the value of the key. When a GET operation is successful, the registry value retrieved from the client is saved in a session variable in this format: session.windows_check_registry.last.data. variable_name. Quotation marks are required. The variable name can include alphanumeric symbols, underscores, dots, and hyphens only and must be no more than 64 characters long.
| Expression | Description |
|---|---|
| "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer"."Build">>"IEBuild" | Checks for the presence of the specified path in the registry and stores the value in the variable session.windows_check_registry.last.data. IEBuild. |
| "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\InternetExplorer"."Version">= "6.0.2900.2180" | Checks that the Internet Explorer version is greater than or equal to the value specified. |
| "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\InternetExplorer"."Version">= "5.0.2800.0" AND "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\InternetExplorer"."Version" >= "6.0.2900.0" | Checks for the presence of Internet Explorer. With this registry check, the Internet Explorer version must be greater than or equal to 5.0.2800.0, and less than or equal to 6.0.2900.0. |
About 32-bit registry keys on a 64-bit Windows client
On 64-bit Windows systems, the Windows Registry action can check for registry keys in the 64-bit registry or the 32-bit registry. The following registry root key names are supported:
- HKEY_CURRENT_USER
- HKEY_CURRENT_USER32
- HKEY_CURRENT_USER64
- HKEY_LOCAL_MACHINE
- HKEY_LOCAL_MACHINE32
- HKEY_LOCAL_MACHINE64
- HKEY_CLASSES_ROOT
- HKEY_CLASSES_ROOT32
- HKEY_CLASSES_ROOT64
- HKEY_USERS
- HKEY_USERS32
- HKEY_USERS64
An HKEY value specified with a 32 can provide a 32-bit view of a 64-bit registry. This is the perspective used by 32-bit applications running on a 64-bit operating system. An HKEY value specified with a 64 can provide a 64-bit view of the registry. This is the perspective used by native 64-bit applications.
Keys without a bit value specified use the default Windows registry redirectors, as specified by Microsoft. On a 32-bit Windows system, the number of bits specified in a registry key name is ignored.
About endpoint security (server-side) access policy items
In endpoint security (server-side) actions, the server queries clients and makes policy decisions based on information that a client presents to the server. For example, the Client Type action presents a query to find out what type of client is connecting, and routes the client to the different policy branches based on the results of the query. Endpoint security (server-side) access policy items do not require installation of client components.
About Client for MS Exchange
The Client for MS Exchange action determines whether a client is using Microsoft Exchange or ActiveSync protocols. This action includes two default branches: Client for MS Exchange and fallback. The Client for MS Exchange branch indicates that the client uses the Microsoft Exchange or ActiveSync protocol. A client for Microsoft Exchange is not a typical web browser and Access Policy Manager® (APM®) has the following restrictions on Client for MS Exchange access policy branches.
- Behavioral restrictions
-
- APM does not attempt to perform authentication retries.
- A logon page action automatically works in clientless mode. (The access policy must include a logon page action.)
- Except for the logon page, APM cannot provide responses that require additional user input.
- Limited supported actions
- Microsoft Exchange devices support only the following actions. Therefore, only these
actions are supported on a Client for MS Exchange access policy branch.
- Authentication actions:
- AD Auth
- AD Query
- Client Cert Inspection
- HTTP Auth
- LDAP Auth
- LDAP Query
- NTLM Auth
- RADIUS Auth
- RADIUS Accounting
- RSA SecurID Authentication
- Endpoint security (server-side) actions:
- Client-Side Capability
- Client OS
- Landing URI
- IP Geolocation Match
- Authentication actions:
About Client OS
The Client OS action detects the operating system of the remote client. Access Policy Manager® detects this using information from the HTTP header. The action provides separate branches for separate operating systems. This action can be very useful at the beginning of an access policy. Each branch can include actions that are specific to a client operating system.
This figure shows the Client OS action and default branches, configured to allow access to clients on the Windows RT operating system and to deny access to all others.
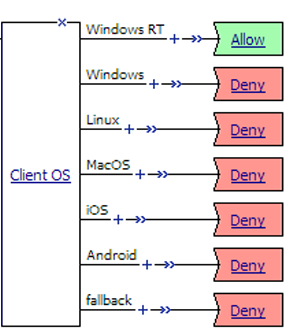
Client OS item with Allow ending configured on Windows RT branch
About Client Type
The Client Type action determines whether the client is using a full browser, the BIG-IP® Edge Client, or another client to access the Access Policy Manager® (APM®). This action makes it possible to specify different actions for different client types in one access policy and, as a result, to use one virtual server for traffic from different client types. This figure shows the Client Type action as it looks when first added to an access policy.
