Applies To:
Show Versions
BIG-IP APM
- 12.1.5, 12.1.4, 12.1.3, 12.1.2, 12.1.1, 12.1.0
Using APM as a SAML IdP (SSO portal)
Overview: Configuring BIG-IP as IdP for IdP- and SP-initiated connections
This configuration supports:
- An SSO portal on the BIG-IP® system configured as a SAML Identity Provider (IdP).
- Service providers (SPs) with the same or different requirements for assertion type and value and attributes (provided by the IdP).
- SP- and IdP-initiated connections.
About local IdP service
A SAML IdP service is a type of single sign-on (SSO) authentication service in Access Policy Manager® (APM®). When you use a BIG-IP® system as a SAML identity provider (IdP), a SAML IdP service provides SSO authentication for external SAML service providers (SPs). You must bind a SAML IdP service to SAML SP connectors, each of which specifies an external SP. APM responds to authentication requests from the service providers and produces assertions for them.
About SP connectors
A SAML service provider connector (an SP connector) specifies how a BIG-IP® system, configured as a SAML Identity Provider (IdP), connects with an external service provider.
What are the available ways I can configure a SAML SP connector?
You can use one or more of these methods to configure SAML service provider (SP) connectors in Access Policy Manager®.
- From metadata - Obtain a metadata file from the vendor and import it into Access Policy Manager. The advantage to this method is that the vendor provides the majority of all required data, including certificates. You can complete the configuration by simply typing a unique name for the SP connector, a very few additional required fields, and browsing to and importing the file. Access Policy Manager then configures the SP connector.
- From template - Use templates that Access Policy Manager provides for some vendors; for
example, Google. The advantages to this method are that:
- Most required data is included in the template
- Additional required data is minimal. You can obtain it and certificates from the vendor
- Custom - Obtain information from the vendor and type the settings into the Configuration utility. To use this method, you must also obtain certificates from the vendor and import them into the BIG-IP® system. Use this method when a metadata file or a template for an SP connector is not available.
Task summary
Setting up a BIG-IP® system as a SAML identity provider (IdP) system involves two major activities:
- First, you set up connection from the BIG-IP system to the external SAML service providers (SPs)
- Then, you set up connection from the external SAML SPs to the BIG-IP system
Task list
Flowchart: Configuration to support a SAML SSO portal
This flowchart illustrates the process for configuring a BIG-IP® system as a SAML identity provider (IdP) that provides an SSO portal.
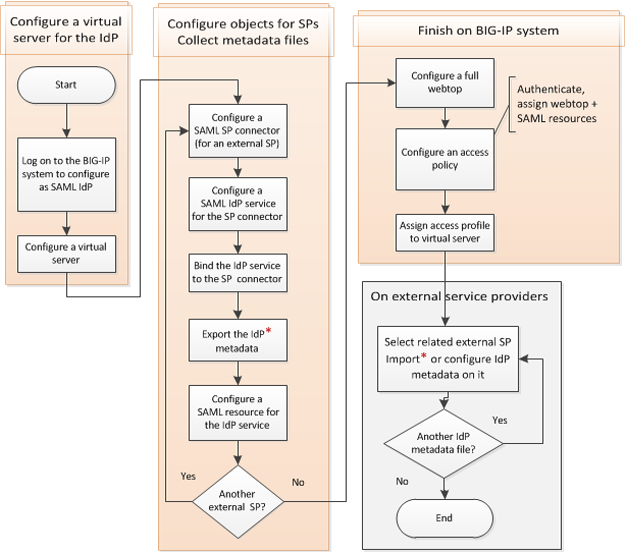
Creating a virtual server for a BIG-IP (as SAML IdP) system
Configuring an artifact resolution service
Configuring SAML SP connectors
Configuring a SAML IdP service for one SP connector
Binding a SAML IdP service to one SP connector
Exporting SAML IdP metadata from APM
Configuring a SAML resource and attaching a SAML IdP service
Configuring a full webtop
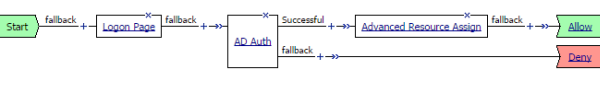
Configuring an access policy for a SAML SSO portal
Simple access policy for access to services on SAML service providers
Verifying log settings for the access profile
Adding the access profile to the virtual server
You associate the access profile with the virtual server so that Access Policy Manager® can apply the profile to incoming traffic.
Adding IdP metadata from APM to external SAML SPs
- Import the SAML IdP metadata file that you exported from APM for the SAML IdP service that this service provider uses.
- Or take information from the SAML IdP metadata file that you exported
from APM for the SAML IdP service and add it to the service provider using
the vendor's interface. Pay particular attention to the values for entityID,
AssertionConsumerService, SingleSignOnService, and the certificate.Note: Regardless of the value of entityID in the metadata file, type an SSO URI that consists of the virtual server host and /saml/idp/profile/redirectorpost/sso. For example, if the host virtual server is https://Bigip-idp, type: https://Bigip-idp/saml/idp/profile/redirectorpost/sso





