Applies To:
Show Versions
BIG-IP APM
- 11.6.5, 11.6.4, 11.6.3, 11.6.2, 11.6.1
About SWG data for threat monitoring
After Secure Web Gateway (SWG) starts proxying web access, it provides information that you can use to monitor threats and to fine-tune URL filters and schemes. SWG provides reports, statistics, and logs. If you configure high-speed remote event logging, you have data on a remote system from which you can create your own reports.
About per-request policies and SWG logging and reports
Unless a per-request policy includes and executes a Category Lookup item, Secure Web Gateway (SWG) event logging does not occur and there is no data for reports.
About Access Policy Manager and Secure Web Gateway logs
Secure Web Gateway (SWG) supports high-speed logging and can store event logs in a local database or on a pool of remote servers (recommended). SWG event logging occurs separately from Access Policy Manager (APM) logging and from BIG-IP system logging as well.
Logs for the access policies that are part of an SWG configuration depend on APM report preference settings. Access policy logs might be in the /var/log/apm file or in a local database that APM reports uses.
About local and remote logging for Secure Web Gateway
You can log Secure Web Gateway (SWG) events either locally on the BIG-IP system or remotely, using the BIG-IP system's high-speed logging mechanism. For remote logging, the high-speed logging mechanism sends log messages to a pool of logging servers that you define. Remote logging is the recommended configuration.
For local logging, the high-speed logging mechanism stores the logs in either the Syslog or the MySQL database on the BIG-IP system, depending on a destination that you specify. The available local destinations are:
- local-db
- Causes the system to store log messages in the local MySQL database. When you choose local-db, you can view log messages in the Configuration utility.
- local-syslog
- Causes the system to store log messages in the local Syslog database. When you choose local-syslog, log messages are not available for display in the Configuration utility.
Although local logging is not recommended, you can store log messages locally on the BIG-IP system instead of or in addition to storing logs remotely.
Flowchart for local logging configuration
F5 recommends remote high-speed logging. However, you can configure local logging instead of or in addition to remote logging if you want to do so.
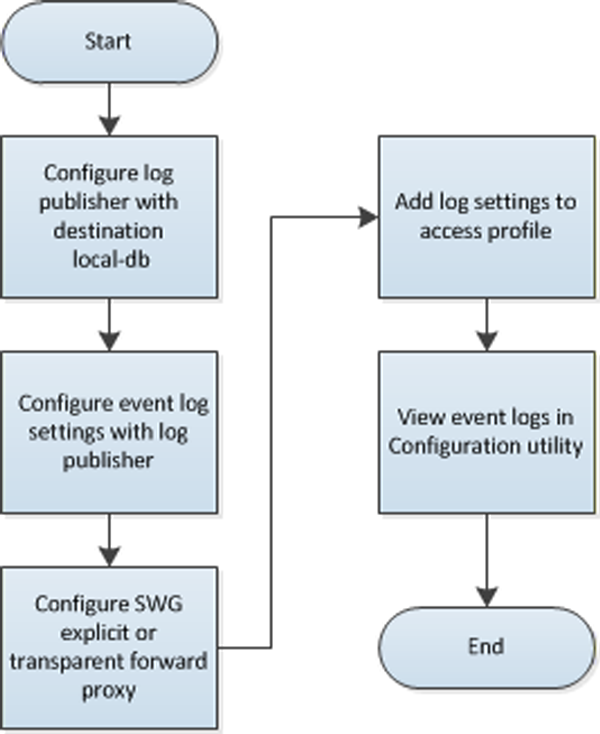 Secure Web Gateway local logging configuration
Secure Web Gateway local logging configuration
Overview: Monitoring Internet traffic and making adjustments to SWG
You can view Secure Web Gateway (SWG) statistics on the BIG-IP system and adjust SWG based on the information that you gather from reports. Charts display statistical information about web traffic on your system, including the following details:
- Actions
- Action (allowed or blocked) taken on the URL request.
- Client IP address
- IP address from which the request for the URL originated.
- Host Name
- When available, host name from which the request for the URL originated.
- Categories
- Name of the preconfigured or custom URL category into which a requested URL falls.
- URLs
- Requested URL.
- Schemes
- Name of the scheme that SWG applied to the request based on your access policy configuration.
- URL filters
- Name of the URL filter SWG applied to the request based on the schedule in the scheme.
- Security categories
- The security category of the URL if it was blocked, because it matched a security category.
- Users
- Name of the user that made the request, if available. Note: Configuring your system to identify users is optional.
- SSL bypass
- Whether the request was bypassed (yes or no). Note: Configuring your system to omit certain SSL traffic from inspection is optional.