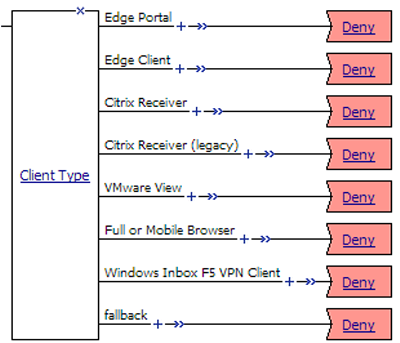
Client Type
By default, the Client Type action includes these branches:
- Edge Portal
- Indicates that the user is connecting with the BIG-IP® Edge Portal® mobile app.
- Edge Client
- Indicates that the user is connecting with the BIG-IP® Edge Client® or BIG-IP Edge Client app, supported on multiple devices and operating systems.
- Citrix Receiver
- Indicates that the user is connecting using a later Citrix Receiver client.
- Citrix Receiver (legacy)
- Indicates that the user is connecting using an earlier Citrix Receiver client (identified with PN Agent).
- VMware View
- Indicates that the user is connecting using a VMware Horizon View client.
- Full or Mobile Browser
- Indicates the user is connecting with a Windows web browser or a mobile browser.
- Windows Inbox F5 VPN Client
- Indicates the user is connecting using the Windows Inbox F5 VPN client.
- fallback
- Indicates the user is connecting with another method.
APM supports the client types on multiple operating systems. Refer to AskF5™ (support.f5.com) to look up the supported operating systems and versions in the compatibility matrix for your version of APM.
About Client-Side Capability
The Client-Side Capability action determines whether the client is fully capable of running endpoint security (client-side) actions. The Client-Side Capability action includes two branches.
| Branch | Description |
|---|---|
| Full | Indicates that the user is connecting with a client that has full client-side check support. |
| fallback | Indicates that the user is connecting with a client that does not fully support client-side checks. |
This action can be very useful as one of the first checks in an access policy. The Full branch can include the required client-side checks for those clients that are capable, while the fallback branch can lead to access policy branches for other clients.
This figure shows an example in which the Client-Side Capability action is used to verify that the client is capable of running a client-side check before running the client-side check for anti-spyware software.
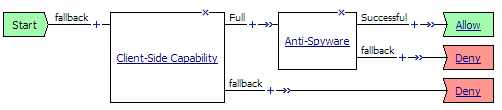
Client-side capability check before a client-side check
About the Date Time action
The Date Time action checks the date or the time to support date- and time-based access. The Date Time action provides two default branch rules:
The Date Time action provides these conditions for defining branch rules.
- Time From
- Specifies a time of day. The condition is true at or after the specified time.
- Time To
- Specifies a time of day. This condition is true before or at the specified time.
- Date From
- Specifies a date. This condition is true at or after the specified date.
- Date To
- Specifies a date. This condition is true before or at the specified date
- Day of Week
- Specifies a day. The condition is true for the entire day (local time zone).
- Day of Month
- Specifies the numeric day of month. This condition is true for this day every month (local time zone).
About IP Geolocation Match
The IP Geolocation Match action determines a user's physical location by comparing the user's IP address to an internal database. The IP Geolocation Match action can make a match based on one or more location parameters.
The default branch rule is IP Geolocation Country code is US.
The IP Geolocation Match action provides these conditions for defining branch rules.
- IP Geolocation Continent code is
- Specifies that the user’s IP address must match the specified continent code.
- IP Geolocation Country code is
- Specifies that the user’s IP address must match the specified country code.
- IP Geolocation Country name is
- Specifies that the user’s IP address must match the specified country name.
- IP Geolocation State/Region is
- Specifies that the user’s IP address must match the specified region or state.
About IP Reputation
When an IP Reputation action is included in an access policy, Access Policy Manager® (APM®) searches for the IP address in the IP intelligence database. The IP intelligence database contains only IP addresses that are considered untrustworthy, along with a category for each that describes why it is not trusted.
