Applies To:
Show Versions
BIG-IP APM
- 12.0.0
Synchronizing Access Policies
Overview: Syncing access policies with a Sync-Only device group
Syncing access policies from one BIG-IP® Access Policy Manager® device to another Access Policy Manager (APM®) device, or to multiple devices in a device group allows you to maintain up-to-date access policies on multiple APM devices, while adjusting appropriate settings for objects that are specific to device locations.
To synchronize access policies between multiple devices, first you configure a Sync-Only device group, which includes the devices between which you want to synchronize access policies. Device group setup requires establishing trust relationships between devices and creating a device group. You set the devices in each group to use Automatic Sync and Full Sync, and then synchronize access policies one at a time, resolving conflicts as needed.
Task summary
Understanding policy sync for Active-Standby pairs
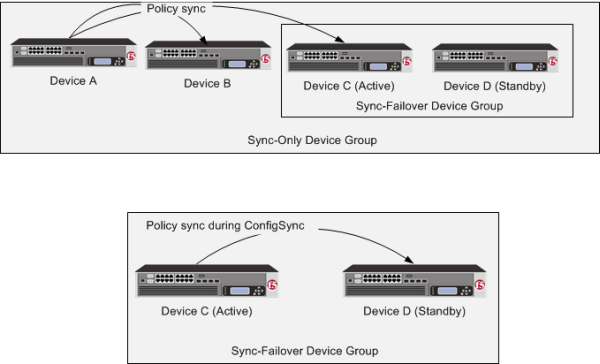
Access policy synchronization in Sync-Only and Sync-Failover device groups
Before you configure device trust
Before you configure device trust, you should consider the following:
- Only version 11.x or later systems can join the local trust domain.
- You can manage device trust when logged in to a certificate signing authority only. You cannot manage device trust when logged in to a subordinate non-authority device.
- If you reset trust authority on a certificate signing authority by retaining the authority of the device, you must subsequently recreate the local trust domain and the device group.
- As a best practice, you should configure the ConfigSync and mirroring addresses on a device before you add that device to the trust domain.
- You must configure DNS on all systems.
- You must configure NTP on all systems, preferably to the same NTP server.
Establishing device trust
Before you begin this task, verify that:
- Each BIG-IP® device that is to be part of the local trust domain has a device certificate installed on it.
- The local device is designated as a certificate signing authority.
You perform this task to establish trust among devices on one or more network segments. Devices that trust each other constitute the local trust domain. A device must be a member of the local trust domain prior to joining a device group.
By default, the BIG-IP software includes a local trust domain with one member, which is the local device. You can choose any one of the BIG-IP devices slated for a device group and log into that device to add other devices to the local trust domain. For example, devices Bigip_1, Bigip_2, and Bigip_3 each initially shows only itself as a member of the local trust domain. To configure the local trust domain to include all three devices, you can simply log into device Bigip_1 and add devices Bigip_2 and Bigip_3 to the local trust domain; there is no need to repeat this process on devices Bigip_2 and Bigip_3.
- On the Main tab, click , and then either Peer List or Subordinate List.
- Click Add.
-
Type a device IP address, administrator user name, and administrator password
for the remote BIG-IP® device with which you want to
establish trust. The IP address you specify depends on the type of BIG-IP
device:
- If the BIG-IP device is an appliance, type the management IP address for the device.
- If the BIG-IP device is a VIPRION® device that is not licensed and provisioned for vCMP®, type the primary cluster management IP address for the cluster.
- If the BIG-IP device is a VIPRION device that is licensed and provisioned for vCMP, type the cluster management IP address for the guest.
- If the BIG-IP device is an Amazon Web Services EC2 device, type one of the Private IP addresses created for this EC2 instance.
- Click Retrieve Device Information.
- Verify that the certificate of the remote device is correct.
- Verify that the management IP address and name of the remote device are correct.
- Click Finished.
Creating a Sync-Only device group for access policy sync
Synchronizing an access policy across devices initially
Configuring static resources with access policy sync
Configuring dynamic resources with access policy sync
Resolving access policy sync conflicts
About ignoring errors due to the Variable Assign agent
The Ignore errors due to Variable Assign Agent during sync setting affects system behavior only when a Variable Assign agent is included in an access policy, and the Variable Assign agent uses resources.
If you set Ignore errors due to Variable Assign Agent during sync to Yes:
- If you do not select any dynamic resources, after the policy sync completes you must create all needed resources on each target system.
- If you select the appropriate dynamic resources, after the policy sync completes, you must resolve any conflicts that exist on the target systems. If you do not select all the dynamic resources that are required, you must create them on each target system.
If you set Ignore errors due to Variable Assign Agent during sync to No:
- If you do not select any dynamic resources, an error is displayed and the policy sync does not start.
- If you select the appropriate dynamic resources, after the policy sync completes, you must resolve any conflicts that exist on the target systems.
Implementation result
To summarize, you now have synchronized access policies between devices in a sync-only device group.
Understanding sync details
On the Sync Details tab, you can see sync status for an access policy.
| Column | Description |
|---|---|
| Device | The specific device to which the access policy was synced. |
| Sync Status | One of the following:
|
| Status End Time | The time at which the last status entry completed on the specific device. |
| Sync Status Details | More information about the Sync Status for a specific device. |
Understanding sync history
On the Sync History tab, you can see the sync history for an access policy.
| Column | Description |
|---|---|
| Last sync | The last time a sync was initiated for this access policy. |
| Last Sync Status | The outcome of the last sync for this access policy. |
| Device Group | The device group to which the access policy was synced. |
| Description | A clickable icon that presents information about the sync operation for the device group. |
| Non Location Specific Objects | An access policy was created with certain resources which the sync process indicates are not location-specific, but that might in fact be location-specific on the target device. This column lists such objects, which you can then verify by checking the objects on the remote systems, and modifying if necessary. |