The system updates the statistics every five minutes; you can refresh the charts periodically to see the updates. SWG provides overview charts and report charts.
- Overview
- The Secure Web Gateway overview charts summarize the top requests, such as top URLs, top categories by blocked request count, top users by permitted request count or by blocked request count, and so on. You can customize the Overview so that it shows the specific type of data you are interested in.
- Reports
- Secure Web Gateway provides two reports: All Requests and Blocked Requests. You can filter the reports to show the information that you want to see.
From the Overview or Reports, you can export data to a PDF or CSV file, or send the reports to one or more email addresses.
Task summary
About the reporting interval for charts and reports
The system updates the statistics for charts and reports at five minute intervals: at five minutes after the hour, ten minutes after the hour, and so on.
Charts and data that you export from charts reflect the publishing interval of five minutes. For example, if you request data for the time period 12:40-13:40, the data in the chart or in the file that you export is for the time period 12:35-13:35. By default, the BIG-IP system displays one hour of data.
Configuring statistics collection for reports
Examining Secure Web Gateway statistics
Focusing charts and reports on security threats
Exporting or emailing Secure Web Gateway statistics
Creating an SMTP server configuration
Chart and report drilldown paths
When drilling down to get more details from a chart or report, the data that displays depends on the starting point and the selections made while drilling down.
| Drilldown path | Alternative drilldown path |
|---|---|
|
|
| Path |
|---|
|
Overview: Configuring remote high-speed SWG event logging
You can configure the BIG-IP system to log information about Secure Web Gateway (SWG) events and send the log messages to remote high-speed log servers.
When configuring remote high-speed logging of SWG events, it is helpful to understand the objects you need to create and why, as described here:
| Object | Reason |
|---|---|
| Pool of remote log servers | Create a pool of remote log servers to which the BIG-IP system can send log messages. |
| Destination (unformatted) | Create a log destination of Remote High-Speed Log type that specifies a pool of remote log servers. |
| Destination (formatted) | If your remote log servers are the ArcSight, Splunk, or Remote Syslog type, create an additional log destination to format the logs in the required format and forward the logs to a remote high-speed log destination. |
| Publisher | Create a log publisher to send logs to a set of specified log destinations. |
| Log Setting | Create event log settings to enable logging of user-specified data, and associate a log publisher with the log settings. |
| SWG configuration | Create a configuration for SWG explicit forward proxy or transparent forward proxy. |
| Access profile | Add log settings to the access profile in the explicit forward proxy or transparent forward configuration. |
| Virtual server | In a SWG configuration, an access profile is associated with the virtual server that handles the forward proxy traffic. |
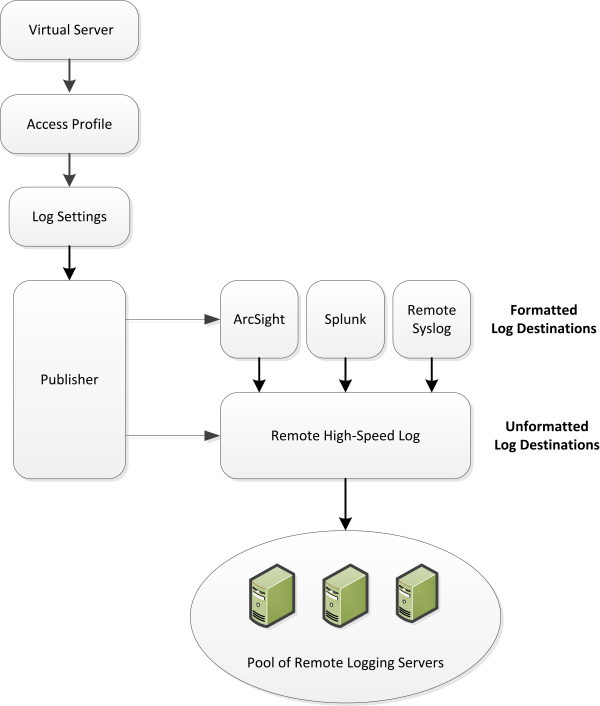 Association of remote high-speed logging configuration objects
Association of remote high-speed logging configuration objects
Task summary
Perform these tasks to configure remote high-speed SWG event logging on the BIG-IP system.Task list
Creating a pool of remote logging servers
Creating a remote high-speed log destination
Create a log destination of the Remote High-Speed Log type to specify that log messages are sent to a pool of remote log servers.
Creating a formatted remote high-speed log destination
Create a formatted logging destination to specify that log messages are sent to a pool of remote log servers, such as Remote Syslog, Splunk, or ArcSight servers.