APM provides these default branch rules for the IP Reputation action.
- Bad
- The IP address exists in the IP intelligence database. The expression for this branch rule includes every IP reputation category. For example, the rule includes expressions such as IP Reputation is: Spam Sources OR IP Reputation is: Proxy, and so on. If any IP reputation category is acceptable at your site, you should update this rule or create and use another rule.
- Good
- The IP address is not found in the IP intelligence database.
- fallback
- The IP intelligence database is inaccessible for some reason. This can be due to a misconfiguration or a problem with a license or Internet connectivity.
About IP Subnet Match
The IP Subnet Match action determines whether the client IP address matches an IP subnet. The IP Subnet Match action provides this configuration option:
IP Subnet Match - specifies a subnet, such as 10.0.0.0/8.
About Jailbroken or Rooted Device Detection
About Landing URI
The Landing URI action checks the landing URI with which the user accessed the access policy. The default Landing URI action includes two branches.
| Branch | Description |
|---|---|
| Landing URI | Indicates that the user is connecting with a URI that matches a specified landing URI. Specifies /uri1 or /uri1/ as the default landing URI. To use this action, it is required to edit the branch rules to specify an actual landing URI. |
| fallback | Indicates that the user is connecting with a different landing URI. |
This figure shows a branch rule that determines whether the address that the user typed includes the string /owa or /owa/, either of which is part of the typical landing URI for an Outlook Web Access connection.
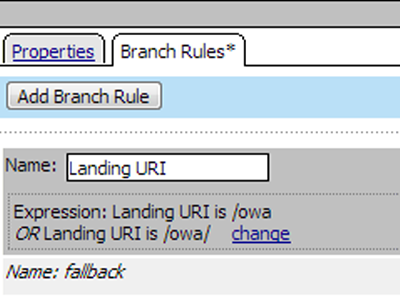
Landing URI branch rule with updated expression
About the License action
The License action provides the ability to create branch rules based on license use. It can check the number of remaining licenses against an absolute value or the percentage of licenses remaining against a threshold. A License action can check access licenses, connectivity licenses, and concurrent users.
The License action supplies the default branch rule - Remaining Global Access license count is above percentage threshold: 20. This branch rule can be deleted or changed. The License action supplies these conditions for configuring branch rules:
- Remaining Global Access License count is above absolute value - checks number of remaining global access licenses against the number that you specify.
- Remaining Global Access License count is above percentage threshold - checks percentage of global access licenses that remain against the threshold that you specify.
- Remaining Global Connectivity License count is above absolute value - checks number of remaining global connectivity licenses against the number that you specify.
- Remaining Global Connectivity License count is above percentage threshold - checks percentage of global connectivity licenses that remain against the threshold that you specify.
- Remaining Concurrent User count is above absolute value - checks number of remaining access licenses for the access profile against the number that you specify.
- Remaining Concurrent User count is above percentage threshold - checks percentage of concurrent access licenses for the access profile that remain against the threshold that you specify.
If the license check does not match the specified conditions, the access policy sends the user to the fallback branch.
About general purpose items
General purpose items can be used in any case and can be placed anywhere in an access policy. These items support:
- Logging a message and variables
- Sending email
- Displaying a message
- Processing an iRule
- Providing a choice between two options
- Running user-configured rules
- Reading from and writing to a local user database
When an administrator adds these items to an access policy, the administrator specifies the message (to log, to display, to email), any options that a user can choose, the iRule to process, and so on, to suit the situation.
About the Decision Box action
A Decision Box action presents two options to the user. These options are presented as link text, preceded by images.
A Decision Box action can be useful after a client fails an endpoint security check, or after a user fails to authenticate. When this occurs, a branch rule can provide an option to allow the user to continue onto a guest or quarantine network that provides only limited access to a segregated subnet. The other branch can provide an option to log out, and present the user with a logon denied ending.
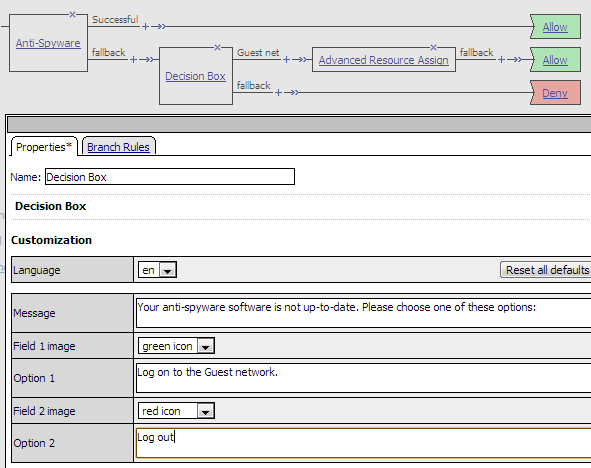
Configuring a decision box to appear after a failed endpoint security check (with decision box detail)
Another use of the Option 2 branch is to allow the user to continue to a redirect ending that takes the user to a helpful URL, for example, to the web site of an antivirus vendor to download virus database updates.
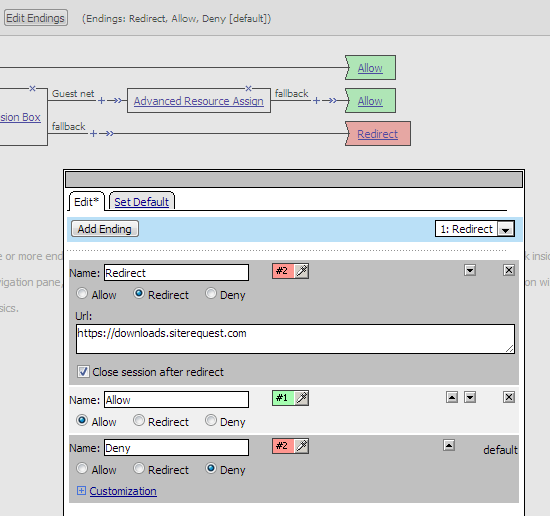
Redirect ending as the second option with configuration detail
About the Email action
An Email action can send email. An Email action provides these configuration options and elements:
- SMTP Configuration
- Specifies an SMTP configuration on the BIG-IP® system.
- From
- Specifies the sender which can be a string or a session variable name or both. For example: APM@vs-%{session.server.network.name}
- To
- Specifies the recipient. This can be a fully qualified email address or a session variable name; for example: %{session.ad.last.attr.mail}
- CC
- Specifies recipients to be copied on the mail. This can be fully qualified email addresses or session variable names.
- Subject
- Specifies the subject of the email message. This can be a string, a session variable name, or a combination of strings and session variable names.
- Message
- Specifies the message to send. This can be a string, a session variable name, or a combination of strings and session variable names.
About the Empty action
An Empty action has no explicit configuration. The action allows a user to create rules only, using the Branch Rules tab.
About iRule Event
An iRule Event action adds iRule processing to an access policy or to a per-request policy subroutine at a specific point. An iRule Event provides one configuration option: ID, which specifies an iRule event ID.
An iRule Event action can occur anywhere in an access policy or a per-request policy subroutine.
About Local Database
The Local Database action can read and write information about a user in a local user database.
A Local Database action provides the following configuration elements and options:
- LocalDB Instance
- Specifies a local user database instance from a list.
- User Name
- Specifies a user name from a list. Note: The same user name can exist in more than one local user database.
- Allow User Create
- Specifies whether to create a user dynamically when trying to write information for a
user that is not in the database already. Note: Dynamically created users exist temporarily and are regularly purged from the database. Static users, created by an administrator using the Configuration Utility or the command line, are not purged.
- Add new entry
- Specify actions that read from and write to specific database properties.
An entry includes these elements:
- Action
- Specifies Read or Write.
- Destination
- Specifies where to store the value that is being read or written.For the
Read action, Destination specifies a
variable; the value that is read from the database is stored in this variable. The
default variables are:
- session.localdb.groups
- session.localdb.locked_out
-
session.localdb.login_failures
Note: Alternatively, the variable can be any text string. When using non-default variables, verify the expressions used in any other item that reads or manipulates local database variables in the same session; ensure that the expressions use the same string.
- locked_out - a number; when 0, the user is not locked out. When greater than 0, the user is locked out.
- login_failures - a number; the number of login failures currently recorded for the user.
-
groups - text; names of membership groups specified for the
user in the local user database. Note: Groups specified in the local user database are not verified against external systems.
- Source
- Specifies where to get the value to read or to write. For Read, specifies a database property (selectable from a list) to read. For Write, specifies an expression, the value of which will be written.
About the Logging action
The Logging action can be used in an access policy or in a per-request policy. In an access policy, the Logging action adds logging for session variables to the access policy. In a per-request policy, the Logging action can add logging for both session variables and per flow variables to the per-request policy.
This action is useful for tracing the variables that are created for a specific category, or in a specific branch.
The Logging action provides these configuration elements and options:
- Log Message
- For an access policy, specifies text to add to the log file. For a per-request policy,
specifies the message text and the session and per-flow variables to add to the message.
Complete variable names must be typed. Wildcards are not supported for per-request policies. An
example log message for a per-request policy follows.
The system found this URL %{perflow.category_lookup.result.url} in these categories %{perflow.category_lookup.result.categories} and placed it into this category %{perflow.category_lookup.result.primarycategory}.An HTTPS request was made to this host %{perflow.category_lookup.result.hostname}; the per-request policy set SSL bypass to %{perflow.ssl_bypass_set}.Requests from this platform %{session.client.platform} were made during this session %{perflow.session.id}. - Session Variables
- Specifies a session variable from a list of predefined session variables or a custom session
variable. Note: This option is available only when adding the Logging action to an access policy.
About the Message Box action
A Message Box action presents a message to the user, and prompts the user to click a link to continue. The message box has no effect on the user's access to the network or the preceding or following access policy checks. A message box can be used, for example, to warn a user about a redirect to a guest network, or that the client certificate failed to authenticate, or to display a message about the results of a rule branch in the access policy.
A Message Box action provides these configuration elements and options:
- Language
- Specifies the language to use to customize this logon page. When a user selects a language,
the content in the remaining fields display in the selected language.Note: Languages on the list reflect those that are configured in the access profile.
- Message
- Specifies the message to present to the user.
- Link
- Specifies the message that appears as the link text.
About authentication items
Authentication items perform authentication or authentication-related functions, such as:
- Verify credentials (or a PIN or a token)
- Inspect SSL certificates
- Check SSL certificate revocation status
- Verify the result of passwordless authentication
- Perform accounting, and so on.
An authentication item usually follows a logon item or another authentication item in an access policy. An access policy can contain any number of authentication items.
An administrator that configures authentication items can make these choices:
- Specify an AAA server (or pool in cases where high availability is supported) against which to authenticate. Access Policy Manager® (APM®) supports many types of AAA servers.
- Inspect the SSL certificate presented during the initial SSL handshake, or specify on-demand certificate authentication (to re-negotiate the SSL connection). On-demand authentication is not supported in every type of access configuration.
- Select a Certificate Revocation Location (CRL) or Online Certificate Status Protocol (OCSP) responder for verifying revocation status.
About AD Auth
An AD Auth action authenticates a user against an AAA Active Directory server. An authentication action typically follows a logon action that collects credentials.
- Type
- Specifies Authentication, the type of this Active Directory action.
- Server
- Specifies an Active Directory server; servers are defined in the area of the Configuration utility.
- Cross Domain Support
- Specifies whether AD cross domain authentication support is enabled for this action.
- Complexity check for Password Reset
- Specifies whether Access Policy Manager® (APM®)
performs a password policy check. APM supports these Active Directory password policies:
- Maximum password age
- Minimum password age
- Minimum password length
- Password must meet complexity requirements
Note: Because this option might require administrative privileges, the administrator name and password might be required on the AAA Active Directory server configuration page.Note: Enabling this option increases overall authentication traffic significantly because APM must retrieve password policies using LDAP protocol and must retrieve user information during the authentication process to properly check the new password. - Show Extended Error
- When enabled, causes comprehensive error messages generated by the authentication server to display on the user's logon page. This setting is intended only for use in testing, in a production or debugging environment. If enabled in a live environment, your system might be vulnerable to malicious attacks. (When disabled, displays non-comprehensive error messages generated by the authentication server on the user's logon page.)
- Max Logon Attempts Allowed
- Specifies the number of user authentication logon attempts to allow. A complete logon and
password challenge and response is considered as one attempt. Note: For a per-request policy subroutine, equivalent functionality is supported through subroutine settings.
- Max Password Reset Attempts Allowed
- Specifies the number of times that APM allows the user to try to reset password.
About AD Query
An AD Query action performs a query against an AAA Active Directory server. An AD Query action provides these configuration elements and options:
- Type
- Specifies Query, the type of this Active Directory action.
- Server
- Specifies an Active Directory server; servers are defined in the area of the Configuration utility.
- SearchFilter
- Specifies the search criteria to use when querying the Active Directory server for the user's information. Session variables are supported as part of the search query string.
- Fetch Primary Group
- Specifies whether to retrieve a user's primary group Distinguished Name for use in the access policy.
- Cross Domain Support
- Specifies whether AD cross domain authentication support is enabled for this action.
- Fetch Nested Groups
- When disabled, associates the user only to the groups to which they belong directly. When enabled, associates the user to all groups that are nested under the groups that they directly belong to. For example, if the user belongs to Group 1 and Group 2, and Group1 is a member of Group 3 and Group 4, enabling this setting allows the user to obtain privileges from all groups.
- Complexity check for Password Reset
- Specifies whether Access Policy Manager® (APM®)
performs a password policy check. APM supports these Active Directory password policies:
- Maximum password age
- Minimum password age
- Minimum password length
- Password must meet complexity requirements
Note: Because this option might require administrative privileges, the administrator name and password might be required on the AAA Active Directory server configuration page.Note: Enabling this option increases overall authentication traffic significantly because APM must retrieve password policies using LDAP protocol and must retrieve user information during the authentication process to properly check the new password. - Max Password Reset Attempts Allowed
- Specifies the number of times that APM allows the user to try to reset password.
- Prompt user to change password before expiration
- Specifies whether to warn the user at a set time before the password expires and provide the option to change the password.
About Client Cert Inspection
Normally, when a client makes an HTTPS request, an SSL handshake request occurs at the start of an SSL session. If the connection is allowed, the Client Cert Inspection action can check the result of the request.
The Client Cert Inspection action provides two branches: Successful and fallback.
About CRLDP Auth
A CRLDP Auth action retrieves a Certificate Revocation List (CRL) from a network location (distribution point). A distribution point is either an LDAP Uniform Resource Identifier (URI), a directory path that identifies the location where the CRLs are published, or a fully qualified HTTP URL. An CRLDP Auth action provides these configuration elements and options:
- CRLDP Server
- Specifies a CRLDP server; servers are defined in the area of the Configuration utility.
About HTTP Auth
About Kerberos Auth
A Kerberos Auth action retrieves user credentials using a Kerberos ticket.
A Kerberos Auth action provides these configuration elements and options:
- AAA Server
- Specifies a Kerberos server; servers are defined in the area of the Configuration utility.
- Request Based Auth
- Specifies whether per request based authentication is enabled. When disabled, authentication occurs only while executing the access policy.
- Max Logon Attempts Allowed
- Specifies the number of user authentication logon attempts to allow. A complete logon and
password challenge and response is considered as one attempt. Note: For a per-request policy subroutine, equivalent functionality is supported through subroutine settings.
About LDAP Query
An AD Query action performs a query against an AAA LDAP server. An AD Query action provides these configuration elements and options:
- Type
- Specifies Query, the type of this LDAP action.
- Server
- Specifies an LDAP server; servers are defined in the area of the Configuration utility.
- SearchFilter
- Specifies the search criteria to use when querying the LDAP server for the user's information. Session variables are supported as part of the search query string. When strings are used, they must be enclosed in parentheses; for example, (sAmAccountName=%{session.logon.last.username}).
- Fetch Nested Groups
- When disabled, associates the user to the groups that they directly belong to. When enabled, associates the user to all groups that are nested under the groups that they directly belong to. For example, if the user belongs to Group 1 and Group 2, and Group1 is a member of Group 3 and Group 4, enabling this setting allows the user to obtain privileges from all groups.
- Required Attributes (optional)
- By default, the server loads all user attributes if no required attributes are specified. However, system performance can improve if fewer attributes are returned.
About LocalDB Auth
The LocalDB Auth action can authenticate a user against a local user database instance. The LocalDB Auth action can lock a user out of a local user database instance if they fail to log on within a specified number of attempts.
A LocalDB Auth action provides these configuration elements and options.
About NTLM Auth Result
If NTLM authentication occurs, it happens before the access policy runs. The NTLM Auth Result action checks the result and provides two branches: Successful and fallback.
About the OAuth Authorization
When Access Policy Manager® (APM®) is configured to act as an OAuth authorization server, an OAuth Authorization agent must be present in the access policy.
The OAuth Authorization agent provides these elements and options.
- Prompt for Authorization
-
- Enabled - Displays the OAuth Authorization page. The page requests authorization for the client application to access a list of scopes and presents the options to allow or to deny access.
- Disabled - Does not display the OAuth Authorization page.
- Scopes
-
Specifies the scopes for which authorization is requested. If no scopes are specified here, the scopes configured in APM for the client application are used.
- Customization
- Customize the messages that display on the OAuth authorization page when Prompt
for Authorization is set to Enabled:
- Authorize Message Specifies the initial wording for the prompt.
- Scope Message Specifies the wording that precedes the list of scopes that are specified in the Scopes Assign area of this screen.
- Allow Message Provides the label for the button that allows access.
- Deny Message Provides the label for the button that denies access.
About OAuth Client
An OAuth Client agent is a policy item that requests authorization and tokens from an OAuth server. An OAuth Client can also validate tokens and get scope data on a per-request basis. The OAuth Client agent provides these configuration elements and options:
- Server
- Specifies the OAuth server to which this OAuth client directs requests.
- Grant Type
- Specifies the type of grant that the OAuth client uses.
- Authorization code - The client redirects the resource owner to the OAuth server to request an authorization code.
- Password - The client uses resource owner password credentials to request an access token from the OAuth server.
- Authentication Redirect Request
- Specifies an auth-redirect-request type request, which redirects a user to an OAuth server. Displays when Grant Type is set to Authorization code.
- Token Request
- Specifies a token-request type of request.
- Refresh Token Request
- Specifies a token-refresh-request type of request. APM uses this request on a per-request basis.
- Validate Token Request
- Specifies a validation-scopes-request type of request to validate a token and to get a list of scopes associated with a token. APM uses this request on a per-request basis.
- Redirection URI
- Specifies the URI for the OAuth server to redirect a user back to the OAuth client. Displays when Grant Type is set to Authorization code.
- Scope
- Specifies one or more strings separated by spaces; for example contacts photo
email. The strings are defined by the OAuth authorization server. Your best source
of information for the strings that a particular OAuth authorization server defines could be
APIs for OAuth 2.0 scopes on developer sites for OAuth providers.
For the Authorization code grant type, an OAuth authorization server prompts the user to grant or deny access to the scopes. For the Password grant type, an OAuth authorization server grants permission to the requested scopes based on the user providing resource owner password credentials.
About OAuth Scope
The OAuth Scope agent makes requests to an OAuth authorization server to get scopes associated with a token and to get scope data, such as a user's email address or contact list. The OAuth Scope item provides these elements and options:
- Server
- Specifies an OAuth server. (OAuth servers in resource server, or client and resource server modes are available for selection.)
- Scopes Request
- Specifies a validation-scopes-request type request. This request type retrieves a list of scopes associated with the token.
There can be multiple scope data requests in this agent with these elements:
- Scope Name
- Specifies the name of a scope for which you are requesting data. (The external OAuth provider specifies the names of the scopes that it supports.)
- Request
- Specifies a scope-data-request type request. This is optional. If the provider does not require this type of request to obtain additional information from an authorization server, you do not need to fill in this field.
About OCSP Auth
An OCSP Auth action retrieves the revocation status of an X.509 certificate by sending the certificate information to a remote Online Certificate Status Protocol (OCSP) responder. Typically, an OCSP Auth action follows an action that receives an X.509 certificate. Either a Client Cert Inspection or On-Demand Cert Auth action can receive the X.509 certificate from a user. Either action populates session variables with data that OSCP Auth uses. Similarly, a Machine Cert Auth action can receive an X.509 certificate from a machine and populate session variables.
An OCSP Auth action provides these configuration elements and options:
About On-Demand Cert Auth
Typically, when a client makes an HTTPS request, an SSL handshake request occurs at the start of an SSL session. If the client SSL profile skips the initial SSL handshake, an On-Demand Cert Auth action can re-negotiate the SSL connection from an access policy by sending a certificate request to the user. This prompts a certificate screen to open. After the user provides a valid certificate, the On-Demand Cert Auth action checks the result of certificate authentication. The agent verifies the value of the session variable session.ssl.cert.valid to determine whether authentication was a success.
The On-Demand Cert Auth action provides one configuration option, Auth Mode, with two supported modes:
- Request
- With this mode, the system requests a valid certificate from the client, but the connection does not terminate if the client does not provide a valid certificate. Instead, this action takes the fallback route in the access policy. This is the default option.
- Require
- With this mode, the system requires that a client provides a valid certificate. If the
client does not provide a valid certificate, the connection terminates and the client
browser stops responding. Note: For an iPod or an iPhone, the Require setting must be used for On-Demand certificate authentication. To pass a certificate check using Safari, the user is asked to select the certificate multiple times. This is expected behavior.
About OTP Generate
The OTP Generate action can generate a one-time use time-limited password. This action does not send the one-time password to a user. Typically, an OTP Generate action precedes other actions that send the password (the Email action, for example) and then verify it (OTP Verify action). The OTP Generate action provides these configuration options:
About OTP Verify
In an access policy, the OTP Verify action checks for a match between a user-entered password and the one-time password generated previously by the OTP Generate action. The OTP Verify action also verifies that the one-time password has not expired. The OTP Verify action provides this configuration option:
About SAML Auth
The SAML Auth action authenticates against an external SAML Identity Provider (IdP). This action is for use when the BIG-IP® system is configured as a SAML service provider and supports connections initiated at SAML service providers.
The SAML Auth action provides this configuration element:
About RADIUS Acct
A RADIUS Acct action reports user session information to an external RADIUS accounting server; it does not perform authentication.
A RADIUS Acct action provides these configuration elements and options:
About RADIUS Auth
A RADIUS Auth action authenticates a client against an external RADIUS server. A RADIUS Auth action provides these configuration elements and options.
- AAA Server
- Specifies the RADIUS accounting server; servers are defined in the area of the Configuration utility.
- Show Extended Error
- When enabled, causes comprehensive error messages generated by the authentication server to display on the user's logon page. This setting is intended only for use in testing, in a production or debugging environment. If enabled in a live environment, your system might be vulnerable to malicious attacks. (When disabled, displays non-comprehensive error messages generated by the authentication server on the user's logon page.)
- Max Logon Attempts Allowed
- Specifies the number of user authentication logon attempts to allow. A complete logon and
password challenge and response is considered as one attempt. Note: For a per-request policy subroutine, equivalent functionality is supported through subroutine settings.
About RSA SecurID
An RSA SecurID action authenticates a user name and PIN code or token against a SecurID server. In an access policy, an authentication action typically follows a logon action that collects credentials. An RSA SecurID action provides these configuration elements and options:
- AAA Server
- Specifies the RSA SecurID server; servers are defined in the area of the Configuration utility.
- Show Extended Error
- When enabled, causes comprehensive error messages generated by the authentication server to display on the user's logon page. This setting is intended only for use in testing, in a production or debugging environment. If enabled in a live environment, your system might be vulnerable to malicious attacks. (When disabled, displays non-comprehensive error messages generated by the authentication server on the user's logon page.)
- Max Logon Attempts Allowed
- Specifies the number of user authentication logon attempts to allow. A complete logon and
password challenge and response is considered as one attempt. Note: For a per-request policy subroutine, equivalent functionality is supported through subroutine settings.
About TACACS+ Acct
A TACACS+ Acct action adds Terminal Access Controller Access Control System (TACACS+) accounting to an access policy. The accounting service sends start and stop accounting records to the remote server.
A TACACS+ Acct action provides these configuration elements and options:
About TACACS+ Auth
A TACACS+ Acct action authenticates a user against a Terminal Access Controller Access Control System (TACACS+) server. In an access policy, an authentication action typically follows a logon action that collects credentials. A TACACS+ Acct action provides these configuration elements and options:
- AAA Server
- Specifies the TACACS+ accounting server; servers are defined in the area of the Configuration utility.
- Max Logon Attempts Allowed
- Specifies the number of user authentication logon attempts to allow. A complete logon and
password challenge and response is considered as one attempt. Note: For a per-request policy subroutine, equivalent functionality is supported through subroutine settings.
About Transparent Identity Import
A Transparent Identity Import action obtains an IP-address-to-username-mapping, if it exists, from an IF-MAP server located on the BIG-IP® system. If the mapping exists, the user identity is assumed to be known.
A Transparent Identity Import action provides two branches: Associated and fallback.





